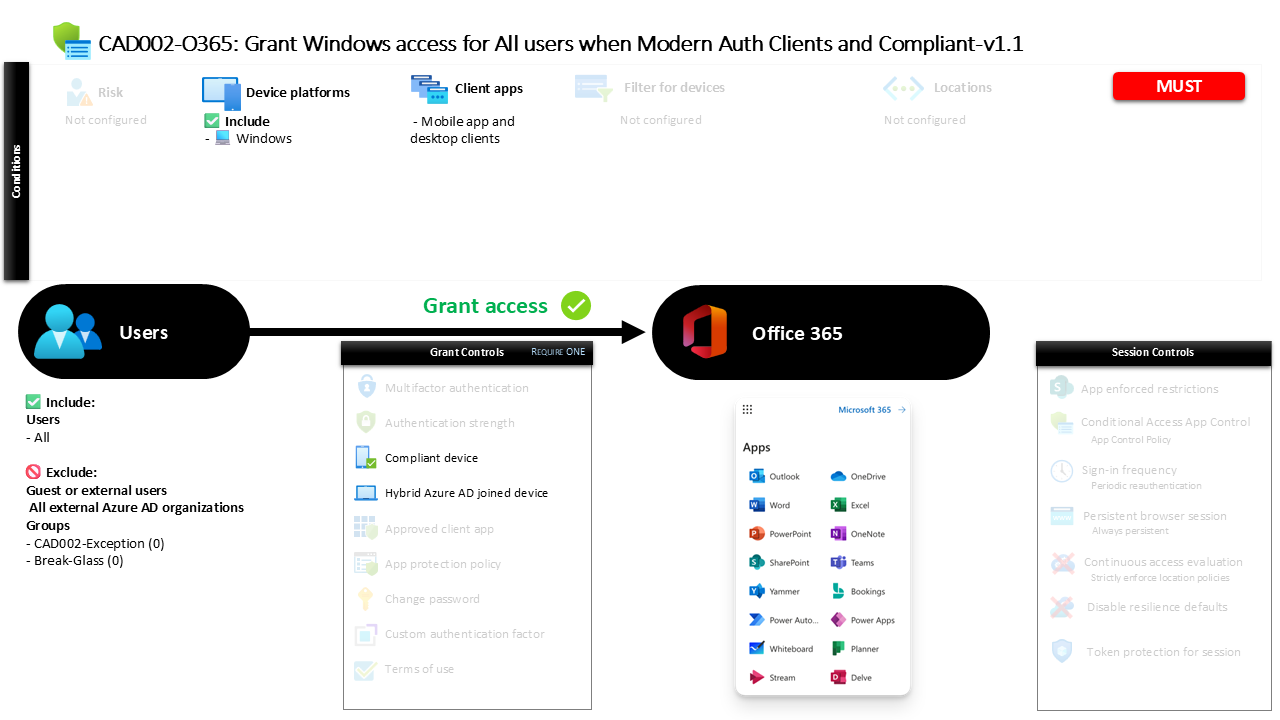
Conditional Access Windows Device Trust CAD002 O365 Grant Windows Access for All Users When Modern Auth Clients and Compliant
Introduction
Conditional Access Windows device trust policies exist because identity alone is no longer enough to secure access to cloud services. A stolen password or compromised session can allow attackers to sign in from unmanaged devices that sit completely outside organizational control. That is why many organizations extend identity verification with device trust requirements. Instead of only asking who the user is, the platform also verifies what device they are using.
This Conditional Access Windows device trust policy addresses that challenge directly. It evaluates whether a Windows device meets one of two trusted states before allowing users to access Microsoft 365 services through modern authentication clients. In practice, this means access is granted only when the device is either recognized as compliant by device management or joined to the organization’s domain environment. By combining identity validation with device posture, the policy helps ensure that corporate services are accessed only from systems that meet the organization’s security expectations.
