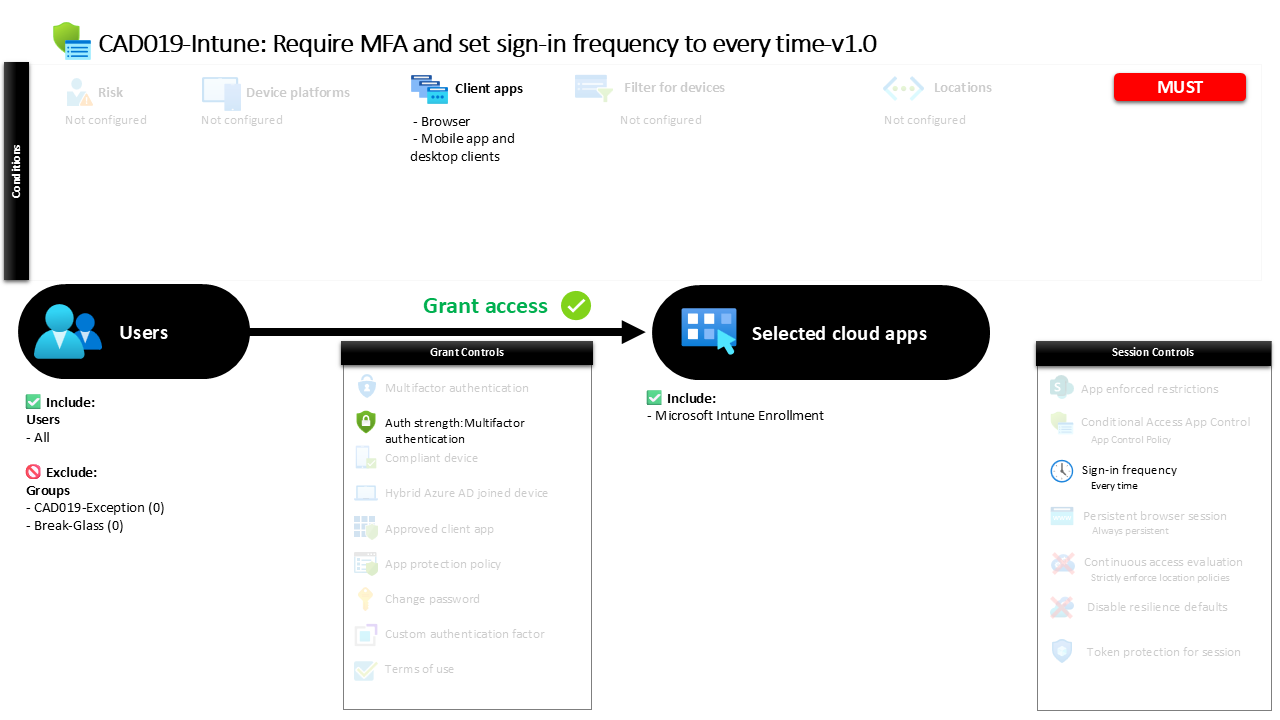
Conditional Access MFA Every Sign-In CAD019-Intune Require MFA and set sign-in frequency to every time
Introduction
Conditional Access MFA Every Sign-In exists to solve a simple but persistent security challenge: identity sessions often last far longer than organizations expect. A user authenticates once, a session is established, and access quietly continues in the background. While this improves usability, it can also create opportunities for attackers if a session token is captured or reused.
Conditional Access policies allow organizations to tighten this behavior and treat every authentication event as a new verification opportunity. Instead of trusting a previously issued session, the identity platform evaluates the request again before granting access.
This policy introduces two important security controls that work together. First, users must complete multifactor authentication. Second, the authentication session does not persist between sign-ins. Every access attempt must be verified again.
Together these controls ensure that access to the protected cloud application always requires fresh identity verification, reinforcing the principle that identity assurance should never rely solely on historical authentication.
his Policy in One Line
This Conditional Access MFA Every Sign-In policy requires multifactor authentication and forces users to authenticate again every time access to the protected application is requested.
What This Conditional Access Policy Does
The Conditional Access MFA Every Sign-In policy introduces a strict identity verification model. Instead of allowing authentication sessions to persist across multiple access attempts, the policy requires a full authentication process every time the protected application is accessed.
When a user attempts to sign in, the Conditional Access engine evaluates the request. If the policy conditions match, the user must complete multifactor authentication using one of the supported strong authentication methods. This ensures that access is not granted based on a single credential alone.
The policy also introduces a session control that eliminates session persistence. Even after successful authentication, the system does not rely on previously issued tokens for future access attempts. Each new sign-in request requires both primary and secondary authentication again.
This design significantly strengthens identity assurance. It ensures that every access request is treated as a fresh authentication event rather than an extension of a previously trusted session.
Who the Policy Applies To
The Conditional Access MFA Every Sign-In policy applies broadly to all users within the tenant environment. By targeting all identities, the design ensures that the authentication requirement is applied consistently whenever the protected application is accessed.
This type of configuration is often used when the protected service represents a sensitive management or security platform. In these situations, organizations prefer consistent authentication enforcement rather than selectively targeting specific user populations.
At the same time, the policy includes exclusion groups. Organizations commonly use these exclusion groups to support controlled exception management through approval workflows or time-based access. This approach ensures that operational continuity can be maintained while the primary security control remains broadly enforced.
By applying the rule to the entire user population and managing exceptions through dedicated groups, the design maintains a clear and predictable access model while still allowing carefully governed flexibility.
What Apps and Services the Policy Protects
This Conditional Access MFA Every Sign-In policy protects a specific cloud application within the Microsoft Entra ecosystem. Access requests targeting that application trigger the Conditional Access evaluation process.
