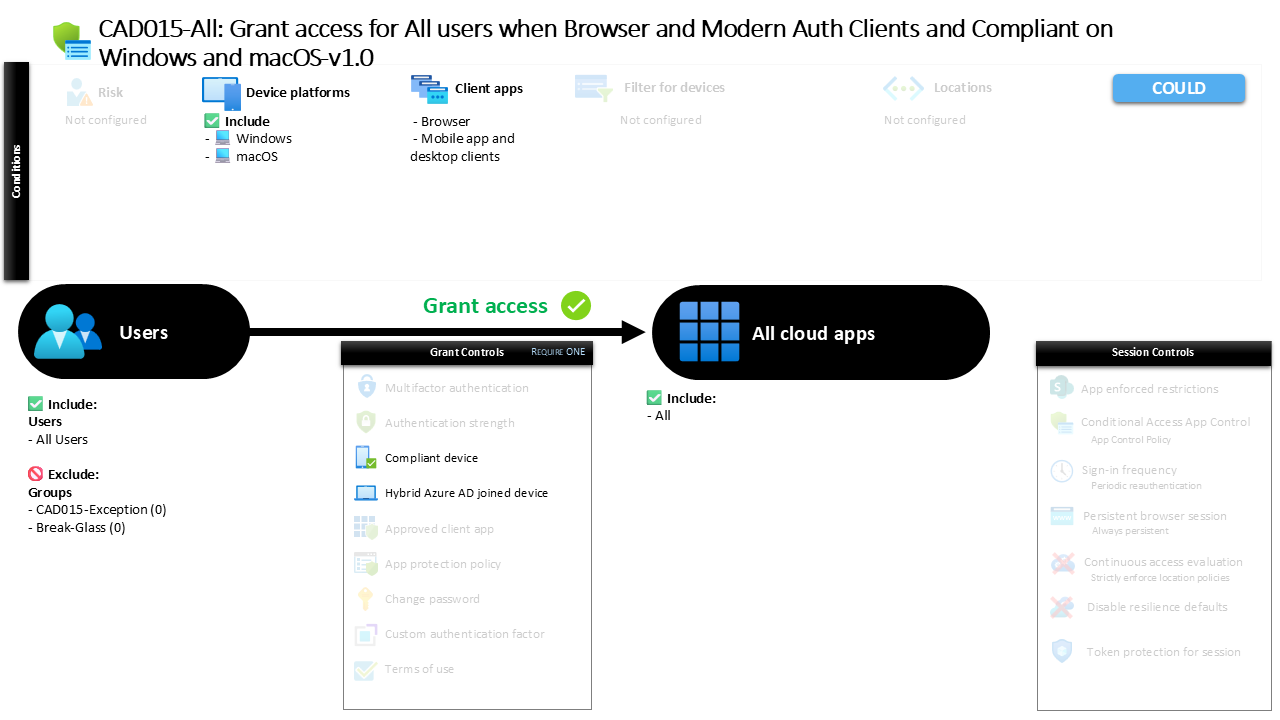
Conditional Access Compliant Device Access Policy CAD015-All Grant access for All users when Browser and Modern Auth Clients and Compliant on Windows and macOS
Introduction
Conditional Access compliant device policies exist to solve a common modern workplace challenge. Organizations want users to access cloud applications from anywhere, but they also need assurance that the device connecting to corporate resources meets security expectations. A personal device, an unmanaged laptop, or a system without proper configuration can quietly introduce risk even when the user identity itself is legitimate.
Conditional Access compliant device access addresses this challenge by introducing device posture as part of the sign-in decision. Instead of relying only on identity verification, the system also evaluates whether the device itself meets organizational standards before granting access.
This policy represents a clear example of how organizations enforce that principle. It ensures that access from Windows and macOS devices is permitted only when those devices meet specific trust requirements. By doing so, the design ties identity security and device security together as part of a unified access control strategy.
This Policy in One Line
This Conditional Access compliant device policy allows access to cloud applications only when users sign in from Windows or macOS devices that are either compliant or recognized as domain joined.
What This Conditional Access Policy Does
This policy introduces device trust as a requirement when users access applications through browsers or modern authentication clients. The intention is straightforward. Identity alone is not considered sufficient proof that access should be granted. The device used during sign-in must also demonstrate that it meets the organization’s security expectations.
Conditional Access evaluates the connection request and checks whether the device satisfies one of the permitted trust states. In this configuration, access is allowed when the device is recognized as compliant or when it is joined to the organization’s domain. Either condition indicates that the device is known and managed within the organization’s security ecosystem.
The policy therefore functions as a gatekeeper. If the device does not meet one of these requirements, the access request cannot satisfy the policy conditions. This design ensures that access decisions reflect both identity assurance and device trust.
Who the Policy Applies To
The policy targets a defined group of users rather than individual accounts. Using group-based targeting is a widely adopted Conditional Access design approach because it allows security teams to manage policy scope in a scalable and maintainable way.
Group targeting also allows the organization to gradually expand policy coverage. As more users are added to the group, they automatically become subject to the same Conditional Access protections without requiring individual policy adjustments.
The configuration also includes exclusion groups. These types of groups are commonly used to support controlled exception management. Organizations often maintain such groups so that specific accounts can temporarily bypass a policy when required, typically through approval workflows or limited-time access arrangements.
This structure reflects a common enterprise design pattern where security policies apply broadly but still allow structured operational flexibility when needed.
