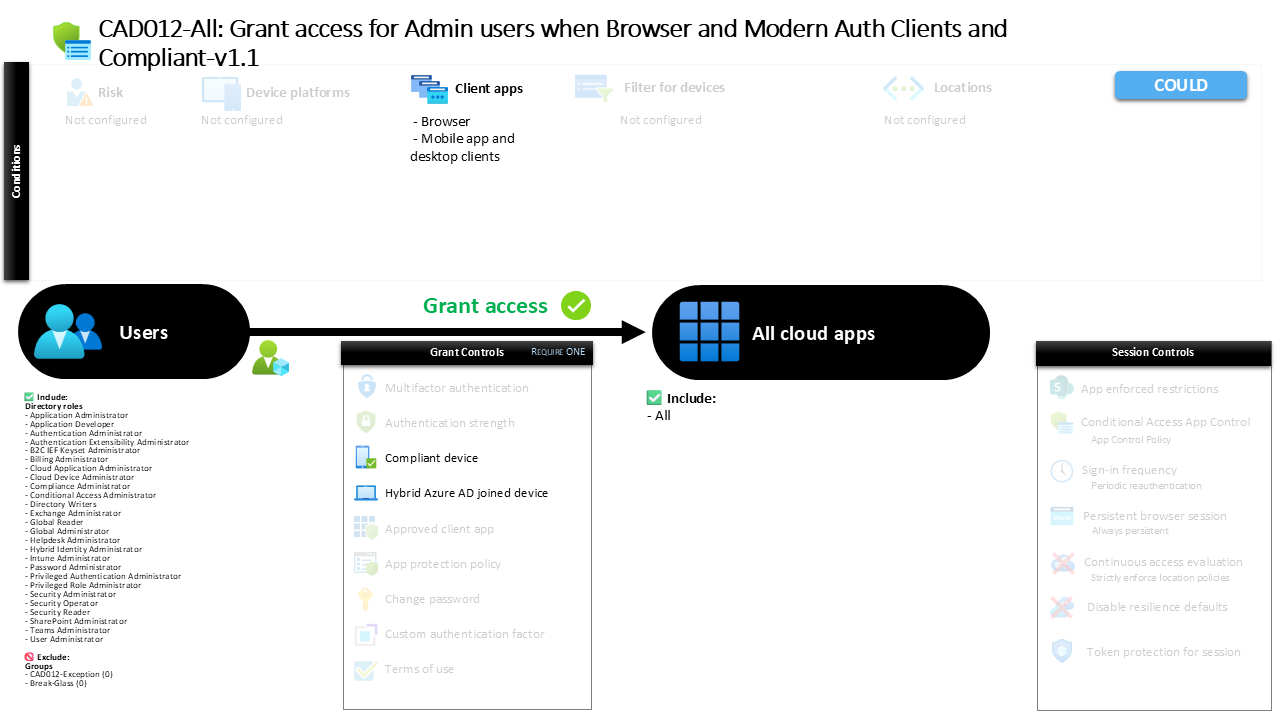
Conditional Access Admin Device Compliance CAD012-All: Grant access for Admin users when Browser and Modern Auth Clients and Compliant
Introduction
Conditional Access admin device compliance is often introduced after organizations realize that privileged accounts represent the most attractive target in any Microsoft Entra ID environment. Administrative identities have the ability to modify tenant configuration, change identity settings, and control access across cloud workloads. If those accounts are allowed to sign in from unmanaged devices or insecure environments, the entire identity platform becomes vulnerable.
This policy design addresses that challenge by introducing a device trust requirement for administrative access. Instead of relying solely on identity verification, the access decision also evaluates whether the device used during sign-in meets organizational trust standards. In practical terms, that means administrative users must sign in from devices that are either compliant with management policies or properly joined to the organization’s domain environment.
By applying this control across browser and modern authentication clients and across all applications, the design establishes a strong security baseline. The result is a Conditional Access architecture where privileged operations occur only from devices that the organization can trust and manage.
This Policy in One Line
This Conditional Access admin device compliance policy allows administrative sign-in only when the device used is either compliant with device management policies or joined to the organization’s domain environment.
What This Conditional Access Policy Does
The purpose of this policy is straightforward: administrative identities can only access cloud resources when the device they are using satisfies defined trust conditions. Instead of allowing privileged access from any browser or client device, the policy evaluates whether the device meets one of two acceptable security states.
When an administrative user signs in, Conditional Access checks the device posture as part of the access decision. If the device is recognized as compliant with device management policies, access can proceed. If the device is not managed but is recognized as joined to the organizational domain, that device state can also satisfy the access requirement.
The grant control uses a logical approach where either of these device states can permit access. This provides flexibility in environments where both modern device management and traditional domain-joined systems coexist. From a design perspective, the policy enforces a device trust requirement while still supporting multiple enterprise device management models.
Who the Policy Applies To
This policy targets administrative roles within Microsoft Entra ID. Rather than selecting individual users or groups, the scope is defined by privileged role assignments. Any identity assigned to one of the included administrative roles becomes subject to the device trust requirements defined in this policy.
Targeting roles instead of individual accounts is an important architectural decision. Administrative privileges in Entra ID can change over time as users are assigned or removed from roles. By linking Conditional Access directly to roles, the policy automatically applies the security requirements to any identity that holds privileged permissions.
