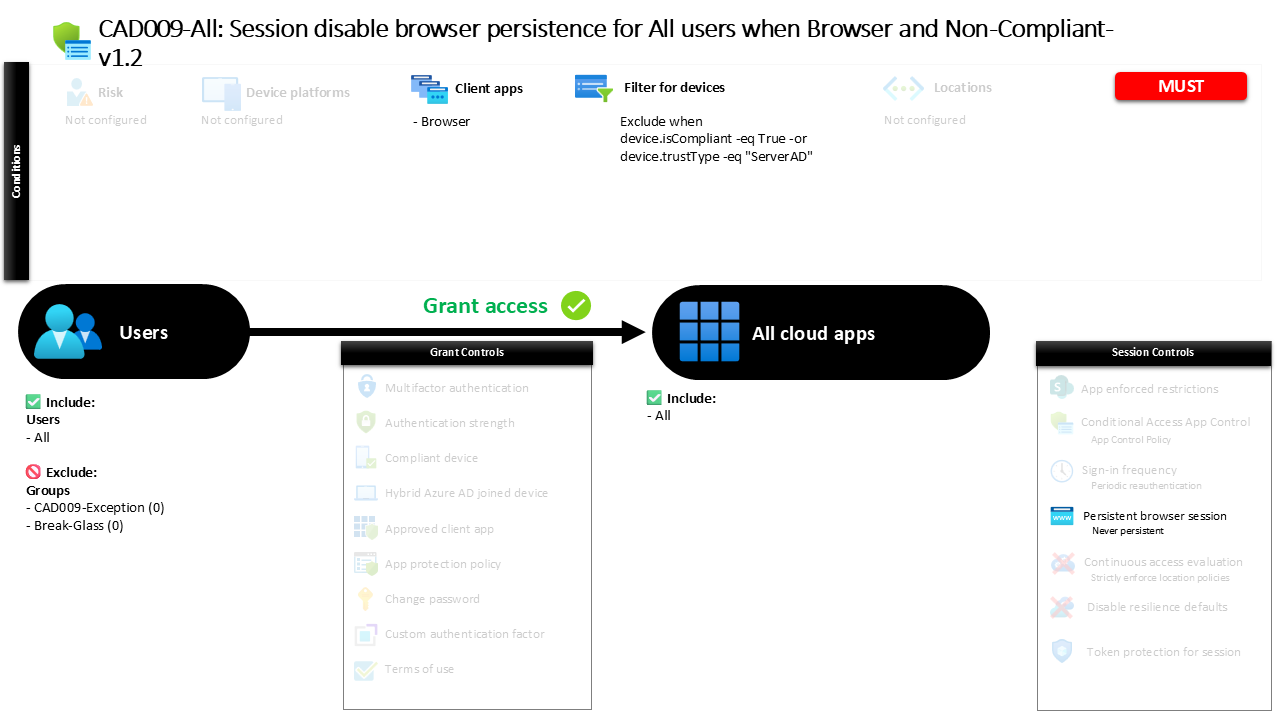
Conditional Access Browser Persistence Control CAD009 - All Session Disable Browser Persistence for All Users When Browser and Non-Compliant
Introduction
Conditional Access browser persistence is designed to solve a common security problem in modern cloud environments. Users frequently access corporate applications through browsers on devices that may not meet corporate compliance standards. When sessions persist in these environments, authentication tokens can remain valid long after the user has finished working. That persistence creates an opportunity for unauthorized reuse, especially on shared or unmanaged devices.
A well-designed Conditional Access policy can reduce that risk by controlling how browser sessions behave after authentication. Instead of allowing long-lived browser sessions, the system can enforce a model where each session is temporary and must be re-authenticated when it ends.
This policy implements exactly that design principle. It evaluates browser-based access and ensures that when the device does not meet compliance or trusted device conditions, browser sessions cannot remain persistent. The result is a safer authentication experience that limits the lifespan of browser access tokens and reduces the risk associated with unmanaged devices.
This Policy in One Line
This Conditional Access browser persistence policy prevents persistent browser sessions when users sign in from devices that are not compliant or not recognized as trusted directory-joined devices.
