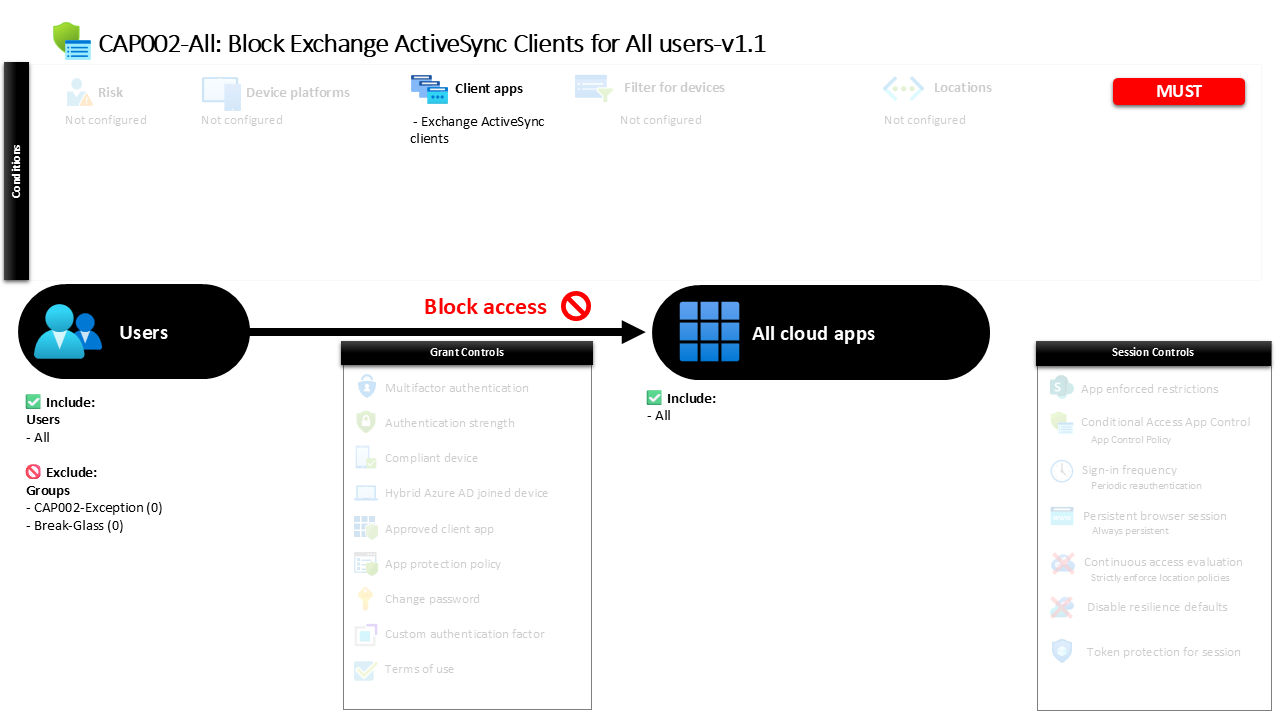
Conditional Access Exchange ActiveSync Block CAP002-All Block Exchange ActiveSync Clients for All users
Introduction
Conditional Access Exchange ActiveSync block policies exist for a simple but important reason. Many organizations still discover that mobile devices try to connect to email using older authentication protocols that were designed long before modern identity protection existed. These legacy connection methods bypass many of the security safeguards that modern identity platforms rely on, including stronger authentication checks and device-aware access decisions.
In real environments this often appears as an unnoticed risk. A user installs a generic mail client on a phone or tablet, enters their work email address, and the application attempts to synchronize mail through Exchange ActiveSync using legacy authentication flows. From a security perspective this can quietly create a path that avoids stronger identity verification mechanisms.
This Conditional Access Exchange ActiveSync block policy addresses that challenge directly. Instead of allowing these legacy synchronization attempts, the policy identifies Exchange ActiveSync client connections and prevents them from completing authentication. By doing so, the organization ensures that email access occurs through modern authentication paths that support stronger identity protection and Conditional Access controls.
