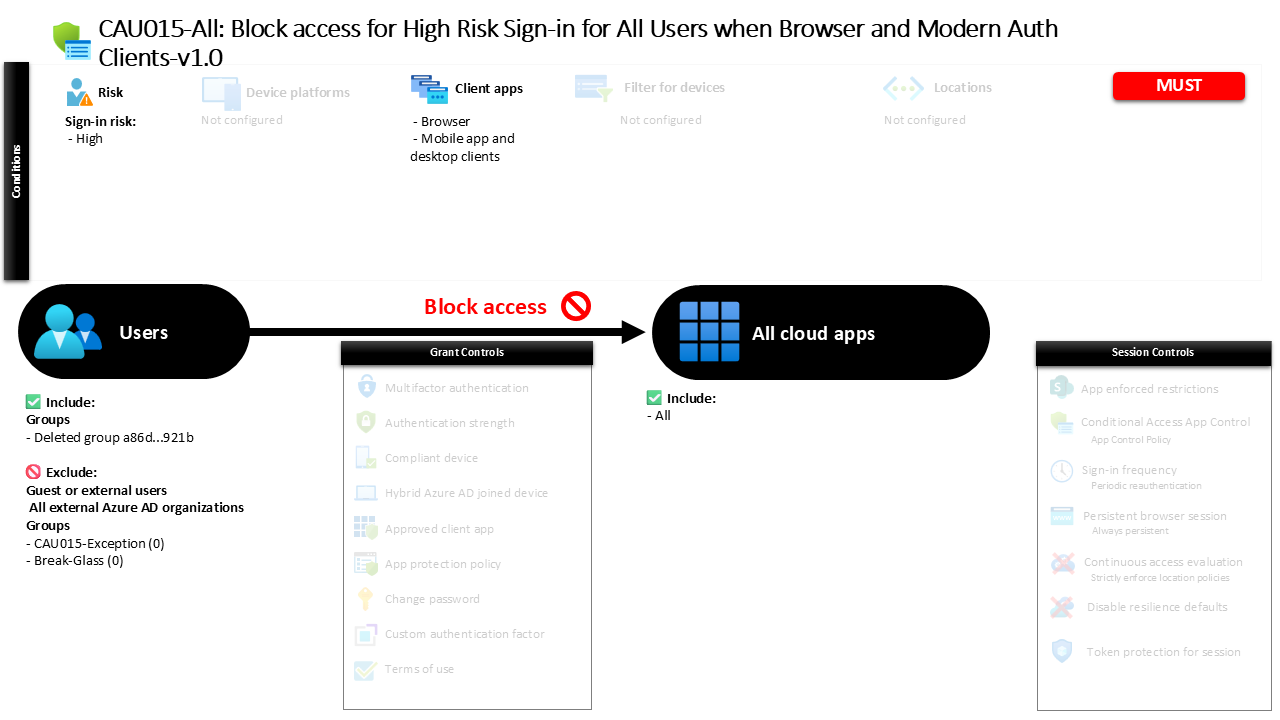
Conditional Access High Risk Sign-In Block CAU015-All: Block access for High Risk Sign-in for All Users when Browser and Modern Auth Clients
Introduction
Conditional Access high risk sign-in block is designed to address one of the most dangerous moments in identity security: when a sign-in attempt shows strong indicators of compromise. In modern identity systems, attackers rarely break in through infrastructure first. Instead, they attempt to sign in using stolen credentials, automated attacks, or tokens acquired through phishing. Microsoft Entra ID continuously analyzes these sign-in attempts and assigns a risk level based on signals such as unfamiliar locations, suspicious behavior patterns, or known attack indicators. When the system determines that a sign-in carries a high level of risk, allowing access could mean granting an attacker immediate entry to corporate resources.
This policy exists to prevent that scenario. Rather than attempting to step up authentication or apply additional verification, the design simply stops the sign-in when the risk signal is severe. By blocking access at the identity layer, the organization ensures that a potentially compromised identity cannot reach any application protected by Microsoft Entra ID. This is a clear example of a defensive identity strategy where risk signals drive immediate containment.
