Conditional Access Location Blocking Explained
Introduction
Conditional Access location blocking is often introduced after organizations discover that identity attacks rarely originate from expected places. Security teams may suddenly see sign-ins appearing from regions where the business has no presence. Those events raise an immediate question: should users even be able to authenticate from those locations in the first place?
This is where Conditional Access becomes a powerful design tool. Instead of reacting to suspicious sign-ins after they occur, administrators can define clear boundaries that determine where authentication is allowed and where it is not. By evaluating the geographic origin of a sign-in request, the platform can stop access attempts before any application session begins.
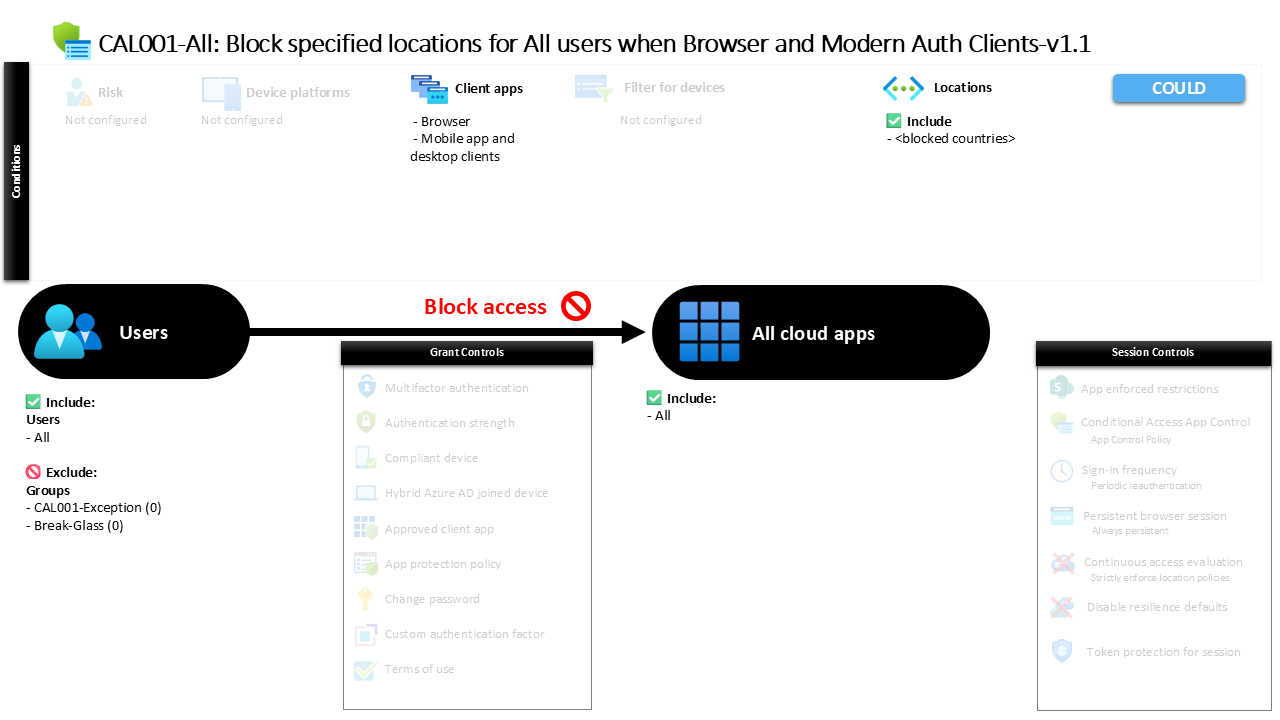
The policy explained in this article demonstrates that exact strategy. It introduces a location-based restriction that evaluates every sign-in from browser sessions and modern authentication clients and blocks access when the request originates from a specified location. The goal is simple but important: eliminate an entire class of risky sign-in attempts before they reach protected services.
This Policy in One Line
This Conditional Access location blocking policy stops users from signing in to protected services when authentication originates from a specified location.
