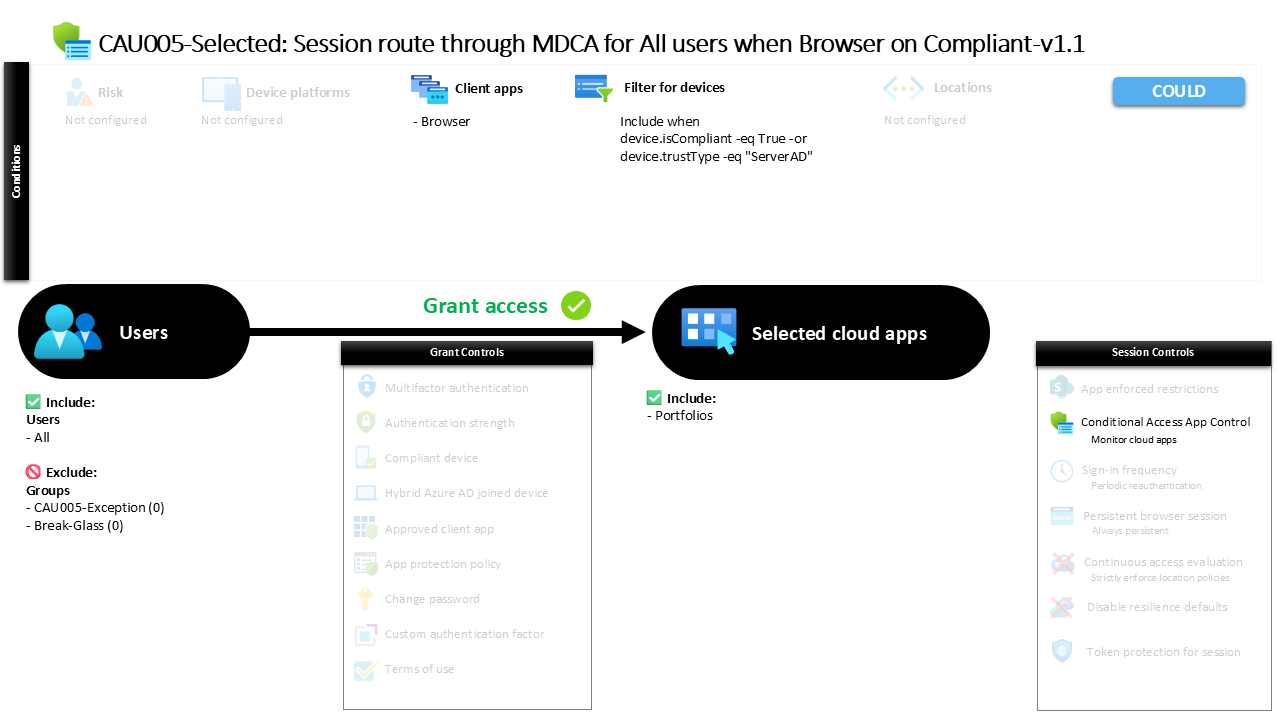
Conditional Access Browser Session Monitoring CAU005 Selected Session route through MDCA for All users when Browser on Compliant
Introduction
Conditional Access browser session monitoring becomes important when organizations want visibility into how users interact with sensitive cloud services. Many security incidents do not start with a failed login. They begin after a legitimate sign-in, when an authenticated session is used in unexpected ways. Security teams often want the ability to observe those sessions without immediately blocking the user.
This policy addresses that challenge by routing browser-based sessions through Microsoft Defender for Cloud Apps so activity can be monitored. Instead of making a hard access decision, the configuration allows the session to proceed while giving the security platform visibility into how the session behaves.
The design reflects a common Zero Trust approach. Access is permitted when the device meets defined trust conditions, but the session is still evaluated by a monitoring layer. This allows organizations to detect suspicious behavior early while keeping productivity uninterrupted.
This Policy in One Line
Conditional Access browser session monitoring routes browser sessions from trusted devices through Microsoft Defender for Cloud Apps so user activity can be observed and analyzed.
What This Conditional Access Policy Does
This policy introduces session-level visibility for browser access to a specific cloud application. When a user signs in through a web browser, Conditional Access evaluates the request and determines whether the device meets the defined trust criteria. If those criteria are satisfied, the session is routed through Microsoft Defender for Cloud Apps.
Rather than enforcing restrictions or blocking actions, the configuration enables monitoring. This allows the session to be inspected for patterns that could indicate risky behavior, such as unusual activity during the session or unexpected interaction with application data.
The design reflects a staged security approach. Organizations often begin with monitoring before introducing stricter controls. By observing real user behavior first, security teams gain insight into how applications are used and where potential risks might exist. That knowledge helps inform future Conditional Access policies that may eventually enforce stronger session protections.
Who the Policy Applies To
The policy targets all users who sign in to the protected application through a browser. This broad scope ensures that session monitoring applies consistently across the organization whenever the defined conditions are met.
However, the configuration includes exclusion groups. In many Conditional Access designs, exclusion groups serve an operational purpose rather than weakening security. Organizations often maintain dedicated exception groups so access can be temporarily adjusted during troubleshooting, application testing, or emergency scenarios.
These groups typically operate under controlled approval processes or time-based access workflows. By structuring exceptions this way, administrators avoid directly excluding individual users and instead manage exceptions in a transparent and auditable manner.
This design keeps the main policy simple and predictable while still allowing the organization to handle exceptional scenarios without modifying the core security configuration.
What Apps and Services the Policy Protects
The policy focuses on a single cloud application rather than applying to every service in the tenant. This targeted design suggests that the organization wants enhanced visibility for activity within a particular workload.
Conditional Access frequently protects applications that contain sensitive data or where monitoring user behavior provides valuable security insight. By focusing on one application, administrators can study real session activity without introducing complexity across the entire environment.
