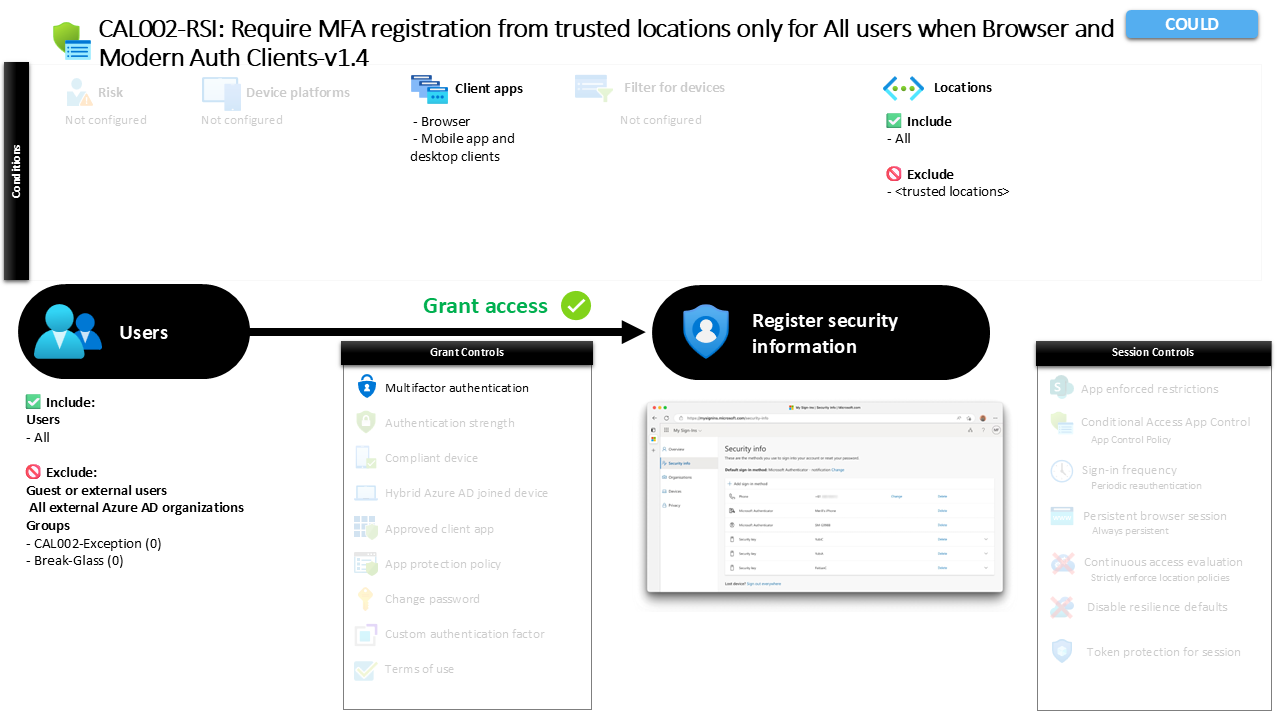
Conditional Access MFA Registration Security Guide CAL002-RSI Require MFA registration from trusted locations only for All users when Browser and Modern Auth Clients
Introduction
Conditional Access MFA registration is designed to address a common identity security challenge: controlling where users can register authentication methods. When users add or update security information such as MFA methods, they are effectively modifying the mechanisms that protect their identity. If that process happens from an untrusted location, it becomes an attractive target for attackers attempting to hijack accounts.
This is why organizations often restrict the environments from which security information can be registered. Conditional Access provides the ability to evaluate the sign-in context before allowing that process to proceed. In this design, the policy ensures that when users attempt to register authentication methods from locations outside trusted networks, additional identity verification is required.
The result is a security control that protects one of the most sensitive moments in the identity lifecycle. By placing conditions around where MFA registration can occur, the organization ensures that authentication method enrollment happens in a controlled and verified environment.