What This Conditional Access Policy Does
The design intention of this policy is to enforce geographic access boundaries within the identity platform. Conditional Access evaluates the location of each authentication request and determines whether that location should be allowed to proceed.
In this configuration, the rule targets sign-ins originating from a defined location and applies a block control. When the policy conditions are met, authentication does not proceed and access to services is denied immediately. Because the control is a direct block action, there is no opportunity for additional authentication or device verification. The session simply does not continue.
This approach reflects a common identity protection strategy. Rather than relying solely on detection mechanisms such as risk scoring or anomaly monitoring, organizations can eliminate known high-risk sign-in origins entirely. By doing so, they reduce the attack surface and prevent automated credential attacks that frequently originate from specific geographic regions.
From a security architecture perspective, this policy acts as a perimeter control within Microsoft Entra ID. It defines where authentication should never occur and enforces that rule consistently across modern sign-in flows.
Who the Policy Applies To
The policy is designed to apply broadly across the user population. It evaluates sign-ins for all users within the environment, ensuring that the location restriction is not limited to specific departments or identity groups.
At the same time, the configuration contains exclusion groups. Organizations commonly use exclusion groups to support controlled exception management through approval workflows or time-based access. This allows security teams to temporarily exempt certain identities when legitimate access from restricted locations is required.
This design pattern is widely used in enterprise Conditional Access deployments. Instead of weakening a policy for everyone, exceptions are managed through dedicated groups that can be reviewed, approved, and audited. That approach maintains strong baseline protections while still allowing operational flexibility when necessary.
The overall result is a policy that protects the majority of the environment while providing a structured way to handle legitimate exceptions without compromising the broader security model.
What Apps and Services the Policy Protects
The policy protects access across the entire application landscape connected to the identity platform. Every authentication request directed toward integrated services is evaluated under the same location restriction.
From a design perspective, applying the rule broadly simplifies the security model. Instead of defining location restrictions for individual services, the organization establishes a universal rule that applies consistently to all protected applications.
This approach reduces configuration complexity and eliminates the risk of gaps where certain services might remain accessible from restricted locations. Every authentication request is evaluated under the same principle: if the sign-in originates from the defined location, access is blocked.
In modern identity architectures, this kind of broad protection is often preferred. Applications are increasingly interconnected, and users frequently move between services during a session. A universal Conditional Access rule ensures the same protection follows the identity regardless of which service is being accessed.
Platforms, Devices, and Client Apps in Scope
The policy focuses specifically on sign-ins that originate from browser sessions and modern authentication clients. These two client categories represent the majority of interactive authentication activity in modern cloud environments.
Browser-based access typically occurs when users sign in to web portals or web-based productivity services. Modern authentication clients represent desktop and mobile applications that use secure authentication protocols to obtain access tokens.
By targeting both client categories, the policy ensures that the location restriction applies across common access paths. Whether a user attempts to sign in through a browser window or through an application that relies on modern authentication protocols, the same location evaluation takes place.
This design choice closes potential gaps that might appear if only one client type were evaluated. Attackers frequently test multiple authentication methods when attempting to gain access. Ensuring that both browser and modern client sign-ins are covered strengthens the effectiveness of the location-based control.
How Access Is Decided
Conditional Access evaluates several conditions during every sign-in attempt. In this policy, the most important factor is the originating location of the authentication request.
When a user initiates sign-in, the identity platform determines the geographic location associated with the request. If the location matches the defined location condition within the policy, the rule is triggered.
Once the condition is met, the grant control configured in the policy is applied. In this case, the control enforces a direct block action. Because the control does not offer alternative authentication paths, the sign-in attempt ends immediately.
This evaluation happens in real time during the authentication process. The identity platform analyzes the request before any application session is created. As a result, blocked sign-ins never progress into a partially authenticated state.
From a design standpoint, this behavior is important. It ensures that access decisions occur at the identity layer, preventing downstream applications from ever receiving an authentication token when the location rule is violated.
What the User Experience Looks Like During Sign-In
From the user’s perspective, the experience is straightforward. A sign-in attempt begins normally when credentials are entered or when an application initiates authentication.
