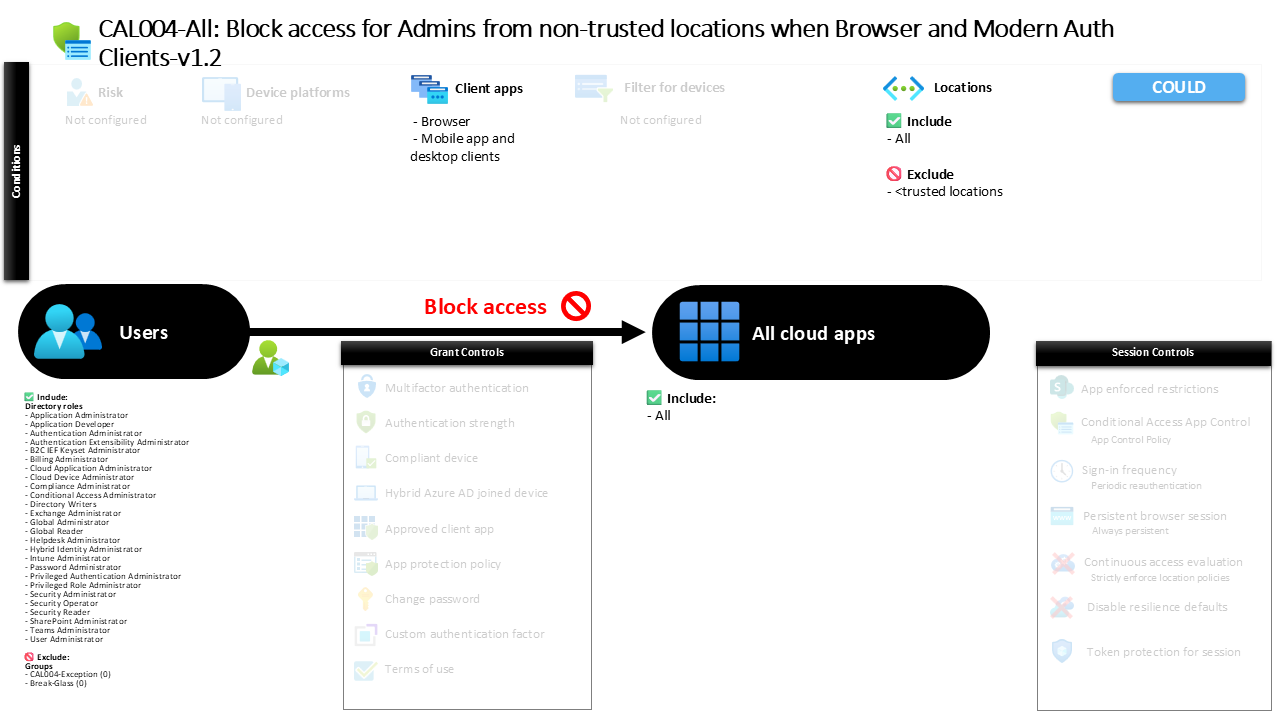
Conditional Access Admin Location Blocking Explained CAL004-All Block access for Admins from non-trusted locations when Browser and Modern Auth Clients
Introduction
Conditional Access admin location blocking often becomes necessary after organizations discover how frequently privileged accounts are targeted from unexpected locations. Attackers know that administrator identities hold the keys to the entire environment, and once those identities are compromised, security controls across Microsoft 365 can be altered or removed within minutes.
This policy addresses that exact challenge by preventing administrator access when the sign-in originates from locations that are not recognized as trusted. Instead of relying solely on authentication strength, the design introduces geographic and network awareness into the decision process. Conditional Access evaluates where the request originates before allowing privileged access to any application.
The result is a policy that quietly protects the most sensitive identities in the environment. Even if credentials are compromised, administrative access attempts from unknown locations are stopped before they can reach the protected resources.
This Policy in One Line
This Conditional Access policy blocks administrator sign-ins to applications when the request originates from locations that are not defined as trusted network locations.
What This Conditional Access Policy Does
This policy introduces a strict access boundary around privileged identities by enforcing location-based access restrictions. When an administrator attempts to sign in to an application, Conditional Access evaluates whether the request originates from a location that the organization recognizes as trusted.
If the sign-in originates from a trusted network location, access evaluation continues normally. When the request originates from any other location, the policy intervenes and blocks the sign-in attempt entirely. Rather than requesting additional authentication or applying session restrictions, the configuration denies the request outright.
This design is deliberate. Administrative privileges allow changes to identity systems, device management, and application access controls. Because of that level of influence, organizations often treat location validation as a hard boundary rather than a conditional requirement. By enforcing a strict block outside trusted networks, the policy significantly reduces the attack surface around privileged identities.
Who the Policy Applies To
The policy targets privileged identities by applying its conditions to administrative roles within the identity platform. Instead of selecting individual users or static groups, the configuration focuses on role-based targeting.
This approach ensures that the protection automatically follows the privilege rather than the individual identity. When a user is assigned a privileged administrative role, the policy immediately applies to that account without additional configuration work. If that role assignment is later removed, the policy no longer applies.
Organizations often choose this design because administrative privileges frequently change through role assignments. By tying Conditional Access enforcement to roles instead of users, security teams avoid gaps that can occur when identities move between operational responsibilities. The policy therefore protects the privilege layer itself, ensuring that elevated access remains tightly controlled regardless of who currently holds those roles.
What Apps and Services the Policy Protects
The scope of this policy extends across all applications integrated with the identity platform. Instead of targeting specific services, the configuration applies the protection broadly so that any application requiring authentication is included within the policy evaluation.
