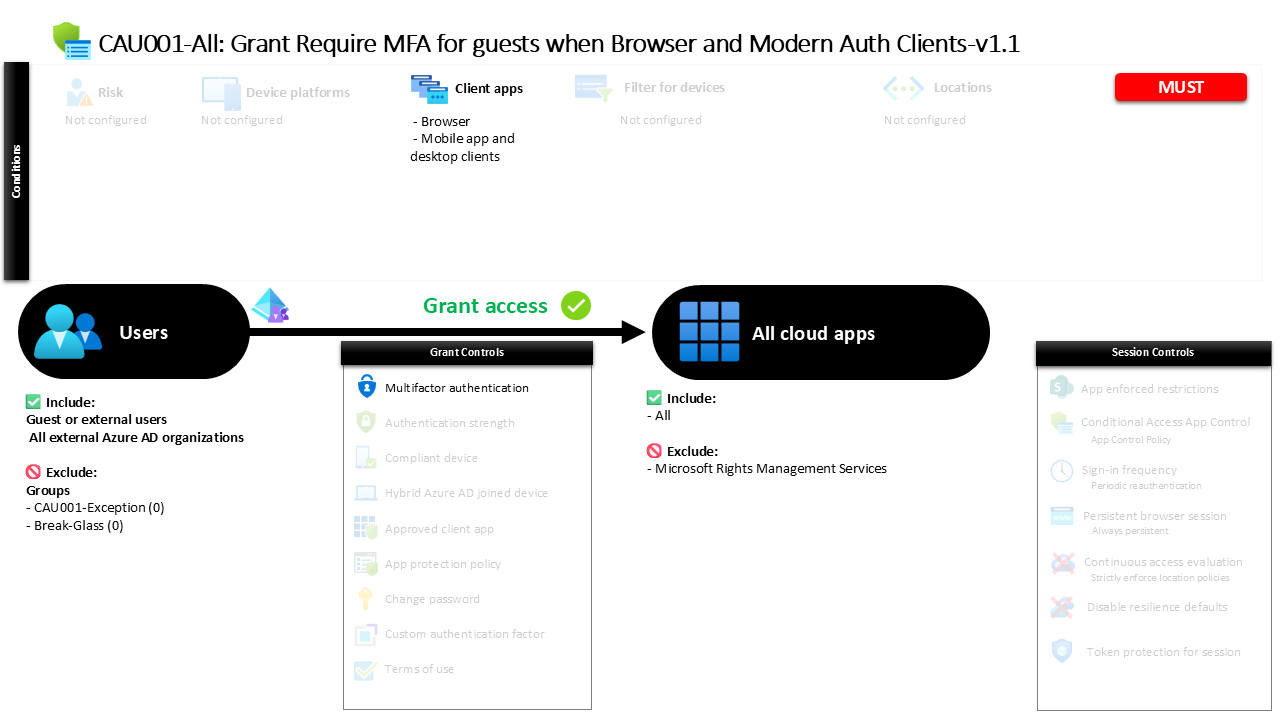
Conditional Access MFA for Guests CAU001-All Grant Require MFA for guests when Browser and Modern Auth Clients
Introduction
Conditional Access MFA for Guests addresses a very common security challenge in modern collaboration environments. Organizations increasingly work with partners, consultants, and suppliers who access internal resources through guest or external identities. These identities often originate from other tenants or identity providers, which means the organization hosting the resources does not control the authentication posture of those accounts. Without additional verification, this can introduce a blind spot where external identities access sensitive workloads with weaker authentication protections.
Conditional Access MFA for Guests is designed to close that gap. The policy ensures that whenever external users access organizational cloud resources through interactive clients such as browsers or modern authentication applications, an additional identity verification step is required. Instead of relying solely on the authentication performed by the external identity provider, the organization adds its own security checkpoint.
By introducing this layer of verification at the Conditional Access level, the environment establishes a clear security expectation for all guest access: collaboration is allowed, but it must always be verified through strong identity authentication.
This Policy in One Line
Conditional Access MFA for Guests requires external users to complete multi-factor authentication when accessing cloud applications through browsers or modern authentication clients.
What This Conditional Access Policy Does
Conditional Access MFA for Guests introduces a security checkpoint during the authentication process for all external identities attempting to access organizational cloud applications. When a sign-in occurs, Microsoft Entra evaluates the identity type associated with the session and determines whether the user qualifies as a guest or other external identity category.