However, once the identity platform evaluates the location condition and detects that the request originates from the restricted location, the process stops. The authentication flow does not continue to application access.
Users attempting to sign in from permitted locations will never encounter this restriction and will proceed through the standard authentication experience. Only sign-ins originating from the specified location trigger the block action.
This clear separation between allowed and blocked sign-in origins simplifies the user experience. Instead of presenting additional verification steps or complex remediation paths, the system communicates that access from that location is not permitted.
In practice, this often encourages users to authenticate from trusted networks or known geographic regions aligned with organizational security policy.
Why This Policy Matters for Security and the Business
Location-based access control plays an important role in modern identity protection strategies. Many credential attacks originate from automated infrastructure operating in known geographic regions.
By defining a policy that blocks authentication from specific locations, organizations remove those attack origins entirely from the sign-in equation. Even if attackers possess valid credentials, the identity platform prevents them from establishing an authenticated session.
This significantly reduces the effectiveness of credential harvesting campaigns and password spray attacks that rely on large-scale automation.
From a business perspective, the policy also supports regulatory and compliance requirements. Some organizations must restrict where authentication may occur due to data protection regulations, contractual obligations, or geopolitical risk considerations.
Conditional Access location blocking therefore becomes both a security control and a governance mechanism. It allows organizations to enforce identity boundaries that align with both operational security and regulatory expectations.
Is This a Foundational or Must-Have Policy?
Location-based restrictions are commonly considered part of a foundational Conditional Access strategy. They address one of the simplest and most effective identity protection opportunities: restricting where authentication is allowed to originate.
While not every organization blocks the same locations, most mature Conditional Access designs include at least some form of geographic control. These rules often complement other controls such as risk evaluation, device compliance requirements, and authentication strength enforcement.
Because location evaluation occurs early in the authentication process, it serves as an efficient filter for suspicious sign-ins. Many high-risk authentication attempts can be stopped before additional security controls even need to be evaluated.
For this reason, location-based blocking policies are frequently among the first Conditional Access rules implemented in a new identity security architecture.
Important Design Choices and Things to Notice
Several design choices stand out in this policy configuration. First, the rule applies broadly to the user population while allowing controlled exclusions. This indicates that the location restriction is intended as a baseline protection rather than a niche control for specific roles.
Second, the policy targets both browser and modern authentication clients. This ensures that the restriction applies consistently regardless of how users attempt to authenticate.
Third, the enforcement action is a direct block. Unlike policies that require additional verification steps, this rule simply stops authentication when the condition is met. That design emphasizes prevention rather than remediation.
Together, these design elements create a clear and predictable access model. Users can authenticate normally from permitted locations, while sign-ins originating from the restricted location are consistently denied.
Conditional Access Design Principles Behind This Policy
This policy reflects several key principles that guide effective Conditional Access design.
One principle is attack surface reduction. Instead of responding to threats after they appear, the policy proactively removes an entire class of risky sign-in origins.
Another principle is consistency. By applying the rule across all users and all applications, the organization ensures that identity protection does not vary depending on which service a user attempts to access.
Finally, the policy demonstrates the concept of layered identity security. Location-based blocking operates alongside other Conditional Access controls to form a broader identity protection framework. Each control addresses a different risk signal, strengthening the overall access decision.
When these principles are combined, Conditional Access becomes more than a configuration feature. It becomes a structured security architecture that governs how identities interact with cloud services.
Final Thoughts
Conditional Access location blocking represents one of the most direct ways to reduce identity risk. By evaluating the origin of every sign-in request and denying access from restricted locations, organizations can prevent large volumes of malicious authentication attempts.
The policy explained in this article demonstrates a straightforward implementation of that concept. It applies location evaluation broadly, covers the most common authentication clients, and enforces a clear block decision when the defined location condition is met.
In modern identity environments where authentication occurs from anywhere in the world, defining where access should not occur can be just as important as defining where it should.
Conditional Access provides the mechanism to enforce those boundaries reliably, turning geographic awareness into a powerful layer of identity protection.