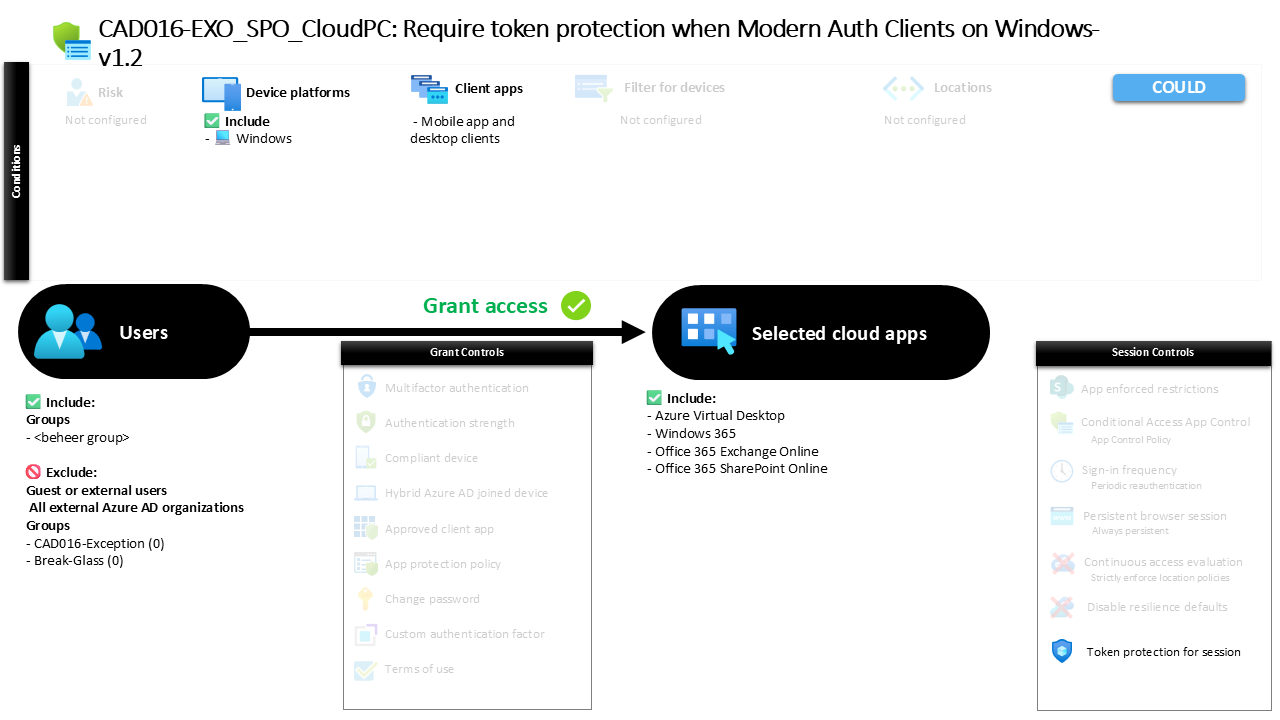
Conditional Access Token Protection for Windows CAD016-EXO_SPO_CloudPC Require token protection when Modern Auth Clients on Windows
Introduction
Conditional Access token protection addresses a security problem that often goes unnoticed in modern authentication environments. When users sign in to cloud services, authentication tokens are issued that allow applications to access resources without repeatedly asking for credentials. These tokens are designed for convenience, but if they are intercepted or replayed, attackers may gain access to services without needing to authenticate again.
Organizations that rely heavily on modern authentication clients on Windows systems must therefore ensure that these tokens cannot be reused outside the trusted environment where they were issued. Conditional Access provides a mechanism to bind authentication tokens to the device and the sign-in session, making token theft significantly harder to exploit.
This policy implements Conditional Access token protection specifically for modern authentication clients operating on Windows devices. By enforcing secure session behavior for targeted cloud services, the policy strengthens the trust relationship between identity, device, and session while maintaining the seamless sign-in experience users expect.