If the user falls into one of the supported external identity classifications, the policy becomes relevant during the authentication evaluation. Conditional Access then examines how the user is accessing the application. Because the configuration specifically evaluates browser sessions and modern authentication clients, the policy focuses on the most common interactive access paths used for productivity workloads.
Once the conditions are met, access to the application is not immediately granted. Instead, the user must complete multi-factor authentication before the sign-in process is allowed to continue. This step introduces an additional verification signal confirming that the person signing in truly controls the external identity being used.
From a security architecture perspective, the design ensures that collaboration with external identities remains possible while still enforcing strong authentication assurance for access to organizational resources.
Who the Policy Applies To
Conditional Access MFA for Guests focuses specifically on external identities interacting with the organization’s environment. These identities include multiple forms of guest and external collaboration accounts used for B2B collaboration, cross-tenant connectivity, and service provider access scenarios.
During the sign-in evaluation process, Microsoft Entra identifies whether the user belongs to one of the supported external identity categories. These categories cover the most common guest and partner collaboration patterns used in Microsoft Entra environments. As a result, the policy ensures that external users accessing internal resources are treated differently from internal employees.
At the same time, the configuration allows for operational flexibility. Some organizations maintain dedicated groups that represent controlled exceptions, allowing administrators to temporarily bypass policies for troubleshooting, onboarding scenarios, or specialized collaboration cases. In mature environments, these groups are often managed through approval workflows or time-based access processes so that exceptions remain visible and auditable.
This approach balances two competing needs. On one side, the organization enforces strong authentication for the broad set of external identities. On the other side, administrators retain a structured mechanism for handling legitimate exceptions without weakening the overall Conditional Access architecture.
What Apps and Services the Policy Protects
Conditional Access MFA for Guests protects access to the organization’s cloud application environment broadly rather than focusing on a single service. When Microsoft Entra evaluates the sign-in attempt, the policy considers access requests directed toward the tenant’s cloud applications and applies the authentication requirement across that landscape.
This design is common in environments where external collaboration may occur across multiple workloads. Guest users may interact with collaboration platforms, shared resources, document repositories, or other cloud-hosted applications provided through the organization’s tenant. Applying the policy across the cloud application surface ensures consistent authentication protection regardless of which workload is being accessed.
At the same time, one specific service is excluded from the policy scope. Exclusions like this are sometimes used to maintain compatibility with specialized authentication flows or platform services that require a different security treatment. By carefully excluding a single service while protecting the broader application landscape, the design maintains security coverage without disrupting required system behavior.
This model reflects a common Conditional Access principle: broad protection combined with carefully managed exceptions to preserve functionality.
Platforms, Devices, and Client Apps in Scope
Conditional Access MFA for Guests evaluates access attempts based on the type of client application used during sign-in. In this configuration, the policy specifically focuses on browser-based sessions and modern authentication clients.
Browsers represent a major access pathway for guest collaboration. External partners frequently access shared resources such as documents or collaboration portals through web interfaces. Because browser sessions often originate from unmanaged devices outside the organization’s control, verifying the identity of the person signing in becomes particularly important.
Modern authentication clients represent the other significant access method. These include applications that use modern authentication protocols to connect directly to cloud workloads. By including both browser and modern client scenarios, the policy captures nearly all interactive access patterns used by external collaborators.
Notably, the configuration does not restrict access based on device platform or device state. The evaluation focuses entirely on the identity type and authentication pathway rather than the device itself. This design prioritizes identity verification as the primary security control, ensuring that regardless of where the sign-in originates, the external user must prove their identity through multi-factor authentication.
How Access Is Decided
When Conditional Access MFA for Guests evaluates a sign-in attempt, Microsoft Entra processes the authentication request through its policy evaluation engine. This engine checks multiple conditions to determine whether the policy should apply to the session.
The evaluation begins by identifying the user type. If the identity qualifies as a guest or external user category, the policy becomes a candidate for enforcement. Next, the sign-in client is evaluated to determine whether the request originates from a browser or a modern authentication application.
If both conditions are satisfied, the policy introduces an additional requirement before access can be granted. The external user must complete multi-factor authentication as part of the sign-in process. Only after this requirement is successfully satisfied does the authentication flow continue toward application access.
This evaluation process ensures that authentication strength is applied consistently for external identities. Instead of relying solely on credentials provided by an external identity provider, the organization requires its own verification step, strengthening the trust level of the session before any application access occurs.
