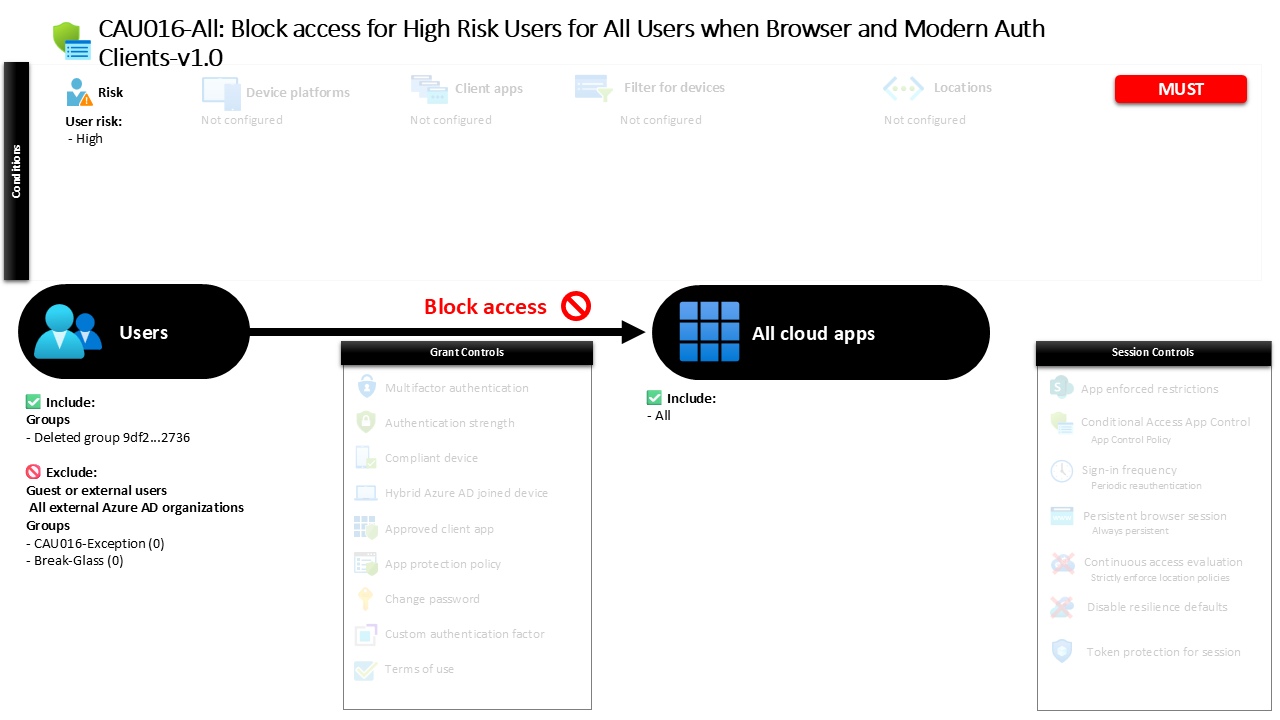
Conditional Access Block for High-Risk Users CAU016-All: Block access for High Risk Users for All Users when Browser and Modern Auth Clients
Introduction
Conditional Access high risk user block policies exist for a simple but critical reason. When an identity becomes compromised, every second of continued access increases the potential damage. Attackers who gain control of an account often move quickly, attempting to access email, cloud storage, collaboration tools, and administrative portals before the breach is detected.
Conditional Access high risk user block policies are designed to interrupt that moment. Instead of allowing a risky identity to continue authenticating, Microsoft Entra ID evaluates the identity risk level during the sign-in process. If the risk reaches the highest threshold, access is immediately denied.
This approach reflects a core Zero Trust principle: compromised identities must be contained as quickly as possible. By evaluating identity risk signals before granting access, organizations ensure that suspicious accounts cannot continue operating normally in the environment.
The policy examined in this article focuses specifically on users identified as high risk and prevents them from accessing any cloud application when that risk condition is detected.
This Policy in One Line
This Conditional Access policy blocks access to all cloud applications whenever Microsoft Entra ID determines that a user account carries a high identity risk level.