This Policy in One Line
This Conditional Access Windows device trust policy allows access to Microsoft 365 services from Windows devices only when the device is either compliant or domain joined.
What This Conditional Access Policy Does
This Conditional Access Windows device trust policy enforces a device-based access decision for Windows systems that connect to Microsoft 365 services through modern authentication clients. Instead of simply allowing any authenticated user to reach cloud services, the policy evaluates the trust state of the device during the sign-in process.
When a user attempts to authenticate, Microsoft Entra ID checks whether the request originates from a Windows platform and whether the connection is coming from a desktop or mobile application client using modern authentication. Once those conditions match, the platform evaluates device trust signals. The device must either be recognized as compliant by device management or identified as a domain-joined device within the organization’s directory environment.
If one of these device trust conditions is satisfied, the sign-in proceeds normally. If neither condition is met, access to the protected services is denied. This design ensures that users can still work flexibly while preventing access from unmanaged Windows systems that fall outside the organization’s security controls.
Who the Policy Applies To
The scope of this Conditional Access policy is intentionally broad, targeting all users attempting to access the protected services. This design choice reflects a common security strategy in modern identity architectures: device trust policies are typically applied widely so that all identities benefit from consistent access controls.
External and guest user types are excluded from this enforcement scope. These external identities often authenticate through federated or partner tenant environments where device trust cannot always be evaluated in the same way as internal corporate devices. Excluding these user categories prevents unintended authentication barriers during cross-organization collaboration scenarios.
Additionally, the configuration contains specific exclusion groups. Organizations commonly use such exclusion groups to support controlled exception management. These groups typically allow administrators to temporarily bypass device restrictions during troubleshooting, device enrollment transitions, or emergency operational scenarios. By structuring the policy this way, administrators maintain strict default enforcement while still retaining operational flexibility when exceptions must be granted through approved processes.
What Apps and Services the Policy Protects
The policy protects Microsoft 365 cloud services accessed through modern authentication mechanisms. These services typically include applications such as collaboration tools, productivity platforms, and cloud-based communication systems that rely on Microsoft Entra ID for identity validation.
Because these services represent core productivity workloads, protecting them with device trust requirements significantly reduces the risk of unauthorized access from unmanaged systems. Even if valid credentials are used, access cannot proceed unless the device itself meets organizational trust criteria.
This approach reflects a broader security design principle within Microsoft Conditional Access: sensitive cloud resources should be reachable only from devices that comply with security standards or belong to the organization’s trusted device inventory. By protecting Microsoft 365 workloads in this way, organizations align user access with their device management strategy and endpoint security posture.
Platforms, Devices, and Client Apps in Scope
This Conditional Access configuration specifically evaluates Windows devices. When a sign-in request originates from another operating system platform, the policy does not apply because the platform condition does not match.
The policy also focuses on modern authentication client applications, including desktop and mobile applications that authenticate using modern protocols supported by Microsoft Entra ID. These client types are commonly used by productivity applications installed on managed workstations or enterprise laptops.
By targeting this specific combination of Windows platforms and modern authentication clients, the policy concentrates enforcement on the primary access path used by corporate devices. This ensures that the policy evaluates device trust during the authentication flow used by most managed enterprise workstations. The result is a targeted control that protects common access scenarios without unnecessarily interfering with unrelated authentication flows.
How Access Is Decided
The decision logic within this Conditional Access Windows device trust policy is straightforward but powerful. Once the user and platform conditions match, Microsoft Entra ID evaluates the device state before granting access.
Two possible device trust conditions can satisfy the policy. The device must either be recognized as compliant through device management or identified as a domain-joined device associated with the organization’s directory environment.
Because the access logic accepts either condition, users can sign in successfully if at least one of these trust signals is present. A fully managed device that meets compliance standards passes the check immediately. Similarly, a device joined to the organization’s directory environment also satisfies the requirement because it is considered part of the trusted corporate infrastructure.