This Policy in One Line
This policy enforces Conditional Access token protection for modern authentication clients running on Windows devices when accessing selected Microsoft cloud services.
What This Conditional Access Policy Does
The purpose of this policy is to ensure that authentication tokens issued during sign-in are protected against misuse. In modern authentication environments, tokens allow applications such as desktop clients or mobile apps to access services after a successful sign-in without repeatedly prompting the user for credentials.
This policy introduces a secure sign-in session control that activates token protection. When a user signs in through a supported modern authentication client on a Windows device, Conditional Access applies session-level protection that ties the authentication token to the device and the session where it was issued.
From a security design perspective, this mechanism reduces the risk of token replay attacks. Even if a token were extracted from a device, it cannot be reused in a different environment because the token is bound to the original session context. In effect, Conditional Access ensures that authentication tokens behave more like secure credentials tied to a device rather than transferable artifacts.
This design strengthens identity protection while maintaining compatibility with modern authentication flows used by enterprise productivity applications.
Who the Policy Applies To
The scope of this policy is defined through group-based targeting. Conditional Access evaluates sign-ins from users who are members of a specific security group configured in the policy.
Group-based targeting is a common design approach because it allows organizations to control policy rollout in a structured and predictable way. Security teams can include users gradually, test behavior with selected populations, and expand the policy once confidence in the design is established.
The configuration also contains exclusions that remove specific groups from the policy scope. Organizations commonly use exclusion groups to support controlled exception management. These groups allow security teams to temporarily exclude accounts that require troubleshooting, application compatibility testing, or staged policy deployment.
In addition, the configuration excludes external identities. This means guest users, business-to-business collaborators, and other external accounts are not evaluated by this policy. The focus of the design therefore remains on protecting authentication sessions for internal identities that access corporate cloud services from Windows devices.
What Apps and Services the Policy Protects
The policy targets a defined set of cloud applications. These services represent the workloads where authentication tokens are issued and subsequently used by modern clients during normal application activity.
Because Conditional Access evaluates authentication before access is granted, the policy ensures that token protection applies whenever users sign in to these specific services using supported Windows-based clients.
The design reflects a common Conditional Access strategy: apply advanced session protections only to workloads where persistent authentication tokens are frequently used. This approach ensures that sensitive enterprise services benefit from stronger protection without unnecessarily affecting unrelated applications.
By focusing token protection on selected Microsoft cloud services, the policy strengthens the trust boundary around productivity workloads where authentication tokens play a critical role in maintaining session continuity.
Platforms, Devices, and Client Apps in Scope
This policy is intentionally limited to Windows platforms. Conditional Access evaluates the device platform during sign-in and applies the policy only when the device is identified as running Windows.
The client application condition is also defined. The policy applies to mobile applications and desktop clients that use modern authentication. These clients rely on OAuth-based authentication flows and obtain tokens after successful sign-in.
From a security architecture perspective, this scope reflects where token replay risks are most relevant. Desktop and mobile applications typically maintain active authentication sessions and store tokens locally to support continuous access to cloud services.
By focusing on modern authentication clients on Windows devices, the policy ensures that token protection is enforced precisely where token-based authentication is actively used. This targeted approach improves security without introducing unnecessary restrictions for other platforms or client types.
How Access Is Decided
Conditional Access evaluates several factors during the authentication process to determine whether the policy applies to a sign-in attempt. First, the service being accessed must match one of the targeted cloud applications. Next, the user must belong to the group included in the policy scope and must not fall within any exclusion group.
The device platform is then evaluated. Only sign-ins originating from Windows devices meet the platform requirement. In addition, the authentication must occur through a modern authentication client categorized as a mobile application or desktop client.
Once these conditions are satisfied, Conditional Access applies a secure sign-in session control. This control activates token protection, ensuring that authentication tokens issued during the session are bound to the device and cannot be reused outside the original context.