What This Conditional Access Policy Does
The intention behind this policy is to limit how long authentication sessions survive in web browsers when device trust cannot be confirmed. Conditional Access evaluates the device characteristics during sign-in and determines whether the device meets compliance standards or belongs to a trusted directory environment.
If the device does not meet those conditions, the policy applies a browser session control that disables persistent sessions. In practical terms, this means the browser cannot store a long-lived sign-in state. Once the browser session ends or the user closes the window, the authentication state disappears and must be re-established during the next sign-in.
This configuration reflects a common security architecture principle. When device posture cannot be verified, access should remain possible but the duration of trust should be shortened. Instead of completely blocking access, the system allows productivity while preventing sessions from silently remaining active across long periods of time.
By controlling browser persistence in this way, organizations reduce the risk of session reuse on devices that fall outside corporate compliance boundaries.
Who the Policy Applies To
The policy targets the entire identity population within the tenant. Any user who signs in through a browser can potentially be evaluated by this rule.
Conditional Access evaluates the user scope before it processes device and session conditions. Because the design includes the entire user population, the security control operates broadly across the environment rather than protecting only a subset of users or departments. This type of wide targeting is typical for foundational session security policies, since session persistence risks exist regardless of user role.
Certain identities are intentionally excluded from the scope. In many environments, organizations maintain controlled exclusion groups to support operational scenarios such as emergency access accounts, troubleshooting activities, or tightly governed administrative workflows. These exclusions allow security teams to maintain operational continuity while still enforcing the control across the broader user population.
The overall effect is a policy that protects nearly all interactive browser users while still allowing carefully governed exceptions where necessary.
What Apps and Services the Policy Protects
The policy applies to every cloud application integrated with Microsoft Entra authentication. Instead of targeting a limited set of services, the configuration evaluates browser sign-ins across the entire application landscape.
This broad scope reflects the nature of browser session persistence risks. Persistent sessions can exist regardless of which application is accessed, because they originate at the identity platform level rather than the application itself. Once a browser session is established, it may grant access to multiple applications through single sign-on.
By applying the session control across all applications, the policy ensures consistent behavior during browser authentication. Whether the user is opening collaboration tools, productivity services, internal enterprise applications, or third-party SaaS integrations, the same browser session rule applies.
From a security architecture perspective, this design reduces policy complexity while ensuring that session persistence controls remain consistent across the entire identity ecosystem.
Platforms, Devices, and Client Apps in Scope
The policy evaluates sign-ins that originate specifically from browser-based client applications. This means the rule focuses on interactive web access rather than mobile or desktop application authentication flows.
Device posture plays an important role in determining when the policy activates. During authentication, Conditional Access evaluates whether the device is marked as compliant through device management or recognized as a trusted directory-joined system. Devices meeting those criteria represent environments where security controls such as device management, endpoint protection, and corporate configuration standards are already enforced.
The policy intentionally excludes those trusted devices from the rule. As a result, browser persistence restrictions are applied primarily when the device cannot be verified as compliant or trusted. These scenarios typically include personal devices, unmanaged systems, or machines that fall outside corporate device governance.
This approach balances security with usability. Trusted and managed endpoints maintain normal browser behavior, while less trusted environments are subject to stricter session controls.
How Access Is Decided
Conditional Access evaluates this policy during the authentication pipeline. When a browser-based sign-in occurs, the identity platform checks several factors in sequence before determining how the session should behave.
First, the platform confirms that the user is within the scope of the policy. Next, it verifies that the authentication request originates from a browser client application. Once these conditions are satisfied, the device characteristics are evaluated.
If the device is marked as compliant or recognized as a trusted directory-joined system, the session control does not apply and the authentication proceeds normally. If those device characteristics are absent, the session control activates.
At that point the policy enforces a restriction on browser session persistence. The browser is not allowed to maintain a persistent sign-in state. Authentication remains valid only for the duration of the active browser session, ensuring that the identity platform periodically re-evaluates user authentication.
This layered evaluation model allows Conditional Access to make contextual decisions based on both user identity and device trust.
What the User Experience Looks Like During Sign-In
From the user’s perspective, the experience is subtle but meaningful. The authentication process itself looks familiar. Users open a browser, navigate to a cloud application, and complete the standard Microsoft Entra sign-in process.