What This Conditional Access Policy Does
This Conditional Access policy introduces a strict containment mechanism for identities that are flagged as high risk. When Microsoft Entra ID Identity Protection determines that a user account has reached the highest risk level, the policy immediately denies access to cloud applications.
The key design intention here is simple. A high user risk signal typically indicates that the account may already be compromised. Signals that contribute to this risk evaluation can include unusual sign-in patterns, credential exposure, impossible travel activity, or other behavioral indicators detected by Microsoft’s identity protection systems.
Instead of attempting to verify the user or allowing conditional remediation, this configuration enforces a full access block. Once the risk condition is met, authentication is halted before any application session is established.
This type of design is often used as a protective barrier in modern identity security architecture. It ensures that accounts identified as highly suspicious cannot continue interacting with business systems until administrators investigate and the identity risk is resolved.
Who the Policy Applies To
The policy targets users through a specific identity group rather than applying globally to every account in the tenant. This design allows organizations to apply the control to a defined set of internal users while maintaining flexibility in how identity protection policies are rolled out.
At the same time, external identities are excluded from the policy scope. Guest users and other externally connected identities are therefore evaluated outside the boundaries of this particular control.
The configuration also includes exclusion groups. In most enterprise environments, these groups exist to support controlled exceptions such as emergency access accounts, operational break-glass identities, or service accounts that require special handling.
This design approach reflects a common Conditional Access principle. Security controls should apply broadly to users while still allowing carefully managed exceptions that support operational continuity.
By structuring the scope in this way, the policy ensures that high-risk internal users are contained while allowing administrators to maintain safe and controlled recovery paths when needed.
What Apps and Services the Policy Protects
The scope of this policy covers every cloud application connected to Microsoft Entra ID. When the identity risk condition is triggered, the block decision applies regardless of which application the user attempts to access.
This design is intentional. When an identity reaches a high risk level, the assumption is that the attacker could attempt to access any connected resource. Email systems, collaboration platforms, administrative portals, and custom enterprise applications may all become potential targets.
By applying the control to all cloud applications, the organization eliminates any opportunity for attackers to bypass the protection through an unprotected workload.
This comprehensive scope aligns with modern Conditional Access architecture practices. Instead of securing applications individually, identity risk is treated as a universal security signal that applies across the entire identity ecosystem.
Once the identity risk threshold is reached, access to every integrated service is prevented until the risk condition is resolved.
Platforms, Devices, and Client Apps in Scope
This policy does not differentiate between operating systems, device states, or endpoint types. Instead, the configuration evaluates all client application types when determining whether the policy should apply.
In practical terms, this means the policy evaluates sign-ins regardless of how the user attempts to authenticate. Browser sessions, desktop applications, mobile clients, and other modern authentication mechanisms are all subject to the same access decision.
The absence of platform filtering reflects a deliberate design choice. When an identity becomes highly risky, the threat does not depend on the device used during authentication. Attackers may attempt access through multiple channels in rapid succession.
By keeping the scope broad and independent of device characteristics, the policy ensures that the identity risk signal remains the primary factor in the access decision.
This approach reinforces the Zero Trust principle that identity integrity should always take precedence over device context when determining whether access should be granted.
How Access Is Decided
Conditional Access evaluates this policy during the authentication process by examining the identity risk level associated with the user account. Microsoft Entra ID continuously calculates this risk score using behavioral analytics, threat intelligence, and sign-in anomaly detection.
When a user begins the sign-in process, Conditional Access checks whether the identity risk level has been classified as high. If that condition is met, the policy immediately applies its access control.
The configured control is straightforward. Instead of requiring additional verification or session restrictions, the policy simply blocks access.
This decision point occurs before the user can establish an authenticated session with the target application. As a result, the user is prevented from reaching the application environment entirely.
From a security design perspective, this type of control is intended to act as an immediate containment mechanism. It ensures that compromised identities cannot continue interacting with sensitive resources while security teams investigate the underlying risk signals.
What the User Experience Looks Like During Sign-In
From the user’s perspective, the experience occurs during the normal authentication flow. The user begins the sign-in process by entering their credentials or initiating authentication through a supported client application.