The configuration also includes exclusion groups. Organizations commonly maintain these groups to support controlled exception management. In mature environments, such groups are typically connected to approval workflows or time-based access processes so that exceptions can be granted temporarily without weakening the long-term security posture of the tenant.
What Apps and Services the Policy Protects
The policy protects access to all cloud applications available through the identity platform. By applying the rule broadly across applications, the design avoids creating security gaps where administrative users might access sensitive services through an unprotected application entry point.
Administrative privileges often span multiple Microsoft services, including identity configuration, productivity platforms, and infrastructure management components. Because of this, restricting the policy to a subset of applications would create inconsistencies in the security model.
Applying the device trust requirement universally ensures that the same access standard applies regardless of which workload an administrator attempts to reach. This approach reflects a common Conditional Access design principle: when protecting privileged identities, consistency across applications is more important than selective enforcement.
Platforms, Devices, and Client Apps in Scope
This policy evaluates access when administrators sign in through browsers or through modern authentication clients used by desktop and mobile applications. These two client categories represent the primary access paths administrators use when interacting with cloud workloads.
Browser access is particularly important because many administrative tasks are performed through web-based management portals. Without Conditional Access enforcement at the browser level, privileged actions could potentially be performed from unmanaged endpoints.
Modern authentication clients represent another critical access channel. Administrative identities may interact with services through rich client applications that rely on modern authentication protocols. By including these client types, the policy ensures that the same device trust requirements apply regardless of how the administrator chooses to authenticate.
How Access Is Decided
During the sign-in process, Conditional Access evaluates the context of the authentication request. After the identity has been verified, the system checks whether the device being used meets the trust requirements defined in the policy.
The grant controls define two acceptable device states. The first condition allows access when the device is marked as compliant. Compliance typically indicates that the device is managed and meets organizational security policies such as encryption, operating system requirements, and security posture checks.
The second condition allows access when the device is recognized as joined to the organizational domain environment. Domain-joined systems are traditionally managed endpoints that operate within the organization’s identity infrastructure.
Because the policy uses a flexible evaluation model, satisfying either device condition allows the access request to proceed. If neither condition is met, the sign-in attempt cannot satisfy the policy requirements.
What the User Experience Looks Like During Sign-In
From the administrator’s perspective, the sign-in process remains familiar but includes an additional security evaluation. The user begins authentication through a browser or modern authentication client in the same way they normally would when accessing cloud services.
Once identity verification occurs, Conditional Access evaluates the device state associated with the session. If the device is compliant or domain joined, the access request continues without interruption. The administrator reaches the intended resource and proceeds with their work normally.
If the device does not meet either of the accepted device trust conditions, the access request cannot proceed. In this situation, the administrator must switch to a trusted device environment that satisfies the policy requirements before privileged access can be granted.
Why This Policy Matters for Security and the Business
Administrative accounts represent the control plane of the identity platform. If those accounts are compromised, attackers can manipulate authentication policies, create new identities, or gain persistent access across the tenant.
Requiring trusted devices for administrative access significantly reduces this risk. Even if credentials are exposed, attackers would still need access to a compliant or domain-joined device environment in order to use those credentials successfully.
From a business perspective, this policy strengthens identity security without significantly disrupting administrator productivity. Administrators typically perform their work from managed corporate systems, which means the policy reinforces existing operational practices rather than introducing entirely new workflows.
Is This a Foundational or Must-Have Policy?
This type of policy is widely considered a foundational Conditional Access control for protecting privileged identities. Administrative access is one of the most sensitive aspects of identity security, and device trust requirements form a critical layer of defense in modern cloud environments.
Organizations that adopt Conditional Access often prioritize policies protecting administrators before expanding similar controls to standard users. The reasoning is simple: securing privileged identities has the greatest immediate impact on reducing risk across the tenant.
By enforcing trusted device conditions for administrators, the organization establishes a clear baseline that aligns with modern Zero Trust identity principles.
Important Design Choices and Things to Notice
Several design decisions within this policy reflect common Conditional Access architecture practices. One notable choice is the use of role-based targeting instead of selecting individual users. This ensures that security enforcement automatically follows the privilege rather than the identity.
Another design detail is the inclusion of both compliant device and domain-joined device states. This accommodates environments where organizations manage a mix of modern and traditional endpoint management approaches.
Finally, applying the policy across all applications ensures that administrative security standards remain consistent regardless of the service being accessed. This avoids fragmented protection and simplifies long-term security governance.
Conditional Access Design Principles Behind This Policy
At its core, this policy reflects the principle of device-based trust within a Zero Trust architecture. Identity alone is not sufficient to determine whether access should be granted. The device used during authentication also becomes an important part of the evaluation process.
Another design principle present here is privileged access isolation. Administrative actions are limited to devices that the organization can manage and verify. This prevents sensitive operations from being performed from unmanaged personal systems or unknown endpoints.
Together, these design elements reinforce a layered identity security model where authentication, device trust, and access control work together to protect the tenant.
Final Thoughts
Conditional Access admin device compliance policies play an essential role in protecting privileged identities within Microsoft Entra ID. By requiring administrators to sign in from compliant or domain-joined devices, organizations ensure that sensitive operations occur only within trusted environments.
This approach strengthens the identity security boundary without introducing unnecessary complexity for administrators. Access remains smooth when trusted devices are used, while untrusted environments are prevented from interacting with privileged accounts.
As organizations continue adopting Zero Trust identity models, policies like this form the foundation of secure administrative access and responsible identity governance.