What the User Experience Looks Like During Sign-In
From the perspective of an external collaborator, the Conditional Access MFA for Guests policy appears as an additional identity verification step during the sign-in process. The user begins by accessing a shared resource or application link, which initiates authentication through their external identity provider.
After the initial credential validation completes, Microsoft Entra evaluates the Conditional Access policies assigned to the session. Because the user is recognized as an external identity accessing applications through a supported client type, the policy introduces a second authentication step.
At this point, the user is prompted to complete multi-factor authentication. The exact verification method depends on the authentication methods available to the external identity, but the goal remains the same: confirm that the person initiating the session truly controls the account being used.
Once the additional verification is completed successfully, the sign-in continues and access to the requested application is granted. For the user, the process typically adds only a brief step to the login experience while significantly increasing the security assurance of the session.
Why This Policy Matters for Security and the Business
Conditional Access MFA for Guests plays a crucial role in protecting collaborative environments where external identities interact with internal resources. In modern organizations, guest access is no longer an exception but a normal part of daily operations. Partners contribute to projects, consultants review documentation, and suppliers interact with shared collaboration spaces.
However, these identities exist outside the organization’s direct control. Their authentication strength depends on policies implemented by external identity providers, which may not align with the organization’s internal security standards.
By requiring multi-factor authentication for guest access, the organization establishes its own trust boundary. Even if the external identity provider allows weaker authentication methods, the Conditional Access policy introduces an additional verification step before access is granted.
From a business perspective, this approach allows organizations to maintain open collaboration without sacrificing security. External collaboration remains frictionless enough for productivity, while the organization ensures that sensitive workloads remain protected by strong identity verification.
Is This a Foundational or Must-Have Policy?
Conditional Access MFA for Guests is widely considered a foundational policy in modern Microsoft Entra security architecture. Any environment that enables external collaboration introduces potential identity risk, and strong authentication controls are the primary method for mitigating that risk.
Because external identities originate outside the organization’s administrative control, relying solely on their original authentication context can create security gaps. Requiring multi-factor authentication ensures that every external session meets a minimum security standard before access to cloud resources is permitted.
For this reason, many Conditional Access design frameworks recommend implementing guest MFA enforcement as part of the baseline security posture. It complements other identity protection policies and forms a critical layer in a broader zero trust identity model.
In practice, this policy often appears early in Conditional Access deployments because it delivers immediate security improvements with minimal operational disruption.
Important Design Choices and Things to Notice
Several design choices stand out in Conditional Access MFA for Guests. The most notable is the decision to apply the authentication requirement broadly across cloud applications rather than targeting a small set of workloads. This ensures that external identities cannot bypass security protections simply by accessing a different application within the tenant.
Another important design detail is the focus on interactive authentication pathways. By targeting browsers and modern authentication clients, the policy covers the most common collaboration scenarios while avoiding unnecessary complexity for non-interactive service flows.
The configuration also incorporates a structured exception mechanism through exclusion groups. Organizations commonly use these groups to manage approved exceptions, allowing administrators to handle unique operational cases without weakening the security posture applied to the broader user population.
Together, these design choices reflect a practical Conditional Access approach: enforce strong authentication broadly, support collaboration securely, and maintain operational flexibility through controlled exception management.
Conditional Access Design Principles Behind This Policy
Conditional Access MFA for Guests reflects several core design principles that appear in mature identity security architectures. The first principle is identity verification over device trust. Because guest users frequently connect from devices outside organizational control, the most reliable security signal is strong authentication rather than device compliance.
The second principle is universal protection for external identities. By applying the policy across the cloud application environment, the configuration ensures that external users encounter consistent authentication expectations regardless of which resource they access.
The third principle is layered identity security. Multi-factor authentication acts as an additional identity assurance step layered on top of the initial authentication performed by the external identity provider.
These principles align closely with zero trust identity models, where authentication strength becomes a critical signal used to determine whether access should be allowed.
Final Thoughts
Conditional Access MFA for Guests represents a simple but powerful identity security control. In environments where collaboration with external partners is routine, verifying those identities through multi-factor authentication becomes essential for protecting organizational resources.
The policy ensures that external users can continue to collaborate through familiar tools and workflows while still meeting a clear authentication standard defined by the organization. By focusing on identity verification rather than device restrictions or complex conditions, the design delivers strong protection without introducing unnecessary operational friction.
In a broader Conditional Access strategy, policies like this establish the baseline trust model for external identities. Collaboration remains open, but every external session must prove its legitimacy before access is granted.