This design ensures that administrator accounts cannot bypass the location restriction simply by accessing a different service. Whether the administrator attempts to sign in to a management portal, administrative interface, or application connected through the identity platform, Conditional Access evaluates the request before granting access.
By covering all applications, the policy ensures consistent enforcement of the location requirement. Privileged access cannot move laterally between services to avoid the restriction. The security model therefore treats administrator authentication as a single protected pathway rather than multiple independent sign-in experiences.
Platforms, Devices, and Client Apps in Scope
The policy evaluates access attempts originating from browser sessions as well as modern authentication clients used by mobile and desktop applications. These client types represent the primary ways administrators interact with cloud services and management interfaces.
Browser access typically includes web-based portals used for administrative tasks, while modern authentication clients represent applications that authenticate using contemporary identity protocols. By covering both categories, the policy ensures that administrative access is consistently evaluated regardless of how the user connects.
This design prevents situations where administrators might bypass location restrictions simply by switching client types. Whether access occurs through a web interface or through a desktop or mobile client application, the same Conditional Access logic applies. The policy therefore closes the gap between different authentication experiences and ensures consistent enforcement across the administrator sign-in landscape.
How Access Is Decided
Access decisions in this policy revolve around a single critical condition: the origin of the sign-in request. Conditional Access evaluates the location associated with the authentication attempt and compares it to the list of trusted network locations defined within the environment.
If the request originates from a trusted location, Conditional Access continues evaluating the sign-in normally. However, when the request originates from a location that is not recognized as trusted, the policy immediately applies a blocking control.
Because the control is a direct access block, no additional authentication steps or session limitations are offered. The sign-in request simply cannot proceed. This design reflects a common security principle in privileged access protection. Instead of introducing friction that an attacker might still overcome, the system removes the access path entirely when the location condition fails.
What the User Experience Looks Like During Sign-In
From the user’s perspective, the sign-in experience remains unchanged when access originates from a trusted network location. Authentication proceeds normally and administrators can access their tools and applications without additional prompts or restrictions.
When the sign-in originates from an untrusted location, the experience changes dramatically. Conditional Access intercepts the authentication attempt during the evaluation stage and denies the request before access is granted. The administrator receives a message indicating that the sign-in cannot continue due to the organization’s access policy.
This behavior reinforces an important operational expectation. Administrative work must occur from approved network locations that the organization recognizes as secure. The policy therefore communicates a clear boundary to administrators while simultaneously protecting the environment against suspicious access attempts.
Why This Policy Matters for Security and the Business
Privileged identities represent one of the most valuable targets in any cloud environment. Attackers frequently focus on administrator credentials because compromising a single privileged account can provide control over identity, security policies, and application access across the organization.
This policy directly addresses that threat by narrowing the environments from which privileged access is allowed. Even if credentials are exposed through phishing or credential theft, attackers attempting to sign in from external locations encounter a hard security barrier.
From a business perspective, this significantly reduces the risk of catastrophic identity compromise. Security teams gain confidence that administrative actions can only originate from known network environments, while auditors can see clear evidence that privileged access is tightly controlled. The policy therefore strengthens both operational security and governance expectations.
Is This a Foundational or Must-Have Policy?
Policies that protect administrator identities are typically considered foundational within Conditional Access design frameworks. Privileged accounts hold the authority to modify security settings, grant permissions, and access sensitive information across the environment.
Because of that influence, organizations frequently implement strong protections around administrator authentication early in their Conditional Access deployment strategy. Location-based restrictions represent one of the most reliable controls in this category.
By limiting where administrative access can originate, the policy establishes a clear operational boundary around privileged activity. This foundational protection works alongside other identity safeguards to ensure that elevated privileges remain tightly controlled within trusted environments.
Important Design Choices and Things to Notice
One notable aspect of the policy design is its reliance on trusted network locations as the defining access boundary. Rather than allowing administrative access from any location with additional authentication steps, the configuration treats trusted networks as the only acceptable environment for privileged activity.
Another design detail is the role-based targeting approach. By applying the policy to administrative roles instead of individual users, the security control automatically follows privilege assignments. This ensures that newly assigned administrators immediately fall under the protection of the policy.
The policy also blocks access outright rather than introducing additional authentication requirements. This reflects a strict security posture where certain risk conditions are considered unacceptable rather than negotiable. The decision simplifies enforcement and removes potential bypass scenarios that might exist with softer controls.
Conditional Access Design Principles Behind This Policy
Several well-established Conditional Access design principles appear within this policy. The first is the protection of privileged identities through layered identity controls. Administrator accounts receive stricter enforcement because they represent higher-impact security risks.
Another principle is environmental trust validation. By verifying that sign-ins originate from trusted network locations, the system introduces contextual awareness into the authentication decision. This reduces reliance on credentials alone and incorporates environmental signals into the security evaluation.
Finally, the policy reflects the principle of minimizing privileged attack surfaces. Instead of allowing administrative access from anywhere on the internet, the design restricts access pathways to controlled environments. By shrinking the number of acceptable access scenarios, the policy makes it significantly harder for attackers to exploit compromised credentials.
Final Thoughts
Conditional Access admin location blocking is a powerful example of how contextual access control can strengthen identity security. By restricting privileged access to trusted network environments, the policy establishes a clear boundary around administrator activity.
The design reduces the likelihood that compromised credentials can be used to access critical systems from unexpected locations. Even when attackers obtain valid authentication information, the environment itself becomes a protective control that prevents privileged access from outside trusted networks.
Policies like this illustrate how Conditional Access moves identity protection beyond passwords and authentication methods. By combining identity signals with environmental context, organizations create security controls that are far more resilient against modern attack techniques.