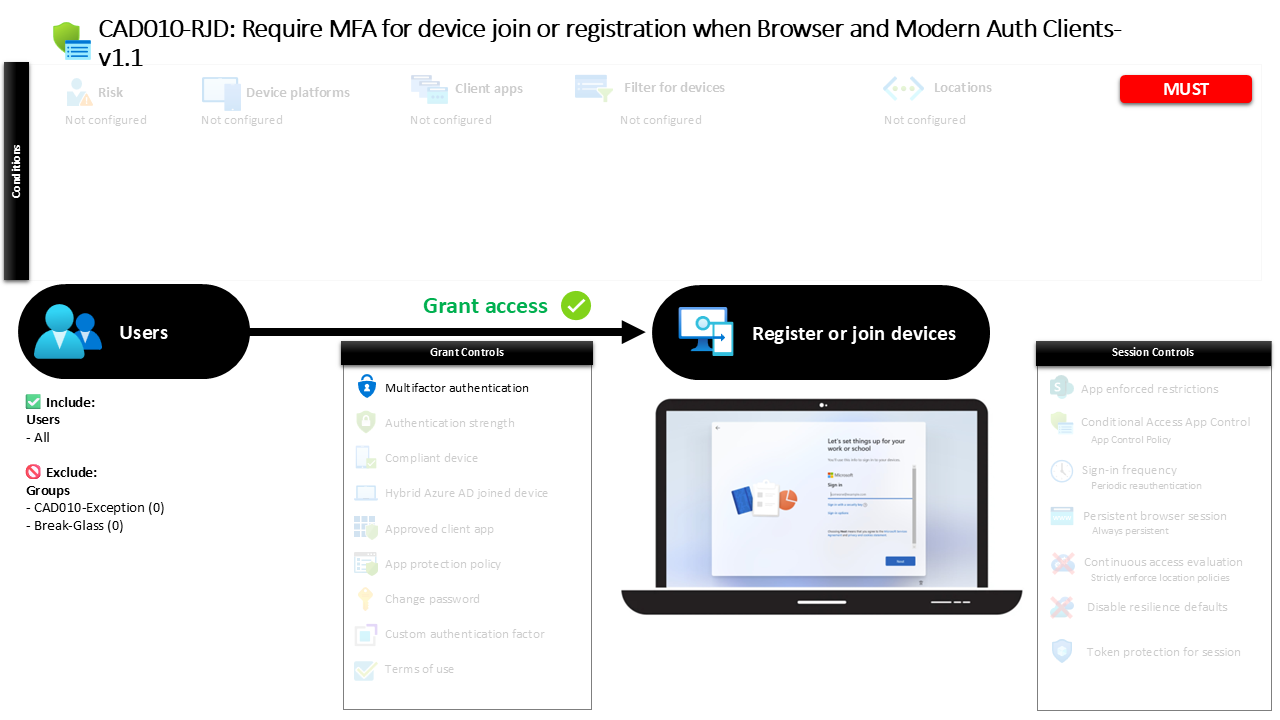
Conditional Access Device Registration MFA CAD010-RJD Require MFA for device join or registration when Browser and Modern Auth Clients
Introduction
Conditional Access device registration security often becomes important when organizations begin allowing employees to enroll devices into their identity environment. Device join and registration are powerful capabilities in Microsoft Entra ID because they establish trust between a device and the organization’s identity platform. If that process happens without strong identity verification, an attacker who compromises credentials could potentially register their own device and gain persistent access.
This Conditional Access device registration policy introduces a simple but important protection: before a device can be joined or registered, the user must verify their identity with multifactor authentication. By placing identity verification at the start of the device trust lifecycle, the organization ensures that only authenticated and verified users can attach devices to the directory.
The design reflects a common Conditional Access principle. Identity must be verified before trust is extended to a device. This policy ensures that device registration is not treated as a routine user action, but as a security-sensitive operation that requires stronger authentication assurance.
This Policy in One Line
This Conditional Access device registration policy requires multifactor authentication when users attempt to join or register a device with Microsoft Entra ID.
What This Conditional Access Policy Does
This Conditional Access device registration policy evaluates sign-in activity when a user attempts to perform the device registration action within Microsoft Entra ID. Instead of targeting traditional applications, the policy focuses on the user action associated with registering or joining a device to the directory.
When this event occurs, Conditional Access evaluates the request and applies an authentication requirement. The configuration requires multifactor authentication before the registration process can proceed. This means the user must successfully complete an additional verification step beyond their password.
From a security perspective, the policy places a strong identity validation checkpoint at the exact moment when a device attempts to establish trust with the organization. Device registration becomes a controlled operation rather than an automatic process.
By requiring MFA at this stage, the policy ensures that only verified users can bind devices to the identity environment. This strengthens the reliability of device identities that later participate in access decisions across Microsoft 365 and other integrated services.
Who the Policy Applies To
The policy is configured to apply broadly across the organization’s user population. All users fall within scope for this Conditional Access device registration control. When any user attempts to perform the device registration action, Conditional Access evaluates the request.
The configuration also defines exclusion groups. These groups are excluded from the policy scope. Because identifiers cannot be interpreted as meaningful names from the configuration alone, the article does not attribute a specific purpose to them.
In many Conditional Access designs, exclusion groups are used to support controlled exception management. Organizations commonly use these groups for break-glass access, administrative recovery scenarios, or temporary operational exceptions. Using groups rather than individual user exclusions allows security teams to manage exceptions through approval processes or time-based access workflows.
This approach aligns with strong Conditional Access design principles. Policies remain broadly enforced, while exception handling remains structured, traceable, and centrally managed.