This Policy in One Line
This Conditional Access Exchange ActiveSync block policy prevents users from accessing services through Exchange ActiveSync client connections.
What This Conditional Access Policy Does
The purpose of this Conditional Access Exchange ActiveSync block policy is to stop authentication attempts coming from Exchange ActiveSync client applications. These clients represent a specific category of connection method used primarily by older mobile email clients and legacy synchronization tools.
During the sign-in evaluation process, Conditional Access inspects the client application type used for authentication. When the system detects that the connection originates from an Exchange ActiveSync client, the policy condition is satisfied and the access evaluation moves to the configured grant control.
The configured control in this design blocks the authentication attempt entirely. This means the sign-in does not proceed, the session is not created, and the application cannot access any protected services.
From a security architecture perspective, the design communicates a clear policy decision: Exchange ActiveSync clients are not permitted as a valid access path. By enforcing this restriction through Conditional Access, the organization eliminates a category of legacy access that could otherwise weaken identity protections.
Who the Policy Applies To
This policy applies broadly to the entire user population. Conditional Access evaluates authentication attempts from all users when the connection originates from an Exchange ActiveSync client.
Applying the policy at this scope ensures consistent enforcement across the organization. Rather than relying on user-specific configuration or manual restrictions, the access decision is handled centrally by Microsoft Entra ID during the authentication process.
Two groups are excluded from enforcement. Organizations often maintain such exclusions to support controlled exception scenarios. For example, temporary access may be granted for legacy systems that cannot yet migrate to modern authentication methods, or for operational testing during security policy rollout.
In mature environments, these exception groups are typically governed through approval processes or time-limited access policies. This approach allows security teams to enforce strict default protections while still supporting controlled operational flexibility.
What Apps and Services the Policy Protects
The Conditional Access Exchange ActiveSync block policy protects access across the organization’s cloud application environment.
When Conditional Access evaluates an authentication request, it considers the target application that the user is attempting to access. In this configuration, the application scope includes the full set of cloud services that rely on Microsoft Entra ID for authentication.
This means that if an Exchange ActiveSync client attempts to authenticate in order to synchronize mailbox data or interact with services tied to the identity platform, the access request falls within the protection scope of this policy.
By applying the rule broadly to cloud services, the organization avoids the complexity of protecting individual workloads separately. Instead, the security control is placed at the identity layer. This reflects a common Conditional Access design principle where identity becomes the central enforcement point for access decisions across multiple services.
Platforms, Devices, and Client Apps in Scope
The defining condition in this policy is the client application type used during authentication.
Conditional Access classifies sign-in attempts based on how the application communicates with the identity platform. In this configuration, the policy specifically targets Exchange ActiveSync clients. These clients typically represent mobile email applications that rely on legacy synchronization mechanisms rather than modern authentication frameworks.
No restrictions are defined for device platforms or device state. Instead, the evaluation focuses exclusively on the client application type used during the sign-in attempt.
This design reflects a precise security objective. The policy is not attempting to control device compliance, operating system type, or location. Its sole purpose is to detect a specific legacy connection method and prevent authentication when that method is used.
By focusing on the client application condition alone, the policy keeps the security logic simple and predictable while addressing a known legacy authentication pathway.
How Access Is Decided
When a user attempts to authenticate, Microsoft Entra ID evaluates the sign-in against all relevant Conditional Access policies.
If the authentication request originates from an Exchange ActiveSync client, the client application condition in this policy becomes true. Once that condition is satisfied, Conditional Access proceeds to apply the configured grant control.
The grant control defined in this policy is a block action. This means that once the policy conditions are met, access is denied immediately. No additional authentication prompts are offered and the authentication session is not allowed to continue.
From a design standpoint, this reflects a strict security posture. The organization is not attempting to strengthen authentication for these clients or allow them under certain circumstances. Instead, the connection method itself is considered unacceptable and therefore completely prevented.
This approach is commonly used when organizations eliminate legacy authentication pathways as part of a broader identity modernization strategy.
What the User Experience Looks Like During Sign-In
From the user perspective, the experience is straightforward but deliberate.
