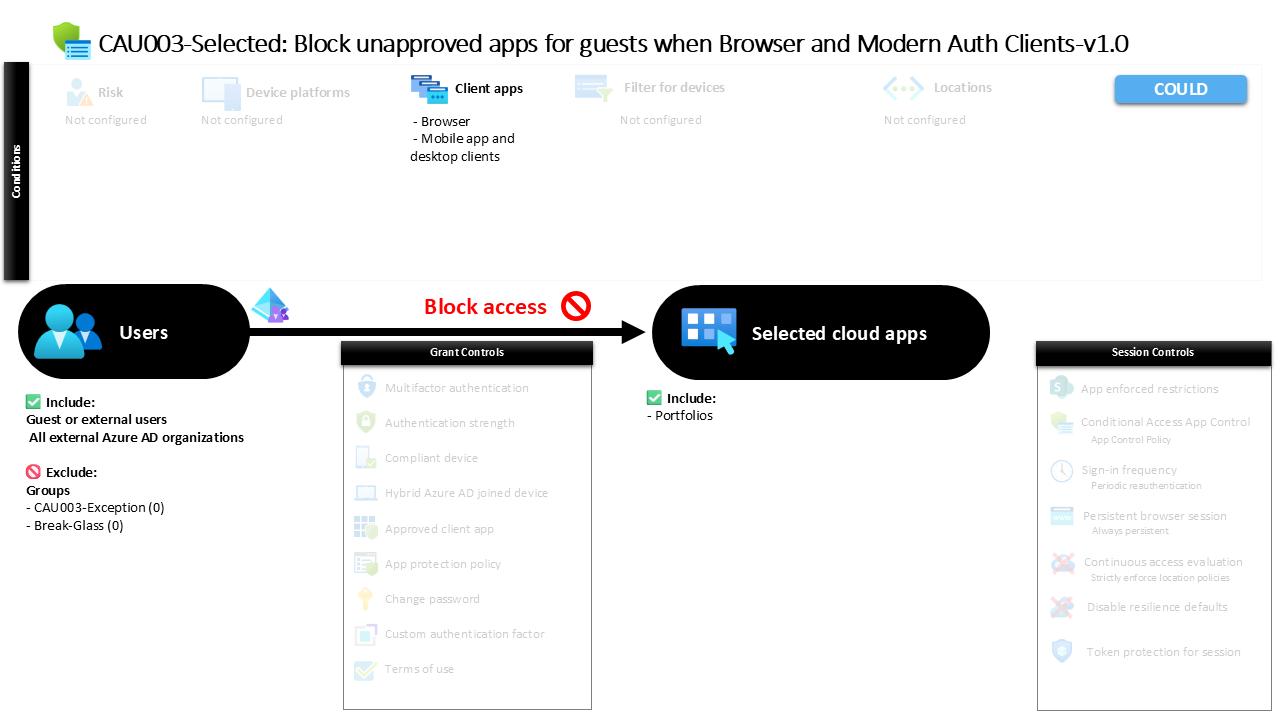
Conditional Access Guest App Blocking CAU003-Selected: Block unapproved apps for guests when Browser and Modern Auth Clients
Introduction
Conditional Access guest app blocking addresses a common security challenge in modern collaboration environments. Organizations frequently invite external partners, vendors, and consultants into their Microsoft Entra environments. These guest identities enable productive collaboration, but they also introduce a new layer of risk. External users often operate from unmanaged devices, unfamiliar networks, and identities that the organization does not fully control.
This is where Conditional Access guest app blocking becomes an important security control. Instead of allowing guest identities unrestricted access to sensitive cloud resources, organizations can define exactly where and how external users interact with specific applications. This policy demonstrates a defensive approach that evaluates guest sign-ins and blocks access when certain client access patterns are used.
Rather than treating external identities the same as internal users, the design intentionally separates their access experience. By controlling browser and modern authentication client access paths, the organization ensures that guest collaboration happens only through approved and controlled methods. In a broader Conditional Access architecture, this type of policy acts as a boundary that protects critical applications while still supporting external collaboration.
