Empowering your Digital Transformation
Migrate with Confidence
Seamless transitions — on-prem, cloud, or hybrid — with zero disruption.
Our proven approach combines strategic planning, best-practice execution, and continuous support to minimize downtime and deliver a smooth, efficient migration every step of the way.
Be Secure
In today’s threat landscape, cyberattacks like ransomware are not a matter of if, but when. Confidence in your organization’s security isn’t a luxury — it’s a necessity.
With the right tools and real-time visibility, you gain the awareness and control needed to stay one step ahead
Training
Empowering your team starts with the right training.
With today’s tools evolving fast, regular workshops and deep-dive sessions ensure your staff stay sharp, confident, and ready. Ongoing education isn’t optional — it’s essential.
Migrate with Confidence
Transitions with zero disruption from on-prem, cloud, or hybrid.
With a proven approach and the combination of robust planning, best-practice execution, and continuous support to minimize downtime and ensure a smooth, efficient migration journey.xt content
Be Secure
In today’s threat landscape, cyberattacks like ransomware are not a matter of if, but when. Confidence in your organization’s security isn’t a luxury — it’s a necessity.
With the right tools and real-time visibility, you gain the awareness and control needed to stay one step ahead
Training
Using today’s tools, regular training or workshop can keep your staff up to date, providing the training they need is key, with comprehensive deep dive session or a workshop on tools
Seamless Endpoint Migration
Whether you’re moving to the cloud, merging organizations, or consolidating AD environments, endpoint migration can be a complex undertaking for IT teams. Yet the goal always remains the same: transition devices from one environment to another with minimal disruption, robust security, and smooth operational continuity.
Seamless Endpoint Migration
Whether you’re moving to the cloud, merging organizations, or consolidating AD environments, endpoint migration can be a complex undertaking for IT teams. Yet the goal always remains the same: transition devices from one environment to another with minimal disruption, robust security, and smooth operational continuity.

News

Conditional Access Explained: Why It Matters
Conditional Access explained from a real-world perspective. Learn why policies are designed this way and how they protect identities in practice.
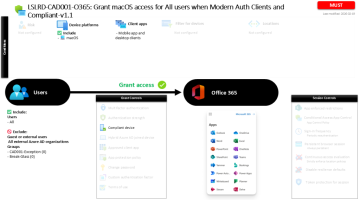
Conditional Access macOS Compliance for Office 365
Conditional Access macOS compliance policy protecting Office 365 by allowing access only from compliant macOS devices using modern authentication clients.
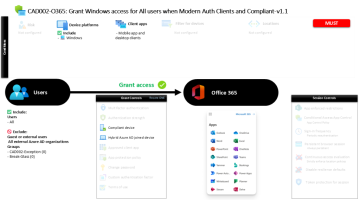
Conditional Access Windows Device Trust
Conditional Access Windows device trust policy requiring compliant or domain-joined Windows devices before users access Microsoft 365 services.
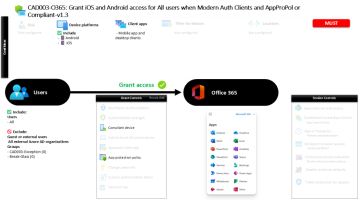
Conditional Access iOS Android for Office 365
Conditional Access iOS Android Office 365 policy allowing mobile access only when devices are compliant or protected by an approved application policy.
Our workflow
Analyze
Prepare
Migrate
Finalize
Start your migration here
Address
Dierenriem 124
1033 AJ Amsterdam
M. info@in2it.solutions
T. +31 (0)6 274 50 598