When a user attempts to authenticate to the application, the identity platform checks whether the conditions defined in the policy apply. If they do, the access attempt moves through the policy’s authentication requirements and session controls before a token is issued.
Targeting a single application allows security teams to introduce strong authentication behavior where it matters most. Certain services may represent administrative interfaces, configuration platforms, or management portals that carry elevated security risk.
By focusing the policy on the protected application, the organization ensures that the strict authentication model is enforced precisely where strong identity verification is most important.
Platforms, Devices, and Client Apps in Scope
The Conditional Access MFA Every Sign-In policy evaluates access attempts from both browser sessions and modern client applications. This means that authentication requests originating from web interfaces, desktop applications, or mobile apps all fall within the scope of the policy.
By covering these client application types, the design ensures that the authentication requirement cannot be bypassed simply by switching access methods. Whether a user signs in through a web browser or through a modern client application, the same Conditional Access evaluation takes place.
No specific platform or device restrictions are defined in the policy configuration. As a result, the authentication requirement applies consistently regardless of the operating system or device used.
This approach keeps the policy focused on identity verification rather than device posture. The design decision prioritizes strong authentication controls as the primary mechanism for protecting access.
How Access Is Decided
Access decisions in the Conditional Access MFA Every Sign-In policy are based on the requirement for strong authentication. When a sign-in attempt occurs, the Conditional Access engine evaluates the request against the defined policy conditions.
If the request targets the protected application and the user falls within the included scope, the system enforces multifactor authentication. The authentication strength requirement ensures that users must provide more than a single credential before access can be granted.
The policy supports multiple authentication combinations capable of satisfying multifactor authentication. These combinations may include modern authentication methods such as authenticator-based verification, hardware security keys, or other supported strong authentication approaches.
Once the multifactor authentication requirement is satisfied, the identity platform proceeds to apply the session control behavior defined in the policy.
What the User Experience Looks Like During Sign-In
From the user perspective, the Conditional Access MFA Every Sign-In policy creates a very clear authentication experience. Each time the protected application is accessed, the sign-in process requires identity verification.
The user first completes the primary authentication step. Immediately after this, the multifactor authentication challenge is triggered, requiring the user to confirm their identity using one of the supported strong authentication methods.
After successful authentication, access is granted to the application. However, the authentication session does not persist for future access attempts. If the user signs out, reopens the application, or starts a new session, the authentication process is repeated.
While this experience introduces additional authentication prompts, it ensures that every access request is validated with fresh identity verification.
Why This Policy Matters for Security and the Business
Identity sessions are one of the most common targets for modern attackers. If an authentication token can be reused without reauthentication, it can become a powerful tool for unauthorized access.
The Conditional Access MFA Every Sign-In policy directly addresses this risk. By requiring multifactor authentication and eliminating persistent sign-in sessions, the policy reduces the window of opportunity for session-based attacks.
From a business perspective, this design is especially valuable for applications that control sensitive configurations, administrative capabilities, or security operations. Continuous identity verification ensures that access is always tied to an actively verified user.
The policy therefore strengthens both security posture and operational trust by ensuring that identity assurance remains current during every access attempt.
Is This a Foundational or Must-Have Policy?
The Conditional Access MFA Every Sign-In policy is typically considered a specialized protection policy rather than a universal baseline control. While multifactor authentication is widely adopted across organizations, forcing reauthentication for every access request is a more restrictive configuration.
This design is most commonly applied to applications that require heightened identity assurance. Administrative consoles, management platforms, and security tools often fall into this category.
By limiting session persistence and requiring fresh authentication, organizations ensure that high-risk access paths always involve active user verification.
In environments where strong identity assurance is required, this type of policy plays a critical role in preventing session reuse and strengthening authentication integrity.
Important Design Choices and Things to Notice
One of the most important design decisions in this Conditional Access MFA Every Sign-In policy is the use of authentication strength requirements to enforce multifactor authentication. This ensures that only authentication combinations capable of delivering strong identity assurance can satisfy the policy.
Another notable design choice is the use of sign-in frequency set to every authentication event. Instead of allowing session tokens to persist across interactions, the policy requires both primary and secondary authentication each time access is attempted.
The policy also applies consistently across browser sessions and modern client applications. This prevents users from bypassing the authentication requirement by switching between application types.
Together these design elements create a policy that prioritizes identity assurance over convenience.
Conditional Access Design Principles Behind This Policy
The Conditional Access MFA Every Sign-In policy reflects several core identity security principles commonly used in modern zero trust architectures.
First, the policy assumes that authentication trust should be continuously verified. Instead of relying on previously issued tokens, each access attempt must prove the user’s identity again.
Second, the policy enforces strong authentication through multifactor verification. This reduces the likelihood that compromised credentials alone can be used to gain access.
Third, the policy focuses on protecting a specific application rather than applying universal restrictions across the entire environment. This allows security teams to apply the strongest protections where the impact of compromise would be greatest.
These principles align closely with modern identity security strategies built around continuous verification and strong authentication.
Final Thoughts
The Conditional Access MFA Every Sign-In policy demonstrates how Conditional Access can be used to strengthen authentication assurance through session control and multifactor verification.
By requiring users to authenticate every time they access the protected application, the policy eliminates the risks associated with persistent authentication sessions. Combined with multifactor authentication, this creates a strong identity verification model that significantly reduces opportunities for session misuse.
Although this approach introduces additional authentication prompts, it delivers a clear security benefit for applications that require the highest level of protection.
In environments where identity assurance is critical, policies like this play an essential role in ensuring that every access request is verified, authenticated, and trusted.