This Policy in One Line
This policy requires additional identity verification when users attempt to register authentication methods from locations that are not recognized as trusted networks.
What This Conditional Access Policy Does
The purpose of this Conditional Access design is to protect the process of registering security information. Registration events occur when users enroll authentication methods that will later be used for identity verification. Because these methods become part of the authentication chain, the registration process itself must be treated as a sensitive security event.
The policy monitors attempts to register security information and evaluates the context of the request. Instead of applying controls to general application access, the policy specifically targets the action of registering authentication methods. When this event occurs, Conditional Access evaluates the sign-in conditions and determines whether additional verification is required.
When the request originates from a location outside the trusted network boundary, the system requires multifactor authentication before the registration process can proceed. This ensures that the person performing the registration has already verified their identity through an additional authentication step.
This approach reinforces the integrity of authentication method enrollment and reduces the likelihood that an attacker can register new authentication methods for a compromised account.
Who the Policy Applies To
This policy applies broadly across the organization by targeting all users within the directory. By applying the rule at this level, the organization ensures that authentication method registration is consistently protected regardless of the user’s role or department.
External identities are excluded from this evaluation. This means that the policy focuses specifically on internal user accounts while leaving guest and external collaboration identities outside the scope of this control. This design choice often reflects the fact that external identities may already be governed by their own identity providers.
In addition, specific groups are excluded from the policy. Organizations commonly maintain such exclusion groups to support controlled exception management. These groups allow administrators to temporarily bypass the policy for testing, emergency scenarios, or operational troubleshooting through approval workflows or time-based access procedures.
By structuring the scope in this way, the organization achieves wide coverage while still maintaining operational flexibility where it is needed.
What Apps and Services the Policy Protects
Instead of targeting a specific application or service, this policy protects a particular identity action: the registration of security information. This design focuses on the moment when users add or modify authentication methods associated with their account.
Conditional Access treats this registration activity as a protected operation because it directly affects how identities are verified during future sign-ins. By controlling this action, the organization protects the trustworthiness of the authentication system itself.
This approach reflects a modern identity security principle. Rather than securing only applications, organizations increasingly secure identity operations that can influence authentication behavior. Security information registration is one of the most important of these operations because it determines which authentication factors are associated with a user account.
Protecting this action ensures that authentication methods are registered only after the identity of the user has been verified under appropriate conditions.
Platforms, Devices, and Client Apps in Scope
The policy evaluates requests coming from browser sessions as well as modern authentication clients used by desktop and mobile applications. By covering both client categories, the organization ensures that the registration process cannot bypass Conditional Access simply by switching to a different sign-in method.
Browser-based access typically occurs when users visit identity management portals to add or modify authentication methods. Modern authentication clients represent applications that support modern authentication protocols and interact directly with Microsoft Entra for identity verification.
Including both access types closes a potential security gap. Without this coverage, attackers could attempt to exploit alternative sign-in channels to complete the registration process outside the intended security controls.
By ensuring that Conditional Access evaluates both browser and modern authentication clients, the policy enforces a consistent registration security posture regardless of how the user initiates the process.
How Access Is Decided
Conditional Access evaluates the location from which the registration request originates. The policy applies to all locations but excludes those that are defined as trusted networks. This effectively means that the rule activates when the request originates from a location that is not recognized as trusted.
When such a request occurs, Conditional Access requires multifactor authentication before the registration process can proceed. This additional verification step confirms the identity of the person attempting to modify authentication methods.
The evaluation sequence follows a straightforward logic. First, the system identifies that the user is attempting to register security information. Next, the location of the sign-in attempt is assessed. If the location falls outside the trusted network boundary, the policy requires multifactor authentication as a condition for continuing the process.
This decision model reinforces a common security principle: sensitive identity operations should require stronger verification when performed from higher-risk environments.
What the User Experience Looks Like During Sign-In
From the user’s perspective, the experience depends largely on where the registration attempt originates. If the user initiates the process from a trusted network, the registration flow proceeds normally without additional verification steps imposed by this policy.
