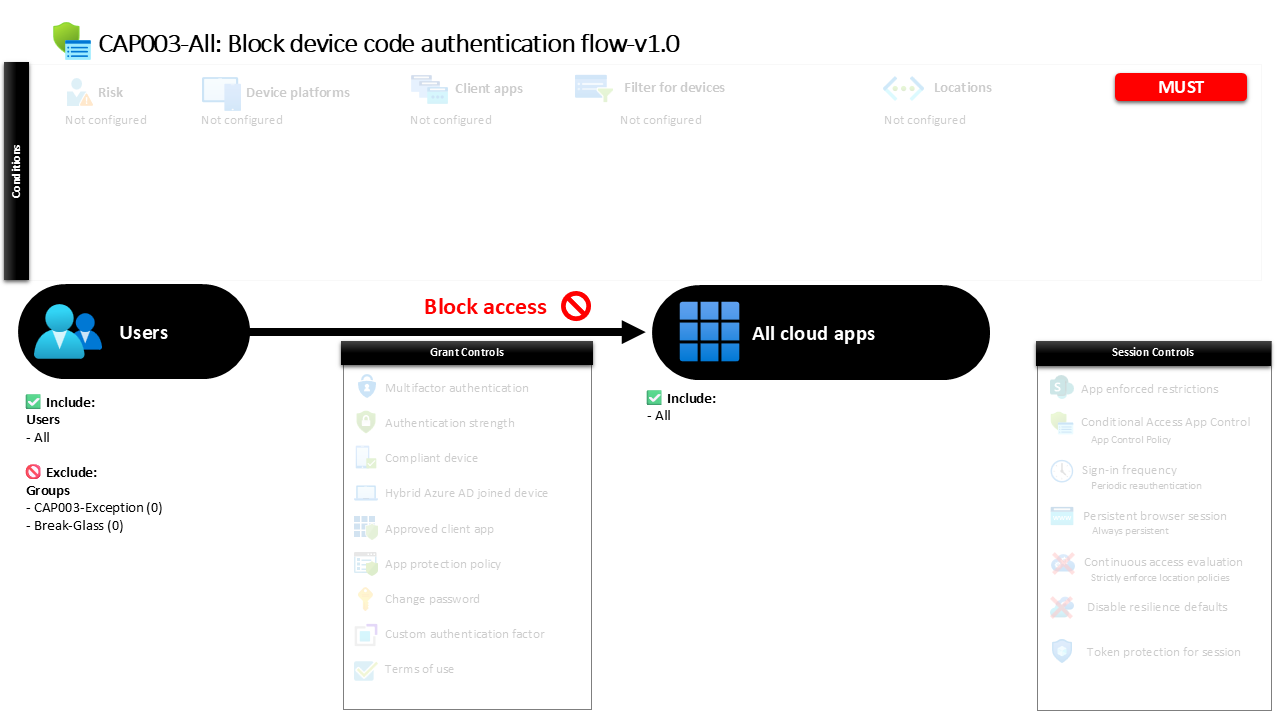
Conditional Access Device Code Flow Block Explained CAP003-All Block device code authentication flow
Introduction
Conditional Access device code flow block policies exist to stop a subtle but powerful authentication path that attackers increasingly exploit. Device code authentication allows a user to sign in on one device while completing authentication on another. The process was originally designed for devices with limited input capabilities, such as smart TVs or command line tools. However, the same mechanism can also be abused during phishing campaigns or token theft scenarios.
A Conditional Access device code flow block policy addresses this risk directly by preventing this authentication method from being used inside the identity environment. Instead of trying to control the device or enforce additional requirements, the design simply removes the entire authentication pathway from the organization’s sign-in options.
This approach reflects a broader security philosophy within Microsoft Entra ID: if an authentication flow is rarely needed but frequently abused, blocking it outright can significantly reduce the attack surface. In this case, the policy acts as a preventative control that protects all identities and all applications from a risky authentication mechanism.
This Policy in One Line
This Conditional Access policy blocks the device code authentication flow for all users and all applications to eliminate a commonly abused sign-in method.
What This Conditional Access Policy Does
The intention behind this Conditional Access design is straightforward: prevent sign-ins that rely on the device code authentication method. Instead of evaluating device trust, location, or risk signals, the policy targets a specific authentication transfer method and stops it from completing.
When a sign-in attempt uses the device code flow, Conditional Access evaluates the authentication request during the sign-in process. Because the policy explicitly blocks this transfer method, the authentication process is terminated before access can be granted to any service.
This approach ensures that the device code mechanism cannot be used to obtain tokens in the tenant. Since authentication tokens are often the target of modern attacks, removing an unnecessary token acquisition path helps reduce exposure.
In practical terms, the policy functions as a gatekeeper for authentication behavior rather than for users, devices, or applications. The design reflects a proactive security stance: eliminate risky authentication flows instead of trying to secure them after the fact.
Who the Policy Applies To
The policy is designed to apply broadly across identities. All users fall within the scope of the control, which ensures that the device code authentication pathway is consistently restricted across the environment.
Broad user targeting is intentional in this type of policy. Authentication flow protections are most effective when they apply universally, because attackers often attempt to exploit the weakest identity rather than the most privileged one.
There are specific exclusions configured through dedicated identity groups. Organizations often maintain these exclusion groups to support controlled exception management. Access to such groups is typically governed through approval workflows, change management procedures, or temporary access mechanisms. This allows security teams to accommodate legitimate operational needs while keeping the protection active for the wider identity population.
This structure maintains the integrity of the security design while still providing flexibility when rare scenarios require temporary exceptions.
