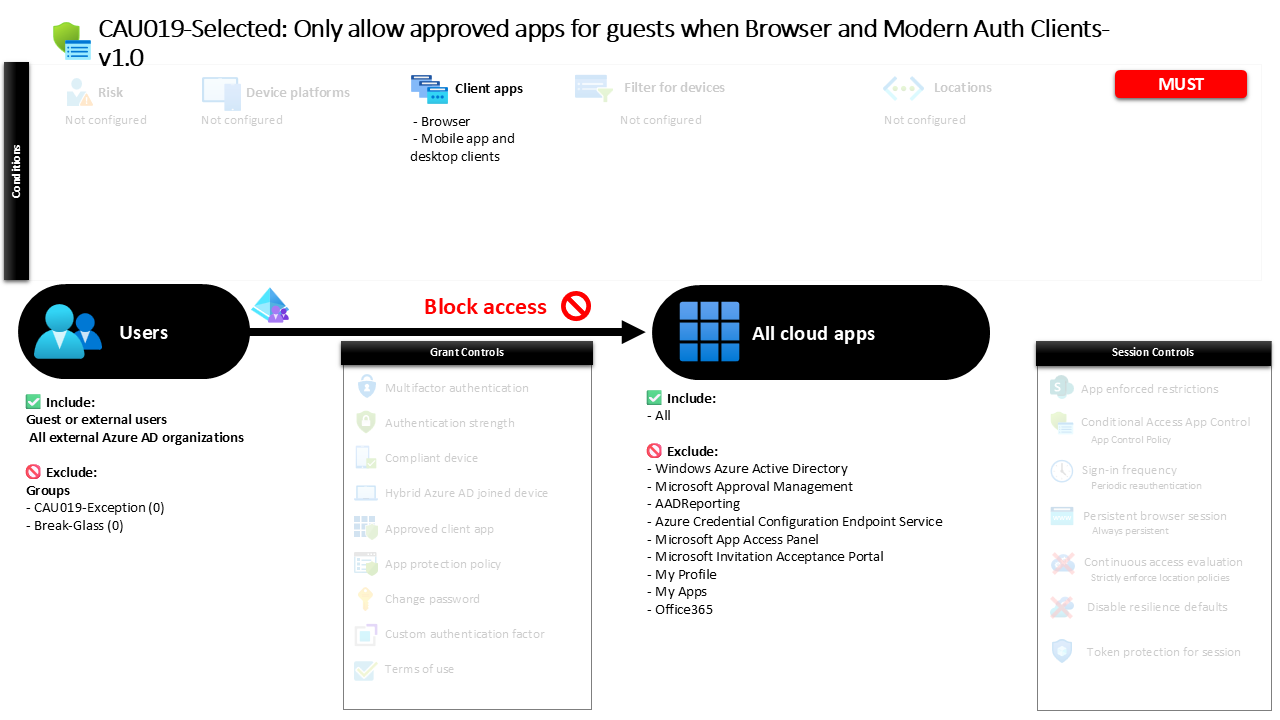
Conditional Access Guest App Restrictions CAU019-Selected: Only allow approved apps for guests when Browser and Modern Auth Clients
Introduction
Conditional Access guest app restrictions are designed to solve a common security challenge in modern collaboration environments. Organizations frequently invite external partners, vendors, and consultants to collaborate using Microsoft cloud services. While this collaboration is powerful, it also creates a risk surface where external identities might access applications or data that were never intended for guest users. Without guardrails, a guest account could potentially authenticate to a wide range of cloud services.
This Conditional Access policy addresses that challenge by placing boundaries around what external identities can reach once they sign in. Instead of allowing guest users to interact with every connected application, the policy evaluates their sign-in and actively blocks access to most services. Only specific applications remain available.
The design reflects a careful balance between collaboration and control. External identities are still able to participate where needed, but their access is constrained to a defined set of allowed services, which is a foundational principle of secure identity architecture.