During this process, Microsoft Entra ID evaluates the account’s risk posture. If the identity risk level has already been classified as high, the Conditional Access evaluation triggers the block decision.
Instead of proceeding to application access, the authentication process stops and the user is informed that access cannot be granted. The user cannot proceed further into the application session.
This behavior is deliberate. High risk signals suggest that the identity may already be compromised, so the policy avoids remediation steps that could allow continued activity during the investigation.
By interrupting the sign-in immediately, the system prevents potentially malicious activity from progressing beyond the authentication stage.
Why This Policy Matters for Security and the Business
Identity compromise remains one of the most common entry points for security incidents. Stolen credentials, phishing campaigns, and password reuse attacks continue to target user accounts as a primary attack vector.
A Conditional Access high risk user block policy addresses this challenge by turning identity protection signals into immediate enforcement actions. Instead of waiting for manual investigation, the platform automatically blocks access when a serious threat indicator appears.
This capability significantly reduces the time attackers have to exploit compromised identities. Even if credentials have already been obtained, the account cannot be used to access business systems once the risk threshold is reached.
For organizations, this provides a powerful containment layer. Security teams gain valuable time to investigate the account, initiate recovery procedures, and reset credentials without worrying that attackers are actively operating inside the environment.
Is This a Foundational or Must-Have Policy?
Policies that block access for high-risk users are widely considered foundational components of modern Conditional Access architectures. They represent one of the most direct ways to translate identity protection insights into actionable security enforcement.
Unlike policies that focus on device posture or location awareness, this control targets the integrity of the identity itself. When the identity signal indicates a potential compromise, access is denied regardless of the user’s device, location, or authentication method.
Because identity compromise is such a high-impact threat scenario, many security frameworks recommend enforcing strong responses to high-risk identities.
Blocking access at this stage ensures that compromised accounts cannot continue operating in the environment until security teams verify the user’s identity and restore account trust.
In practice, this type of policy acts as a final safety net that prevents the most dangerous identity scenarios from escalating further.
Important Design Choices and Things to Notice
Several design decisions in this policy reveal the underlying security strategy. The first is the focus on the highest identity risk level rather than broader risk categories. This ensures that the block response is reserved for the most severe threat scenarios.
Another notable choice is the application scope covering every cloud application. Instead of protecting specific services, the policy treats identity compromise as a universal risk across the entire digital environment.
The policy also evaluates all client application types. By avoiding restrictions tied to device platforms or authentication methods, the design eliminates potential gaps that attackers might attempt to exploit.
Finally, the presence of controlled exclusions reflects operational awareness. Security policies must protect systems without creating situations where administrators lose the ability to recover accounts or maintain critical operations.
Together, these decisions show a policy designed for strong containment while still supporting practical identity management processes.
Conditional Access Design Principles Behind This Policy
At its core, this policy reflects several key Conditional Access design principles used in modern identity security architectures.
The first principle is risk-based access control. Instead of relying solely on static rules such as location or device compliance, the policy responds to real-time risk signals generated by Microsoft Entra ID Identity Protection.
The second principle is identity containment. When an account becomes highly suspicious, the safest action is to halt access entirely until administrators confirm the user’s legitimacy.
Another principle visible in this design is universal coverage. Because the policy applies to all applications and client types, it eliminates opportunities for attackers to pivot into less protected services.
Finally, the policy demonstrates layered identity protection. Conditional Access works alongside identity risk detection to ensure that risk signals automatically translate into meaningful enforcement decisions.
Final Thoughts
Conditional Access high risk user block policies play a crucial role in modern identity security strategies. They ensure that when Microsoft Entra ID identifies a potentially compromised account, the response is immediate and decisive.
Rather than relying on manual intervention, the system automatically denies access before attackers can interact with applications or data. This approach dramatically reduces the window of opportunity for malicious activity.
Combined with identity investigation and remediation workflows, this type of policy forms an essential containment layer within Microsoft Entra ID security architecture.
By enforcing strict controls when identity risk reaches the highest level, organizations ensure that compromised accounts are stopped at the door, protecting both users and business systems from further harm.