What Apps and Services the Policy Protects
This policy protects all cloud applications within the Microsoft Entra ID environment. Rather than focusing on a single service such as collaboration tools or administrative portals, the design ensures that the restriction applies across the entire application ecosystem.
From a security architecture perspective, targeting every application is important. Device code authentication is not tied to a specific service. It can be used by scripts, command line tools, and applications that request delegated access tokens. Because of this flexibility, attackers can leverage the flow to gain access to multiple services once authentication succeeds.
By applying the policy universally, the organization ensures that no application can accept a device code authentication request. The restriction therefore protects the full identity perimeter instead of leaving gaps between individual services.
This design aligns with a core Conditional Access principle: when controlling authentication methods, enforce the rule consistently across all applications.
Platforms, Devices, and Client Apps in Scope
The policy evaluates authentication attempts originating from all client application types. This ensures that the restriction applies regardless of whether the sign-in originates from a browser, a mobile application, a desktop client, or another authentication client.
The design does not focus on specific operating systems, device platforms, or device management states. Instead, it concentrates entirely on the authentication transfer method itself.
This distinction is important. Device code authentication does not depend on the platform from which the request originates. A command line tool running on a workstation, a development script, or a remote system could all initiate the same authentication process.
By evaluating all client app types collectively, Conditional Access ensures that the device code flow cannot bypass the restriction through a different client interface. The result is a comprehensive control that focuses on authentication behavior rather than endpoint characteristics.
How Access Is Decided
Access decisions in this policy are determined by evaluating the authentication transfer method used during the sign-in process. Conditional Access inspects the request and identifies whether the device code authentication flow is being used.
If the sign-in relies on this transfer method, the policy immediately blocks the request. No additional conditions or grant requirements are evaluated because the design explicitly denies the authentication attempt.
This decision logic reflects a clear and deterministic rule. Instead of layering multiple conditions such as device compliance or multifactor authentication, the policy enforces a simple outcome: device code authentication is not permitted.
The advantage of this approach is predictability. Security teams can confidently state that tokens cannot be issued through this authentication pathway, which simplifies both risk analysis and incident investigation.
What the User Experience Looks Like During Sign-In
From the user’s perspective, the experience appears as a blocked authentication attempt during the device code sign-in process. Typically, device code authentication begins with a prompt instructing the user to enter a code on a separate authentication page.
When Conditional Access evaluates the request, the policy prevents the authentication from completing. The user is informed that access cannot be granted due to organizational security requirements.
For most users this behavior will never appear in normal workflows because device code authentication is not commonly used in everyday business applications. However, the restriction becomes visible if a user attempts to authenticate through developer tools, command line interfaces, or other systems that rely on the device code flow.
This ensures that the policy quietly protects the environment without interfering with standard productivity tools.
Why This Policy Matters for Security and the Business
Blocking device code authentication significantly reduces the risk of token-based attacks. The device code flow has historically been leveraged in phishing campaigns where attackers trick users into completing authentication on a separate device.
In these scenarios, the attacker initiates the authentication process and convinces the victim to enter a verification code. Once completed, the attacker receives the authentication token and gains access to cloud resources.
By eliminating this authentication pathway entirely, the policy removes an attack technique that is difficult for users to recognize during phishing attempts.
For the business, the benefit is clear. Identity protection becomes stronger without adding friction to normal sign-in experiences. Employees continue working as usual, while a potentially dangerous authentication mechanism is quietly disabled.
Is This a Foundational or Must-Have Policy?
This policy is widely considered a foundational Conditional Access control within modern Microsoft Entra ID security designs.
Organizations that adopt Zero Trust principles typically remove authentication flows that are unnecessary or prone to abuse. Device code authentication falls into that category for most environments, especially those that rely on standard modern authentication methods.
Because the restriction affects a specific authentication flow rather than a user scenario, it rarely disrupts legitimate workflows. This makes it an ideal candidate for baseline identity protection.
As a result, many security frameworks recommend blocking the device code flow unless a specific operational requirement demands its use.
Important Design Choices and Things to Notice
One notable aspect of the design is its simplicity. The policy does not rely on device compliance checks, multifactor authentication requirements, or risk evaluation. Instead, it focuses on the authentication transfer method itself.
Another key design choice is the universal application scope. By targeting all users and all applications, the policy ensures that no authentication path remains exposed through the device code mechanism.
The presence of structured exclusion groups also indicates a mature governance approach. Security teams often maintain these groups to support controlled exceptions when specialized tools or automation workflows require temporary access to the blocked authentication method.
Together, these design choices show a balance between strong security controls and operational flexibility.
Conditional Access Design Principles Behind This Policy
Several Conditional Access design principles are visible in this configuration.
First is attack surface reduction. Instead of attempting to monitor or mitigate a risky authentication method, the policy removes it completely.
Second is consistency. Applying the restriction across all users and applications ensures that the identity environment behaves predictably and avoids security gaps.
Third is exception governance. By managing exclusions through controlled groups, organizations maintain the ability to support rare operational requirements without weakening the overall protection model.
These principles reflect the broader philosophy of Microsoft Entra ID security architecture: simplify authentication pathways while strengthening identity protections.
Final Thoughts
A Conditional Access device code flow block policy represents a quiet but powerful identity protection measure. It does not introduce new prompts, additional authentication requirements, or complex device evaluations. Instead, it removes an authentication mechanism that has proven vulnerable to abuse.
In a modern cloud environment where authentication tokens represent the keys to corporate data, eliminating risky token acquisition methods is a smart defensive strategy.
By blocking device code authentication entirely, organizations reinforce their identity perimeter and align their Conditional Access strategy with Zero Trust security practices.