The result is a layered decision model where identity, application, client type, and device platform all combine to determine whether token protection is enforced during the sign-in process.
What the User Experience Looks Like During Sign-In
From the user perspective, this policy operates quietly in the background. When a user signs in from a supported Windows device using a modern authentication client, the authentication flow proceeds normally. Credentials are entered, authentication completes, and access to the application is granted.
Behind the scenes, however, Conditional Access ensures that the authentication session is protected. The token issued to the application is tied to the device and session context. If the same token were extracted and attempted to be reused elsewhere, the service would reject it because the required session context would not match.
This approach is important for usability. Users are not confronted with additional prompts or disruptive authentication steps. Instead, the protection is implemented at the protocol and session level, strengthening security without altering the normal sign-in workflow.
Why This Policy Matters for Security and the Business
Authentication tokens are a central component of modern cloud identity systems. They enable seamless application access, but they also represent a valuable target for attackers who attempt to bypass authentication controls.
By implementing Conditional Access token protection, organizations ensure that tokens cannot be reused outside the environment where they were issued. This significantly reduces the effectiveness of token theft attacks, including scenarios where tokens are extracted from compromised devices or intercepted during authentication flows.
For the business, the benefit is clear. Security improves without disrupting the productivity tools employees rely on every day. The policy strengthens trust in modern authentication systems while maintaining the smooth user experience expected from cloud-based collaboration platforms.
Is This a Foundational or Must-Have Policy?
This policy falls into the category of advanced Conditional Access protections rather than foundational controls. Foundational policies typically focus on baseline protections such as multifactor authentication or device compliance requirements.
Token protection represents the next step in securing authentication sessions after those baseline protections are established. It addresses a more sophisticated threat scenario in which attackers attempt to reuse legitimate authentication tokens instead of stealing credentials directly.
Organizations that have already implemented modern authentication and Conditional Access frameworks often deploy policies like this to strengthen session security and reduce the risk of token replay attacks.
Important Design Choices and Things to Notice
One notable design choice in this policy is the focus on modern authentication clients. Legacy authentication mechanisms do not support the same token-based security model and therefore cannot benefit from token protection controls.
Another important aspect is the platform restriction. By limiting the policy to Windows devices, the configuration ensures that token protection is applied only where supported client and device capabilities exist.
The use of group-based targeting also reflects a controlled deployment strategy. Security teams can manage policy rollout, monitor behavior, and adjust scope without affecting the entire organization at once.
Together, these design decisions illustrate how Conditional Access policies are often built incrementally, layering advanced protections onto a well-structured identity security architecture.
Conditional Access Token Protection Design Principles Behind This Policy
This policy reflects several important Conditional Access design principles. The first is targeted enforcement. Rather than applying session protections universally, the policy focuses on specific applications, client types, and device platforms where token-based authentication is most relevant.
The second principle is risk reduction through session binding. By binding authentication tokens to the device and session context, Conditional Access reduces the usefulness of stolen tokens.
Finally, the design demonstrates how Conditional Access can extend identity protection beyond the moment of authentication. Security does not stop once a user signs in. Instead, Conditional Access continues protecting the session throughout the lifetime of the authentication token.
These principles are central to modern identity security strategies within Microsoft Entra ID environments.
Final Thoughts
Conditional Access token protection is an important evolution in protecting cloud authentication sessions. While traditional controls focus on verifying identity during sign-in, token protection ensures that authentication artifacts cannot be reused outside their intended context.
This policy demonstrates how Conditional Access can strengthen the security of modern authentication clients on Windows devices without introducing friction for users. By applying secure session controls to selected cloud services, organizations create a stronger trust boundary around the applications employees rely on every day.
As identity threats continue to evolve, policies like this play a critical role in ensuring that authentication tokens remain as secure as the identities that generated them.