This Policy in One Line
This policy blocks access to all applications whenever a sign-in attempt is detected as high risk and originates from browser sessions or modern authentication clients.
What This Conditional Access Policy Does
The central function of this policy is straightforward: when Microsoft Entra ID detects a sign-in with a high risk score, access is blocked before the user can reach protected services. Sign-in risk represents the probability that a specific authentication attempt is malicious. Microsoft evaluates this risk using machine learning models and threat intelligence, analyzing signals such as anonymous IP usage, unfamiliar sign-in patterns, leaked credential detection, or behavior consistent with automated attacks.
When the evaluated risk reaches the high level, the policy activates. At that moment the Conditional Access engine evaluates the incoming authentication request and immediately denies access rather than allowing the authentication process to continue. Because the grant control in the policy explicitly blocks access, no additional authentication step is attempted.
The result is decisive protection. Instead of attempting to remediate the situation in real time, the organization treats high-risk sign-ins as potential account compromise events and prevents them from reaching applications altogether.
Who the Policy Applies To
This policy targets a defined group of internal users within the organization. Conditional Access evaluates membership in that group when determining whether the policy should apply to a specific sign-in attempt.
External users are excluded from the policy scope. This means that guest identities and other external collaboration identities are not evaluated by this specific rule when they sign in. The design keeps the focus on protecting internal workforce identities, which typically hold the most valuable access within the tenant.
The configuration also includes multiple exclusion groups. In practice, organizations often use such groups to manage controlled exceptions through formal approval workflows or time-based access scenarios. For example, break-glass administrative accounts or emergency recovery identities are commonly placed in exclusion groups to ensure that access to the tenant remains possible during security incidents.
This approach balances strong protection with operational resilience, which is a key principle in mature Conditional Access design.
What Apps and Services the Policy Protects
The scope of application protection in this policy is intentionally broad. The policy applies to all applications integrated with Microsoft Entra ID authentication. Whenever a user attempts to sign in to any protected service, the Conditional Access engine evaluates the risk level of the sign-in before access is granted.
By targeting all applications rather than a subset, the policy eliminates the possibility that an attacker could pivot to a less protected service after a risky sign-in is detected. Whether the user attempts to access Microsoft 365 services, enterprise applications, or custom cloud applications integrated with the identity platform, the same rule applies.
This design reflects a common best practice in Conditional Access architecture. Risk-based controls are most effective when applied consistently across the identity surface. A compromised identity should not have a path to any application once a high-risk sign-in has been detected.
Platforms, Devices, and Client Apps in Scope
The policy evaluates sign-ins originating from two major client categories: web browsers and modern authentication clients used by mobile applications and desktop software.
Browser sessions represent one of the most common entry points for identity attacks. Phishing campaigns frequently target browser-based authentication because users are accustomed to entering credentials through web prompts. Monitoring browser activity therefore plays a critical role in detecting suspicious sign-in attempts.
Modern authentication clients include applications such as mobile productivity apps and desktop clients that authenticate through the modern OAuth-based authentication framework. These clients communicate directly with Microsoft Entra ID using secure authentication flows, but they are still subject to identity risk evaluation during sign-in.
By including both client categories, the policy ensures that risk-based blocking occurs regardless of how the authentication request is initiated. Whether the sign-in originates from a web browser or a mobile application, the same protection applies.
How Access Is Decided
Access decisions in this policy revolve around one condition: sign-in risk level. When a user attempts to authenticate, Microsoft Entra ID analyzes the request using its identity protection system and assigns a risk classification.
If the risk level is evaluated as high, the Conditional Access policy is triggered. At that moment the grant control defined in the policy instructs the access engine to block the authentication attempt.
Because the policy contains a block control rather than a remediation step such as multi-factor authentication, the decision path is simple. Once the condition is met, access is denied immediately.