This targeted approach is especially useful during early stages of session monitoring adoption. Organizations can validate that the monitoring workflow functions as expected, evaluate the telemetry produced by Defender for Cloud Apps, and confirm that normal user activity remains unaffected.
Once the monitoring process proves reliable, similar session visibility policies can be extended to additional applications.
Platforms, Devices, and Client Apps in Scope
This policy specifically evaluates browser-based access. When a user signs in through a web browser, the request becomes eligible for the session monitoring workflow.
Conditional Access identifies the client application type and applies the policy only when the sign-in originates from a browser session. Other client types such as mobile or desktop applications are not evaluated by this configuration.
Device trust is also part of the evaluation process. The policy includes devices that meet defined trust characteristics, meaning the device must either be marked as compliant or recognized as a domain-joined system. These signals allow Conditional Access to determine whether the device belongs to a managed or trusted environment.
By focusing on browser access from trusted devices, the policy ensures that monitoring occurs in scenarios where users interact directly with application data through the web interface.
How Access Is Decided
During sign-in, Conditional Access evaluates several factors before determining how the session should proceed. The system first checks whether the user falls within the policy scope and whether the request originates from a browser.
Next, the device attributes are evaluated. If the device is considered compliant or recognized as a trusted domain-joined system, it satisfies the device trust condition defined by the policy.
Once these conditions are met, access to the application proceeds. At that point, Conditional Access applies a session control that routes the connection through Microsoft Defender for Cloud Apps.
Instead of altering authentication requirements or blocking access, the policy activates a monitoring pathway. The session remains fully functional, but activity within that session becomes visible to the security monitoring platform.
This layered evaluation model reflects how Conditional Access combines identity signals, device posture, and session controls to shape access behavior.
What the User Experience Looks Like During Sign-In
From the user’s perspective, the sign-in experience remains straightforward. A user opens the application in a web browser and signs in with their normal credentials. If the device meets the defined trust criteria, the login proceeds without interruption.
Behind the scenes, Conditional Access attaches the session monitoring control. The user continues interacting with the application normally, but their session traffic flows through Microsoft Defender for Cloud Apps.
Because the configuration focuses on monitoring rather than restriction, users typically do not notice any difference in functionality. Documents, dashboards, and application features behave exactly as expected.
Meanwhile, the security platform gains visibility into the session. Activity patterns can be analyzed for anomalies, giving security teams insight into how applications are used and where potential threats may appear.
Why This Policy Matters for Security and the Business
Modern cloud security requires visibility beyond authentication. Once a user successfully signs in, traditional security controls often lose sight of what happens next.
Conditional Access browser session monitoring addresses that visibility gap. By routing browser sessions through a monitoring platform, organizations gain the ability to observe behavior within the application environment.
This insight allows security teams to identify suspicious patterns that might otherwise remain hidden. For example, unusual activity sequences, abnormal interaction patterns, or other indicators of misuse can be detected within an active session.
For the business, the benefit is balance. Users maintain seamless access to the tools they rely on, while security teams gain deeper insight into how those tools are used.
Is This a Foundational or Must-Have Policy?
This policy typically falls into the category of an advanced Conditional Access capability rather than a foundational control. Basic Conditional Access strategies often begin with identity verification requirements, device compliance checks, and restrictions on legacy authentication.
Session monitoring introduces an additional layer that focuses on behavior within authenticated sessions. It does not directly prevent access but enhances security awareness by observing how applications are used.
Organizations often deploy these monitoring policies after their core Conditional Access framework is already in place. Once identity and device trust signals are established, session monitoring becomes a powerful tool for identifying subtle threats.
In that sense, this policy complements foundational Conditional Access controls by extending visibility beyond the initial sign-in decision.
Important Design Choices and Things to Notice
Several design choices in this policy reveal the intent behind its configuration. The first is the use of browser-based access as the trigger condition. Web sessions often expose the richest user interaction data, making them ideal for monitoring scenarios.
Another notable element is the device trust filter. By including compliant devices or trusted domain-joined systems, the policy ensures monitoring occurs in managed environments where user identity is already strongly validated.
The session control itself is also significant. Rather than enforcing restrictions, the configuration enables monitoring mode within Microsoft Defender for Cloud Apps. This suggests the organization is observing behavior and collecting insights before deciding whether stronger session controls may be necessary in the future.
These choices indicate a thoughtful security design that prioritizes visibility and learning before introducing enforcement.
Conditional Access Design Principles Behind This Policy
The policy reflects several important Conditional Access design principles. One of the most visible is layered security. Instead of relying solely on authentication decisions, the design extends protection into the session layer where user behavior unfolds.
Another principle is progressive security maturity. Monitoring policies often represent an intermediate stage in a Conditional Access journey. Organizations observe how users interact with applications before determining whether additional restrictions should be introduced.
The use of device trust signals also aligns with Zero Trust thinking. Access decisions are influenced not just by identity but also by the security posture of the device used during sign-in.
Together, these principles demonstrate how Conditional Access can move beyond simple login protection and evolve into a dynamic framework that continuously evaluates risk throughout the user session.
Final Thoughts
Conditional Access browser session monitoring offers organizations a valuable way to understand what happens after authentication succeeds. While identity verification remains essential, real security insight often comes from observing user activity inside the application.
By routing browser sessions through Microsoft Defender for Cloud Apps, this policy introduces a monitoring layer that operates quietly in the background. Users maintain a seamless experience while security teams gain deeper visibility into session behavior.
This approach reflects a mature Conditional Access strategy. Rather than relying solely on hard access decisions, the policy introduces intelligence into the session itself. Over time, the insights gained from monitoring can guide the evolution of stronger controls, helping organizations build a security model that is both adaptive and resilient.