This Policy in One Line
This Conditional Access guest app blocking policy blocks guest and external users from accessing a specific cloud application when the sign-in originates from browser-based or modern authentication clients.
What This Conditional Access Policy Does
The design intention behind this policy is straightforward: restrict access to a specific application when external identities attempt to sign in using browser sessions or modern authentication clients. In Conditional Access, policies evaluate several factors during authentication, including the identity type, application being accessed, and the client used to initiate the session.
In this case, the policy targets a defined cloud application and evaluates whether the user signing in belongs to a guest or external identity category. If that condition is met and the sign-in attempt originates from either a browser session or a modern authentication client such as desktop or mobile applications, the policy applies its configured access decision.
The configured decision in this policy is to block access entirely. Instead of allowing the session to continue with additional verification steps, the request is stopped before the application session can be established. This approach is commonly used when an organization wants to strictly limit how external identities interact with certain resources.
From a design perspective, the policy establishes a clear security boundary. It ensures that external identities cannot use common client entry points to reach the protected application.
Who the Policy Applies To
The policy specifically targets guest and external user identities. Conditional Access supports a broad classification of external identities, and this policy includes multiple types of external collaboration accounts within its scope. These identities typically originate from partner organizations, external tenants, or federated collaboration relationships.
During sign-in, Conditional Access evaluates whether the identity belongs to one of these guest or external categories. If the user matches that classification, the policy becomes eligible for enforcement. This ensures that internal employees are not affected by the rule while external identities are evaluated against the restriction.
Two exclusion groups are configured as part of the design. In Conditional Access architectures, exclusion groups are commonly used to support controlled exceptions. Security teams may temporarily allow specific external collaborators to bypass certain restrictions when business needs require it. These exceptions are typically managed through approval workflows or time-based membership so that the security boundary remains intact while operational flexibility is maintained.
This approach reflects a common Conditional Access design principle: enforce strict controls by default while allowing controlled and auditable exceptions when necessary.
What Apps and Services the Policy Protects
The policy protects a specific cloud application configured within the Conditional Access application targeting scope. Conditional Access evaluates the application requested during sign-in and determines whether the policy should apply based on that target.
When a guest identity attempts to authenticate to the protected application, the policy becomes active in the access evaluation process. This allows the organization to implement application-specific access boundaries instead of applying identical restrictions across all cloud services.
Targeting individual applications is a powerful design strategy. Some resources may support external collaboration safely, while others contain sensitive data or administrative capabilities that require tighter restrictions. By isolating a specific application in the policy scope, the organization creates a focused protection layer without disrupting legitimate external collaboration elsewhere.
This application-level targeting reflects a mature Conditional Access strategy where access decisions are tailored to the sensitivity and purpose of each service.
Platforms, Devices, and Client Apps in Scope
This policy focuses on the client application used during sign-in rather than the operating system or device platform. Conditional Access evaluates whether the authentication request originates from either a browser session or a modern authentication client such as desktop or mobile applications.
When a guest identity attempts to access the protected application through a web browser, the policy becomes applicable because the client type matches the configured condition. Similarly, if the sign-in occurs through a modern authentication client, such as an application using modern authentication protocols, the same evaluation applies.
No device state, device compliance, or platform restrictions are defined in this configuration. The policy therefore focuses exclusively on the method used to access the application rather than the device itself.
From a security design perspective, this approach emphasizes controlling entry points into the application. By identifying the client types commonly used for direct application access, the policy can enforce a strict access boundary for external identities.
How Access Is Decided
Conditional Access evaluates sign-in events using a layered decision model. When a guest user attempts to access the protected application, the system first verifies whether the identity falls into the external user category defined by the policy.
Next, Conditional Access examines the client type used during authentication. If the sign-in originates from a browser or modern authentication client, the condition matches the policy configuration. At this point, the policy becomes active and proceeds to evaluate the configured grant control.
The grant control defined in this policy is a block decision. This means that once the conditions are satisfied, the sign-in request is denied before access to the application is granted.
Blocking access at this stage prevents the session from progressing into the application environment. The result is a clear enforcement boundary that stops unauthorized client access patterns for external identities.