If the same action occurs from a location that is not recognized as trusted, Conditional Access intervenes. Before the registration process can continue, the user is prompted to complete a multifactor authentication challenge.
This prompt verifies that the user still has access to an existing authentication factor before allowing new authentication methods to be registered. The additional step ensures that the registration process itself is protected by strong authentication.
Although this introduces a small amount of friction for users outside trusted locations, the experience remains straightforward and predictable. Users simply confirm their identity and then continue the registration process as intended.
Why This Policy Matters for Security and the Business
Authentication method registration is one of the most critical moments in identity security. If an attacker gains the ability to register new authentication factors for a compromised account, they can effectively establish persistent access to that identity.
This policy significantly reduces that risk by adding verification requirements when registration occurs from unfamiliar or potentially risky locations. The design ensures that attackers cannot easily manipulate authentication methods without first completing a multifactor challenge.
For the organization, this translates directly into stronger protection for user accounts and authentication infrastructure. It also supports broader identity security strategies that rely on multifactor authentication as a foundational control.
By securing the registration process itself, the organization ensures that authentication methods remain trustworthy and that the identity platform continues to operate as a reliable security boundary.
Is This a Foundational or Must-Have Policy?
Policies that protect authentication method registration are widely considered foundational in modern Conditional Access designs. The reason is simple: authentication methods define how identities are verified across the entire environment.
If attackers can manipulate those methods, many other security controls become ineffective. Protecting the registration process therefore safeguards the entire authentication framework.
This type of policy is often implemented early in Conditional Access deployments because it strengthens the integrity of multifactor authentication from the start. It ensures that authentication methods are only registered under verified conditions and that identity changes cannot occur unnoticed.
As organizations mature their identity security strategies, policies like this become a core component of a layered identity protection model.
Important Design Choices and Things to Notice
One of the most notable aspects of this design is its focus on location context. Instead of enforcing multifactor authentication during every registration event, the policy selectively requires it when the request originates outside trusted network boundaries.
This approach balances usability and security. Users working within trusted environments experience minimal disruption, while registration attempts from unknown locations trigger stronger verification.
Another important detail is the focus on the security information registration action rather than application access. By targeting the identity operation itself, the policy protects the moment when authentication methods are created or modified.
Finally, the inclusion of both browser sessions and modern authentication clients ensures that the registration process cannot bypass Conditional Access controls through alternative sign-in channels.
Together, these design decisions create a well-balanced policy that strengthens identity protection without unnecessarily disrupting normal user activity.
Conditional Access Design Principles Behind This Policy
Several core Conditional Access principles are reflected in this design. The first is context-based access control, where decisions are based on sign-in conditions such as location rather than static identity attributes alone.
Another principle is protection of identity lifecycle events. Registration of authentication methods represents a critical moment in the lifecycle of a user identity. Securing this event helps ensure that authentication remains trustworthy across the environment.
The policy also demonstrates the principle of adaptive verification. Instead of requiring multifactor authentication in every situation, the system applies stronger verification when the risk level increases, such as when the sign-in originates from outside trusted networks.
These principles align closely with modern zero trust identity strategies, where identity actions are continuously evaluated and protected based on context.
Final Thoughts
Conditional Access MFA registration policies protect one of the most sensitive identity operations in any environment. By controlling where authentication methods can be registered and requiring verification when requests originate outside trusted locations, organizations significantly reduce the risk of identity takeover.
The design presented here shows how Conditional Access can protect identity lifecycle events without disrupting normal user activity. Users working within trusted environments can complete the registration process smoothly, while requests from unfamiliar locations require additional verification.
This balance between security and usability is a hallmark of effective Conditional Access design. By securing authentication method registration with contextual verification, organizations strengthen the foundation of their identity protection strategy and ensure that multifactor authentication remains a reliable defense against account compromise.