This dual-condition design allows organizations to support multiple device management strategies simultaneously while maintaining strong security boundaries.
What the User Experience Looks Like During Sign-In
From the user’s perspective, the experience during sign-in is usually seamless when the device already meets trust requirements. A user working from a corporate Windows workstation that is either compliant or domain joined will simply authenticate and proceed directly to the requested application.
However, if a user attempts to access Microsoft 365 services from a personal or unmanaged Windows device, the experience changes. During authentication, Microsoft Entra ID evaluates the device state and determines that the system does not meet the required trust conditions. Because the device is neither compliant nor domain joined, the sign-in cannot proceed.
This evaluation happens automatically during the authentication flow, often without the user understanding the full security logic behind it. From a security architecture perspective, this behavior is intentional. Conditional Access operates silently in the background, ensuring that only trusted devices are permitted to access protected services.
Why This Policy Matters for Security and the Business
Device trust enforcement significantly reduces the attack surface associated with identity-based attacks. Even when credentials are compromised, attackers often rely on unmanaged devices to access corporate resources. By requiring trusted device states, organizations remove that opportunity.
For the business, this type of policy helps ensure that sensitive collaboration environments remain accessible only from systems that meet corporate security requirements. Managed devices typically include endpoint protection, patch management, disk encryption, and monitoring capabilities that reduce risk.
The policy therefore creates an additional defensive layer that complements identity protections such as strong authentication or risk detection. Instead of relying solely on who the user is, the system also evaluates where the user is connecting from and whether that device is part of the trusted environment.
Is This a Foundational or Must-Have Policy?
Device trust enforcement policies are widely considered foundational elements of a mature Conditional Access architecture. While identity verification protects accounts, device trust ensures that access occurs only from endpoints that meet security standards.
Organizations adopting Zero Trust principles often introduce policies like this early in their Conditional Access strategy. By requiring trusted devices for core productivity services, they significantly reduce the likelihood of unauthorized access from unmanaged systems.
Because Microsoft 365 workloads are central to everyday business operations, enforcing device trust at this layer creates a strong baseline protection across the digital workplace.
Important Design Choices and Things to Notice
One important design element in this Conditional Access policy is the use of two alternative device trust signals. Instead of forcing a single device management model, the policy supports both compliant devices and domain-joined systems.
This flexibility is particularly useful in environments transitioning between traditional directory-based device management and modern cloud-based device management platforms. It allows organizations to support legacy workstation models while gradually introducing modern compliance-based management.
Another notable design choice is the focus on Windows platforms combined with modern authentication clients. This ensures that enforcement occurs primarily where corporate workstations access cloud services, aligning security controls with real-world usage patterns.
Conditional Access Design Principles Behind This Policy
This Conditional Access Windows device trust policy reflects a common Zero Trust design principle: verify both identity and device posture before granting access to cloud services. Instead of assuming that authentication alone is sufficient, the system continuously evaluates additional security signals.
The policy also demonstrates the principle of layered access control. Device compliance and domain membership act as independent indicators of device trust. Allowing either signal ensures operational flexibility while still maintaining strict device verification.
Finally, the design highlights the importance of consistent enforcement. By applying device trust requirements broadly to users accessing Microsoft 365 services from Windows devices, the organization ensures that the same security expectations apply across the environment.
Final Thoughts
Conditional Access Windows device trust policies play a critical role in modern identity security strategies. They shift the security model from simple authentication to contextual access decisions that evaluate both the user and the device involved in the sign-in process.
By allowing access only when a Windows device is either compliant or domain joined, this policy ensures that Microsoft 365 services remain accessible only from trusted systems. The result is a balanced security design that supports productivity while protecting the organization’s most important collaboration platforms.
As organizations continue adopting cloud-first workplace strategies, policies like this one form a core part of the broader Conditional Access architecture that protects identities, devices, and services together.