What the User Experience Looks Like During Sign-In
From the perspective of an external collaborator, the experience is immediate and visible during the sign-in process. The guest user attempts to open the protected application using either a browser or a client application that relies on modern authentication.
The authentication process begins normally. The identity is validated, and Conditional Access evaluates the sign-in context. As soon as the system detects that the user is classified as an external identity and that the client type matches the policy conditions, the policy enforcement is triggered.
Instead of continuing to the application session, the sign-in attempt is stopped. The user receives a message indicating that access is blocked according to the organization’s access policy.
This behavior reinforces the concept that access decisions are evaluated in real time. The application itself is never reached because the decision occurs during the identity verification stage of the sign-in process.
Why This Policy Matters for Security and the Business
External collaboration is essential in modern organizations, but unmanaged access paths can quickly become a security concern. Guest identities may originate from environments that the organization does not control, and they may attempt to access applications from devices or client applications that bypass established governance models.
Conditional Access guest app blocking addresses this challenge by restricting specific access paths. Instead of allowing unrestricted entry points into the protected application, the organization defines exactly how external identities may interact with it.
This approach helps reduce exposure to accidental data access, uncontrolled integration points, and unexpected application usage patterns. At the same time, it ensures that internal users and approved collaboration channels continue to function without disruption.
From a business perspective, the policy demonstrates how security and collaboration can coexist. External access remains possible where appropriate, but the organization maintains control over the environments and methods used to access sensitive services.
Is This a Foundational or Must-Have Policy?
This type of policy is typically considered a targeted protective control rather than a universal foundational policy. Foundational Conditional Access policies often focus on identity protection, baseline authentication requirements, and broad security enforcement across all applications.
In contrast, this design focuses on a specific application and a specific user category. It introduces a restriction that is applied only when certain client access methods are used by external identities.
Policies like this are commonly introduced as part of a mature Conditional Access architecture. Once baseline security controls are established, organizations begin refining their policies to address application-specific risks and collaboration scenarios.
In that sense, this policy represents a more advanced layer of Conditional Access governance.
Important Design Choices and Things to Notice
Several design decisions stand out in this policy. The first is the explicit targeting of guest and external identities. This separation ensures that internal users are not unintentionally affected by restrictions intended for external collaboration.
Another important design choice is the use of client application conditions rather than device conditions. Instead of evaluating device trust or compliance, the policy simply blocks access when the application is accessed through browser or modern authentication clients.
The inclusion of exclusion groups is also noteworthy. In Conditional Access design, these groups allow organizations to handle exceptional situations without weakening the core security rule. Temporary collaboration scenarios, emergency access, or approved integrations can be managed through controlled group membership.
Together, these design choices reflect a thoughtful balance between strict security boundaries and operational flexibility.
Conditional Access Design Principles Behind This Policy
At its core, this policy reflects several key Conditional Access design principles. The first is identity-based segmentation. By separating external identities from internal users, the organization ensures that different risk levels are handled appropriately.
Another principle visible in the design is application-centric protection. Instead of applying identical restrictions across all services, the organization selectively protects specific applications based on their risk profile and collaboration requirements.
The policy also demonstrates the principle of controlled access paths. By restricting specific client access methods, the organization reduces the number of possible entry points into the protected application.
Finally, the presence of exclusion groups illustrates the principle of operational flexibility. Security policies remain strict, but exceptions can be granted in a structured and auditable way.
Final Thoughts
Conditional Access guest app blocking is an example of how organizations can apply precise controls to external collaboration scenarios. Instead of treating guest identities as identical to internal users, the policy enforces boundaries that reflect the different risk profile associated with external access.
By targeting a specific application and blocking access when browser or modern authentication clients are used, the policy ensures that external identities cannot access the service through these common entry points. The result is a clearly defined access boundary that protects sensitive resources while maintaining flexibility through controlled exceptions.
In a broader Microsoft Entra security strategy, policies like this help organizations move toward a layered and contextual access model. Every sign-in is evaluated, every access path is considered, and security decisions are made dynamically based on identity and context.