This Policy in One Line
This policy blocks external and guest users from accessing most cloud applications when signing in through browsers or modern authentication clients, ensuring only approved services remain reachable.
What This Conditional Access Policy Does
The core intention of this Conditional Access design is straightforward: prevent guest identities from accessing the broader application ecosystem of the tenant. When a sign-in request is initiated by an external user, Conditional Access evaluates the request against the policy and determines whether access should be allowed or blocked.
In this configuration, the policy targets all cloud applications by default. This means the Conditional Access engine assumes that external users should not interact with most services unless those services are explicitly carved out of the policy scope. When a guest attempts to authenticate to a cloud application, Conditional Access evaluates the request and applies a block decision.
However, several applications are intentionally left outside the scope of the restriction. These exclusions represent services that organizations typically allow guest users to access in order to enable collaboration scenarios. By structuring the policy in this way, the organization creates a clear boundary: guest users are permitted to interact with specific collaboration platforms, while everything else remains off limits.
This approach reflects a defensive access model where external identities operate within carefully controlled access corridors rather than broad application visibility.
Who the Policy Applies To
The policy targets external identities rather than internal users. Specifically, it applies to several categories of guest and external accounts commonly used in Microsoft Entra collaboration scenarios.
When a user authenticates and the identity is recognized as a guest or external account, Conditional Access includes that identity within the scope of the policy evaluation. This applies across multiple collaboration models, including traditional guest accounts and cross-tenant collaboration users.
In practical terms, this means that when an external partner signs in to access shared resources, their authentication request is treated differently from that of an internal employee. Conditional Access recognizes the identity type and applies the restrictions defined in the policy.
There are also groups that are excluded from the policy scope. Organizations commonly use such exclusion groups to support controlled exception management. These groups often allow administrators to temporarily permit external users who require broader access for legitimate scenarios such as troubleshooting, migration support, or special collaboration projects. By managing exceptions through groups, security teams maintain oversight while avoiding permanent configuration changes.
What Apps and Services the Policy Protects
From an application perspective, the policy takes a broad security stance. Conditional Access treats the entire cloud application catalog as protected resources.
When an external user attempts to access an application, the policy evaluates that request against the defined scope. Because the policy includes the entire set of cloud applications, the default outcome for guest users is denial of access.
However, certain services are intentionally excluded from this protection boundary. These exclusions represent applications that are commonly required for collaboration scenarios. For example, organizations often allow guest users to interact with services that enable document sharing, communication, or project collaboration.
By excluding only a limited set of services, the design ensures that external users can participate in collaborative workflows while still preventing them from reaching administrative tools, internal business applications, or other sensitive resources.
This model effectively implements an allowlist approach for guest access. Instead of trying to restrict access application by application, the organization blocks everything by default and allows only the services that are explicitly intended for external collaboration.
Platforms, Devices, and Client Apps in Scope
The policy focuses specifically on how external users connect to cloud applications. In this configuration, Conditional Access evaluates sign-ins that originate from two common authentication paths: browser-based access and modern authentication clients.
Browser sessions represent the most common method for guest users to interact with shared content. When a partner opens a collaboration link, accesses a shared document, or signs into a web-based application, the authentication flow typically begins through a browser session. This policy ensures those sessions are evaluated for guest restrictions.
Modern authentication clients are also included. These are applications such as desktop or mobile productivity tools that use modern identity protocols to connect to Microsoft services. By including these clients, the policy prevents guest users from bypassing restrictions through desktop applications or mobile apps.
No device platform restrictions are defined in this policy. As a result, the access decision focuses primarily on identity type and client application behavior rather than device characteristics.
How Access Is Decided
The decision logic within this policy is intentionally simple and decisive. Once Conditional Access determines that the sign-in originates from a guest or external identity and that the targeted application falls within the protected scope, the access request is blocked.
The block control acts as a hard stop in the authentication process. Unlike policies that require additional verification steps such as multifactor authentication, this policy does not offer remediation paths. If the request matches the conditions defined in the policy, access to the application is denied.