This model is intentionally strict. High-risk sign-ins are treated as potential account compromise indicators, and the safest response is to prevent access until the situation can be investigated or remediated.
What the User Experience Looks Like During Sign-In
From the user’s perspective, the experience occurs during the authentication phase. A user attempts to sign in to a cloud service using either a browser or a modern client application. Microsoft Entra ID evaluates the authentication request and detects signals that classify the sign-in as high risk.
When the Conditional Access policy processes that evaluation, the authentication process stops. Instead of receiving access to the requested service, the user is informed that access has been blocked due to security policies.
In a real-world scenario, this often indicates that the system detected behavior inconsistent with the user’s normal sign-in patterns. Security teams typically investigate these events as potential credential compromise attempts, verifying whether the activity originated from the legitimate user or from an attacker attempting to use stolen credentials.
Why This Policy Matters for Security and the Business
Identity is now the primary security perimeter for most organizations. Applications, services, and data increasingly rely on identity providers rather than network boundaries for access control. When attackers obtain credentials, they can bypass many traditional defenses simply by signing in as legitimate users.
This policy directly addresses that risk. By blocking high-risk sign-ins, the organization prevents potentially compromised identities from accessing sensitive services. Instead of relying solely on password resets or user awareness, the system enforces automatic containment based on risk analysis.
For the business, this translates into stronger protection against account takeover, data exposure, and unauthorized access to enterprise systems. The policy also demonstrates a proactive security posture where identity risk signals are used to enforce real-time defensive controls.
Is This a Foundational or Must-Have Policy?
This policy represents a foundational identity protection control in modern Conditional Access architecture.
Risk-based blocking of high-risk sign-ins is widely recommended because it provides immediate containment for the most suspicious authentication events. When identity protection systems classify a sign-in as high risk, the probability of malicious activity is already significant. Allowing access under those conditions introduces unnecessary exposure.
For that reason, many organizations implement this type of rule early in their Conditional Access deployment. It forms part of the baseline identity defense strategy alongside multi-factor authentication and device-based access policies.
Important Design Choices and Things to Notice
One notable design decision in this policy is the use of a direct block rather than a remediation control. Instead of requesting additional authentication factors when a risky sign-in occurs, the policy stops the authentication attempt entirely.
This reflects a clear security philosophy. When risk reaches the highest level, the safest response is not to challenge the user further but to deny access until the identity can be verified through administrative or automated recovery processes.
Another important observation is the broad application scope. Because the policy applies to all applications, it prevents attackers from attempting alternative entry points after a risky sign-in is detected.
Finally, the presence of defined exclusion groups shows that operational considerations were included in the design. Controlled exception handling ensures that emergency access accounts remain available if required.
Conditional Access Design Principles Behind This Policy
Several key Conditional Access design principles are visible in this configuration.
First is risk-driven access control. Instead of applying static rules based only on location or device type, the policy reacts dynamically to identity risk signals generated by Microsoft Entra ID.
Second is the concept of identity containment. When risk signals indicate potential compromise, the safest course of action is to stop the sign-in immediately rather than attempting remediation within the same authentication flow.
Third is consistency across the application landscape. By protecting all applications, the policy eliminates gaps where attackers might otherwise gain access after a risky authentication attempt.
Together, these principles demonstrate a mature Conditional Access strategy that treats identity risk signals as authoritative indicators for access decisions.
Final Thoughts
Conditional Access high risk sign-in block policies represent a powerful line of defense in modern identity security. They transform threat intelligence and behavioral analysis into real-time access decisions that stop attackers before they reach applications.
In environments where credential theft, phishing, and automated login attacks are increasingly common, this type of policy provides an essential safeguard. When Microsoft Entra ID determines that a sign-in carries a high level of risk, the safest response is simple: do not allow the session to proceed.
By implementing this design, organizations ensure that their identity platform actively defends against the most suspicious authentication attempts, reinforcing the broader strategy of Zero Trust access control.