What Apps and Services the Policy Protects
This policy protects all applications integrated with the organization’s identity platform. Instead of targeting a specific service, the design applies the same device trust requirement across the full application landscape.
This approach simplifies security architecture. Rather than defining different device policies for each application, the organization enforces a consistent expectation that trusted devices must be used when accessing corporate resources.
Conditional Access evaluates every sign-in request to determine whether the device meets the policy requirements before the application session begins. If the device satisfies the policy conditions, access proceeds normally.
By protecting all applications under the same rule, the organization reduces complexity while maintaining a consistent security posture across its cloud environment.
Platforms, Devices, and Client Apps in Scope
This policy specifically evaluates sign-ins originating from Windows and macOS platforms. These platforms are often central to enterprise workstation environments, which makes them a logical focus for device trust enforcement.
Conditional Access evaluates both browser sessions and modern authentication clients. This means that the policy applies whether users access applications through a web interface or through desktop and mobile applications that rely on modern authentication protocols.
The design ensures that device trust requirements cannot be bypassed simply by switching access methods. Whether the user opens a browser or launches a desktop application, the same Conditional Access evaluation takes place.
By aligning platform conditions with client application types, the policy creates consistent enforcement across the most common enterprise access paths.
How Access Is Decided
When a sign-in occurs, Conditional Access evaluates whether the device meets one of the accepted trust states. In this configuration, access can be granted when the device is compliant or when the device is joined to the organization’s domain.
A compliant device generally indicates that the device meets the organization’s security policies, typically evaluated through device management and configuration compliance checks. A domain joined device indicates that the device is registered within the organization’s identity infrastructure.
The policy uses a logical OR decision between these conditions. That means the device only needs to satisfy one of the two trust indicators for the access request to succeed.
This approach balances security and usability. Devices that are either compliant or domain joined are recognized as trusted, allowing the organization to support multiple device management models while maintaining a controlled access posture.
What the User Experience Looks Like During Sign-In
From a user perspective, the experience remains largely invisible when the device already meets the required trust conditions. The sign-in process proceeds normally, and access to the requested application is granted without interruption.
Behind the scenes, however, Conditional Access evaluates the device state during the authentication flow. The system checks whether the device is recognized as compliant or joined to the domain. Only when one of these checks succeeds does the access request continue.
If the device does not meet the required conditions, the user will not be able to complete the sign-in process under this policy. This behavior ensures that only trusted devices can establish authenticated sessions with organizational resources.
By integrating the device evaluation into the sign-in flow, the organization enforces device trust without adding unnecessary complexity to the user experience.
Why This Policy Matters for Security and the Business
Device trust has become a fundamental element of modern identity security. In cloud environments where users work from multiple locations and devices, identity verification alone is no longer sufficient.
This policy reinforces the idea that secure access requires both a trusted identity and a trusted device. By requiring either compliance or domain membership, the organization ensures that devices interacting with corporate resources meet a baseline level of security assurance.
From a business perspective, this reduces the risk associated with unmanaged or unknown systems accessing sensitive data and applications. It also helps security teams maintain consistent governance over how devices interact with enterprise services.
Policies like this allow organizations to extend flexible access to users while maintaining strong device-level protections.
Is This a Foundational or Must-Have Policy?
A Conditional Access compliant device policy is widely considered a foundational component of a mature Conditional Access architecture. It introduces device trust into the authentication decision without creating excessive complexity.
Many organizations begin their Conditional Access journey by enforcing identity controls such as multifactor authentication. As security maturity increases, device posture becomes an equally important signal in the access decision.
Policies that evaluate device compliance or domain membership establish a clear trust boundary. Devices that meet the organization’s standards can interact with corporate services, while unmanaged or unknown systems cannot.
Because of this, compliant device policies are commonly included in baseline Conditional Access frameworks for modern enterprise environments.
Important Design Choices and Things to Notice
One notable design choice in this policy is the use of platform targeting. By focusing specifically on Windows and macOS, the organization ensures that the policy applies to the primary workstation environments used in enterprise settings.
Another key decision is the inclusion of both browser and modern authentication clients. This eliminates potential gaps where users might attempt to access applications through alternative client types that are not evaluated by the policy.
The use of a logical OR condition between compliant devices and domain joined devices is also significant. This design allows organizations to support both managed compliance models and traditional domain-based device trust simultaneously.
Together, these design decisions create a policy that balances strict device requirements with operational flexibility.
Conditional Access Design Principles Behind This Policy
Several well-established Conditional Access design principles are visible in this configuration. The first is the concept of layered trust signals. Identity, device posture, and access method are all evaluated together before access is granted.
Another principle is broad application coverage. Instead of protecting a single application, the policy applies consistent device trust requirements across the organization’s application environment.
The policy also demonstrates the principle of scalable policy management through group-based targeting. This allows administrators to manage policy scope dynamically without modifying the policy configuration itself.
These design principles reflect a mature Conditional Access architecture where security decisions are centralized, consistent, and based on multiple contextual signals.
Final Thoughts
Conditional Access compliant device policies represent a critical step toward a modern Zero Trust access model. They ensure that access decisions are based not only on who the user is but also on the security posture of the device being used.
This particular design focuses on Windows and macOS devices and evaluates access through both browsers and modern authentication clients. By requiring devices to be compliant or domain joined, the organization ensures that only trusted systems interact with corporate applications.
The result is a security model that remains flexible for users while maintaining strong protections for enterprise resources.
Policies like this demonstrate how Conditional Access transforms identity security into a dynamic decision engine that evaluates trust at every sign-in.