What Apps and Services the Policy Protects
This Conditional Access device registration policy does not target a traditional application or cloud service. Instead, the policy focuses on a specific user action related to identity lifecycle management: registering or joining a device with Microsoft Entra ID.
The device registration process establishes a relationship between a user, a device, and the directory. Once a device is registered or joined, it can participate in other identity and access decisions, including device-based Conditional Access evaluations.
Because device trust becomes part of the broader access control model, protecting the registration process is critical. By targeting the device registration action directly, this policy ensures that identity verification occurs exactly when the trust relationship is created.
This design prevents unauthorized or unverified device enrollments and strengthens the integrity of the device identities that the organization later relies on for access decisions.
Platforms, Devices, and Client Apps in Scope
The policy configuration evaluates requests originating from all client application types. This means Conditional Access evaluates device registration attempts regardless of whether the action originates from browser-based activity or modern authentication clients.
No specific device platforms are defined within the configuration. Because platform conditions are not present, the policy does not distinguish between operating systems or device types. Instead, the focus remains on the registration event itself rather than the device characteristics.
This approach reflects a straightforward security strategy. Rather than filtering based on device type, the organization ensures that the identity performing the registration is verified with multifactor authentication.
By keeping the conditions broad, the policy ensures consistent enforcement of identity verification across all environments where device registration may occur.
How Access Is Decided
Access decisions in this Conditional Access device registration policy are based on a single grant control. When the device registration action is detected, Conditional Access evaluates the policy and enforces a requirement for multifactor authentication.
The policy configuration uses a grant control that requires MFA. The logic ensures that the registration process cannot proceed until the user successfully completes an additional authentication factor.
This mechanism strengthens identity assurance at the moment of device trust creation. Even if a password is compromised, the attacker would still need to complete the multifactor authentication challenge in order to register a device.
In Conditional Access design, requiring MFA for high-impact identity events is a well-established principle. Device registration is one such event because it extends trust from the identity system to a physical endpoint.
What the User Experience Looks Like During Sign-In
From a user perspective, the Conditional Access device registration experience introduces an additional identity verification step during the enrollment process. When a user attempts to register or join a device, the request is evaluated by Conditional Access.
If the user falls within the policy scope, the system prompts them to complete multifactor authentication. This may involve approving a sign-in request through an authenticator application or completing another configured verification method.
Once the MFA requirement is satisfied, the device registration process continues normally. The device can then be successfully associated with the user and the directory.
The result is a user journey that remains familiar while quietly strengthening security. Users experience a brief identity verification step, while the organization gains higher confidence that the device enrollment event is legitimate.
Why This Policy Matters for Security and the Business
Device identities increasingly play a central role in modern access control strategies. Organizations rely on device registration to determine whether endpoints meet security requirements, participate in management frameworks, or qualify for trusted access scenarios.
Without strong protection at the moment of registration, the entire device trust model becomes vulnerable. A malicious actor who registers an unauthorized device could attempt to leverage that trust relationship in later access requests.
This Conditional Access device registration policy protects the first step in the device trust chain. By requiring multifactor authentication, the organization ensures that device enrollment begins with strong identity validation.
For the business, this translates into greater confidence in device-based access policies, reduced risk of unauthorized endpoint enrollment, and a stronger overall identity security posture.
Is This a Foundational or Must-Have Policy?
This Conditional Access device registration policy is commonly considered a foundational security control. Device join and registration are critical identity lifecycle events, and protecting them is widely recommended in modern identity security frameworks.
Because device registration establishes long-term trust relationships, it represents a high-value target for attackers. Requiring MFA at this point ensures that attackers cannot easily introduce unauthorized devices into the environment using compromised credentials.
For organizations adopting Conditional Access as part of a Zero Trust identity model, protecting device registration is often implemented early in the security architecture.
By enforcing strong identity verification during device enrollment, the organization ensures that device trust begins with a verified identity.
Important Design Choices and Things to Notice
One important design element of this Conditional Access device registration policy is its focus on the user action associated with registering a device. Instead of targeting applications, the policy protects a specific identity lifecycle event.
Another design decision is the broad scope of client application coverage. By evaluating all client app types, the policy ensures that the MFA requirement applies consistently regardless of how the registration process is initiated.
The use of exclusion groups is also notable. Rather than excluding individuals directly, the configuration relies on groups. This supports structured exception management and aligns with common Conditional Access operational practices.
Finally, the policy enforces a clear authentication requirement without layering additional conditions. This simplicity ensures predictable enforcement and reduces the risk of configuration conflicts with other access policies.
Conditional Access Design Principles Behind This Policy
Several Conditional Access design principles are reflected in this policy configuration. The most visible principle is identity verification before trust extension. Device registration extends trust to an endpoint, so the identity performing that action must be strongly verified.
Another principle is targeted protection of identity lifecycle events. Conditional Access policies are most effective when they focus on moments where trust relationships are created or modified.
The policy also reflects the principle of broad applicability with controlled exceptions. Applying the rule to all users ensures consistent protection, while exclusion groups allow organizations to manage operational scenarios that require temporary flexibility.
Together, these principles create a design that is both secure and manageable.
Final Thoughts
Conditional Access device registration policies play a crucial role in protecting the foundation of modern identity environments. Devices often become trusted participants in access decisions, making the registration process a critical security checkpoint.
By requiring multifactor authentication during device join or registration, this policy ensures that device trust begins with verified identity assurance. The configuration focuses on a single high-impact action and enforces a straightforward authentication requirement.
The result is a clean, predictable Conditional Access design that strengthens identity security without introducing unnecessary complexity.
In environments where device trust influences access to cloud services and corporate data, protecting the registration process is not optional. It is an essential step in building a resilient Microsoft Entra ID security architecture.