The difference becomes visible after the session ends. Because browser persistence is disabled, the browser cannot maintain a long-term sign-in state. When the user closes the browser window or returns later, they must authenticate again rather than being automatically signed back into the application.
On compliant or trusted corporate devices, users typically retain their expected single sign-on experience. On devices that fall outside those trust boundaries, authentication becomes more frequent because the session cannot persist across browser restarts.
This user experience signals an intentional security design: convenience on trusted devices and shorter authentication lifetimes on devices that the organization cannot fully control.
Why This Policy Matters for Security and the Business
Browser sessions are one of the most common attack surfaces in cloud identity systems. If a persistent session remains active on a shared or unmanaged device, anyone with access to that device may gain unintended access to corporate applications.
Disabling persistent browser sessions on non-compliant devices directly addresses this risk. Even if a user signs in from a personal or unmanaged computer, the session expires when the browser closes. That significantly reduces the window during which authentication tokens could be reused.
For organizations balancing remote work, bring-your-own-device scenarios, and cloud application adoption, this control offers a practical security compromise. It allows employees and partners to access applications from many environments while still limiting long-term exposure.
From a business perspective, the policy protects corporate data without completely blocking productivity. Users retain the ability to work from unmanaged devices, but access remains tied to active sessions rather than persistent browser authentication.
Is This a Foundational or Must-Have Policy?
This policy represents a foundational component of a Conditional Access security architecture. Session controls such as browser persistence management are often deployed early in a security maturity journey because they reduce risk without requiring complex infrastructure.
Unlike strict device compliance policies that can prevent access entirely, browser persistence controls operate in a more flexible way. They allow organizations to maintain open access models while still enforcing safer authentication behavior.
In many environments, this type of control complements other policies such as device compliance enforcement, sign-in risk evaluation, and multifactor authentication requirements. Each policy addresses a different dimension of identity security, and together they form a layered defense strategy.
By starting with session-based controls like this one, organizations can introduce meaningful protection against session hijacking and token reuse while keeping the user experience manageable.
Important Design Choices and Things to Notice
One of the most important design decisions in this configuration is the distinction between trusted and untrusted devices. Rather than applying strict controls to every device, the policy evaluates device posture and applies session restrictions only when trust cannot be established.
Another notable element is the exclusive focus on browser client applications. Browser sessions behave differently from native application authentication flows, and they are more likely to remain active through cookies or stored session tokens. By targeting browser traffic specifically, the policy addresses the session persistence risk where it most commonly appears.
The device filtering logic also plays a key role. Devices that meet compliance standards or are recognized as trusted directory-joined systems are intentionally excluded from the restriction. This preserves the streamlined single sign-on experience on corporate endpoints while tightening controls elsewhere.
Together, these design choices demonstrate a security approach that focuses on contextual trust rather than applying identical restrictions across all access scenarios.
Conditional Access Design Principles Behind This Policy
Several Conditional Access design principles are visible in this configuration. The first is contextual access control. Rather than evaluating identity alone, the system incorporates device posture and client application context before deciding how a session should behave.
The second principle is risk reduction through session management. Authentication tokens represent a powerful capability. If those tokens persist too long on unmanaged devices, they can become a pathway to unauthorized access. Restricting session persistence directly reduces that exposure.
Another important principle is user productivity. Security controls should not unnecessarily block legitimate work. By allowing access but limiting session duration on less trusted devices, the policy achieves a balanced security posture.
Finally, the policy reflects the concept of trust tiers. Devices that meet compliance or directory trust standards receive a smoother experience, while devices outside that trust boundary are subject to stricter session management.
Final Thoughts
Conditional Access browser persistence controls are a subtle but powerful element of identity security. They operate quietly in the background, shaping how authentication sessions behave without dramatically changing the sign-in process.
By preventing persistent browser sessions on devices that are not compliant or trusted, this policy reduces the risk of session reuse and unauthorized access. At the same time, it preserves usability by allowing trusted corporate endpoints to maintain normal browser authentication behavior.
In modern cloud environments where users frequently access applications from a wide variety of devices, these session controls form an important layer of defense. They reinforce the idea that access should not only depend on who the user is, but also on the context in which authentication occurs.
When implemented as part of a broader Conditional Access strategy, browser persistence restrictions help create a more resilient identity platform that protects both users and organizational data.