This type of enforcement is often used for boundary protection scenarios. Instead of prompting users to prove their identity further, the system simply prevents access to services that are not intended for external collaboration.
The result is a predictable security posture where guest identities are automatically constrained to a narrow set of allowed services.
What the User Experience Looks Like During Sign-In
From the user perspective, the experience depends on which application the guest attempts to access. When a guest signs in to a service that remains available for collaboration, the authentication process proceeds normally.
However, when the same guest attempts to access an application outside that approved scope, Conditional Access intervenes during the sign-in evaluation. The authentication attempt is halted and the user receives a message indicating that access to the resource is not permitted.
This behavior often appears when external users attempt to explore additional services beyond the collaboration environment they were invited to use. The policy ensures those exploratory sign-ins do not result in unintended access.
The user experience therefore reinforces the intended collaboration boundary. Guests can work within the approved environment but cannot expand their access footprint.
Why This Policy Matters for Security and the Business
External collaboration is essential for modern organizations, but it also introduces identity exposure. Every guest account represents an external authentication path into the tenant.
Without restrictions like this policy, guest identities could authenticate against a wide array of internal services. Even if those services ultimately deny access through application-level permissions, the mere ability to attempt authentication increases the attack surface.
By blocking guest access to most cloud applications at the Conditional Access layer, the organization significantly reduces this exposure. External identities remain useful for collaboration, yet they cannot interact with unrelated services.
This improves the overall identity security posture while still enabling the productivity benefits of cross-organization collaboration.
Is This a Foundational or Must-Have Policy?
Policies that restrict guest application access are widely considered foundational in a mature Conditional Access architecture.
Organizations increasingly rely on external identities for project collaboration, supplier access, and partner integration. As these external relationships grow, so does the importance of clearly defining where guest identities can and cannot go within the tenant.
A policy like this establishes those boundaries early in the authentication process. Instead of relying solely on application permissions, the Conditional Access layer enforces a tenant-wide rule that prevents unintended service access.
For environments that heavily use guest collaboration, this type of control is often part of the baseline Conditional Access policy set.
Important Design Choices and Things to Notice
One notable aspect of the policy design is the decision to include all cloud applications as the default target. This simplifies the access model significantly. Instead of trying to identify every sensitive application that should be restricted, the policy assumes that guest users should not access most services unless specifically allowed.
Another important design element is the explicit allowance of certain applications through exclusions. This reflects a practical understanding of collaboration requirements. Guest users typically need access to a small set of collaboration platforms, and these services are intentionally preserved.
The policy also targets both browser sessions and modern authentication clients. This ensures that guest users cannot bypass the restriction by switching from a browser interface to a desktop or mobile application.
Together, these design choices create a consistent and predictable access boundary for external identities.
Conditional Access Design Principles Behind This Policy
Several Conditional Access design principles are visible in this policy architecture.
The first is the principle of least privilege. External identities receive access only to the services required for collaboration, rather than broad access to the tenant’s application ecosystem.
The second principle is perimeter reduction. By blocking most applications at the Conditional Access layer, the organization reduces the number of potential authentication paths that external users can attempt.
The third principle is centralized enforcement. Instead of relying on individual application settings, Conditional Access acts as the gatekeeper that consistently evaluates sign-ins before application access occurs.
These principles help ensure that external collaboration remains secure without becoming overly complex to manage.
Final Thoughts
Guest collaboration is an essential capability in modern cloud environments, but it must be carefully governed. Conditional Access guest app restrictions provide a clear mechanism for defining where external identities can operate.
By blocking access to most applications while allowing only specific collaboration services, this policy establishes a well-defined boundary for guest users. External partners can still contribute and participate, yet the organization maintains control over the broader application landscape.
In practice, this type of policy helps security teams maintain confidence that external identities cannot unintentionally expand their reach within the tenant. It represents a thoughtful application of Conditional Access principles to real-world collaboration scenarios.