A user installs a mobile email application that attempts to connect using Exchange ActiveSync. The application prompts the user to enter their corporate credentials and begins the authentication process.
When the request reaches Microsoft Entra ID, Conditional Access evaluates the sign-in and detects that the client application type matches Exchange ActiveSync. Because the policy blocks this client type, the authentication attempt fails.
The user typically sees an authentication failure message within the email client. The synchronization attempt does not proceed and the mailbox remains inaccessible through that application.
While this may initially appear as a technical failure to the user, the behavior is intentional. The policy prevents insecure connection methods so that users instead adopt supported applications that use modern authentication and integrate properly with Conditional Access protections.
Why This Policy Matters for Security and the Business
Legacy authentication protocols represent one of the most common identity attack surfaces in cloud environments. These protocols often lack support for modern authentication protections such as multifactor verification or advanced identity risk evaluation.
Exchange ActiveSync connections can be particularly problematic when used by older email clients. Because these clients were built around legacy authentication patterns, they may bypass stronger identity protection measures that organizations rely on today.
The Conditional Access Exchange ActiveSync block policy removes that risk by eliminating the connection method entirely. By doing so, the organization ensures that access to email and related services flows through authentication paths that support modern security controls.
For the business, the outcome is both improved security and simplified identity governance. Security teams gain confidence that legacy authentication channels are not silently bypassing modern identity protections.
Is This a Foundational or Must-Have Policy?
Policies that block legacy authentication methods are widely considered foundational within a modern Conditional Access architecture.
Legacy authentication paths are frequently targeted in identity-based attacks because they bypass advanced authentication protections. Removing these paths significantly reduces the available attack surface within the identity environment.
A Conditional Access Exchange ActiveSync block policy is therefore commonly implemented early in identity security programs. It establishes a baseline that prevents outdated connection methods while encouraging the adoption of modern client applications.
In many organizations, this type of policy forms part of a broader initiative to eliminate legacy authentication entirely and standardize all authentication flows on modern protocols that support Conditional Access evaluation.
Important Design Choices and Things to Notice
One notable design element is the use of a targeted client application condition rather than broader device or platform controls.
By focusing on the Exchange ActiveSync client type specifically, the policy avoids unintended impact on other authentication scenarios. Modern mobile email applications that use supported authentication frameworks are not affected by this rule because they do not authenticate through the Exchange ActiveSync client category targeted by the policy.
Another important design choice is the use of a direct block control. Rather than attempting to secure legacy authentication with additional requirements, the organization has determined that this access method should not be used at all.
This reflects a common Conditional Access design philosophy. When a technology path is known to weaken identity protections, the most effective control is often to remove that path entirely rather than attempting to compensate for its limitations.
Conditional Access Design Principles Behind This Policy
This policy illustrates several core principles of strong Conditional Access design.
First, security enforcement occurs at the identity layer. By evaluating authentication requests before access is granted, Microsoft Entra ID becomes the central decision point for whether a connection method is acceptable.
Second, the policy uses precise targeting. Instead of introducing broad restrictions that could affect multiple user scenarios, it focuses on a single legacy client type. This keeps the policy understandable and predictable.
Third, the design demonstrates a preventive security posture. Rather than waiting for suspicious behavior or risk signals, the policy removes a known weak authentication pathway in advance.
Together, these principles reflect a modern identity security approach where Conditional Access policies are used to proactively eliminate outdated access methods.
Final Thoughts
Legacy authentication paths often persist quietly in cloud environments long after modern identity protections have been deployed. Exchange ActiveSync connections are a common example, particularly when unmanaged mobile applications attempt to synchronize email using older protocols.
The Conditional Access Exchange ActiveSync block policy addresses that risk by ensuring that these legacy connection methods cannot authenticate successfully.
By enforcing this restriction centrally through Microsoft Entra ID, the organization protects access to its services while guiding users toward modern applications that integrate properly with Conditional Access protections.
In practice, policies like this represent an important step in building a resilient identity security architecture. Removing outdated authentication methods allows Conditional Access to operate as intended, ensuring that every successful sign-in is evaluated against the organization’s modern security standards.