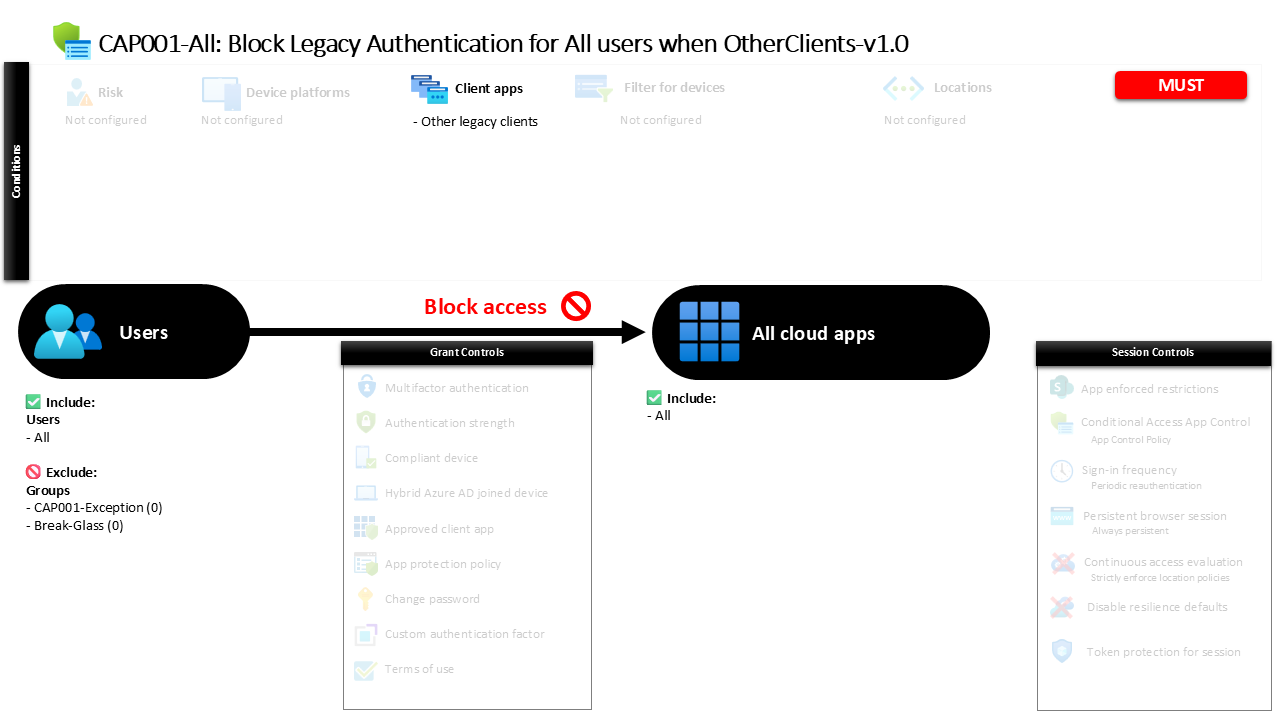
Conditional Access Legacy Authentication Block CAP001 All Block Legacy Authentication for All users when OtherClients
Introduction
Conditional Access legacy authentication block policies exist because many identity attacks still succeed through older authentication methods. Legacy protocols were designed in a different era of computing, long before modern identity protections like multifactor authentication or device evaluation became common. When attackers discover that a tenant still allows these older protocols, they often use automated password spray or credential stuffing attempts to gain access without triggering stronger security checks.
The Conditional Access legacy authentication block policy described here addresses exactly that risk. Instead of relying on users or applications to gradually stop using outdated protocols, the policy explicitly prevents sign-ins that originate from legacy client types. By doing so, the organization closes one of the most commonly exploited identity attack paths.
This design reflects a fundamental principle in modern Microsoft Entra ID security architecture. Organizations should not only strengthen authentication methods but also eliminate outdated ones entirely. Blocking legacy authentication ensures that only modern authentication flows can be used to access applications protected by Conditional Access.
This Policy in One Line
This Conditional Access legacy authentication block policy prevents all users from signing in to any application when the request originates from legacy client authentication methods.
What This Conditional Access Policy Does
The intention of this policy is simple but strategically important. It blocks authentication attempts that originate from legacy client types across all applications in the environment. Legacy authentication protocols typically include older technologies that do not support modern authentication mechanisms such as interactive identity verification or advanced security controls.
When a sign-in request reaches Microsoft Entra ID, Conditional Access evaluates several attributes of that request. One of those attributes is the type of client application attempting to authenticate. If the authentication attempt originates from a legacy client category, the request is evaluated by this policy.
Because the grant control configured for the policy blocks access, the authentication attempt is denied. This means the user cannot successfully authenticate using that legacy client method. Importantly, this restriction applies across the entire application landscape rather than targeting specific services.
From a security architecture perspective, this design ensures that all protected resources follow the same rule. Legacy authentication methods are simply not permitted as an entry point into the environment.
Who the Policy Applies To
This policy is designed to apply broadly across the user population. Conditional Access evaluates the identity attempting to sign in and determines whether the user falls within the scope defined by the policy configuration.
In this design, all users are included in the policy scope. That means every identity attempting to authenticate in the tenant is evaluated against the legacy authentication restriction. This approach reflects a security-first strategy where legacy authentication is not considered acceptable for any standard identity.
There are also specific user groups that are excluded from the policy scope. Organizations frequently use exclusion groups to support carefully controlled exceptions. These groups are often tied to administrative approval processes, temporary troubleshooting scenarios, or time-bound operational requirements.
By structuring exclusions through dedicated groups rather than modifying the policy itself, organizations maintain strong governance over exceptions. This allows security teams to monitor and manage deviations from the standard authentication model while still enforcing the policy for the broader identity population.
What Apps and Services the Policy Protects
A key design choice in this policy is the scope of protected applications. Instead of targeting a limited set of services, the policy evaluates access attempts to all applications.
This means that whenever a sign-in request occurs, Conditional Access checks whether the request involves legacy authentication and whether the user falls within the policy scope. If those conditions match, the block control is enforced regardless of which application the user attempted to access.
This broad scope is intentional. Legacy authentication risks do not exist only for a single application or service. Any workload that accepts authentication tokens could potentially be targeted if legacy protocols remain available.
By applying the restriction to every application, the organization ensures consistent protection across the entire environment. Security teams do not need to track which services might still allow legacy authentication because the policy eliminates that pathway universally.
From a design standpoint, this approach simplifies identity protection while significantly reducing the potential attack surface.
Platforms, Devices, and Client Apps in Scope
Conditional Access evaluates several contextual signals during sign-in, including device information, platform type, and the client application used to authenticate. In this particular policy design, the focus is placed specifically on the client application type.
The policy targets authentication attempts classified as legacy client applications. These clients fall into the category used for older authentication protocols that do not support modern identity protections.
No platform restrictions are defined, and the policy does not differentiate between device operating systems or device states. Instead, the enforcement decision focuses purely on the authentication method used by the client.
This design reflects a practical understanding of legacy authentication risk. The primary vulnerability lies in the protocol itself rather than the device or platform generating the request. A legacy authentication attempt is considered insecure regardless of whether it originates from a workstation, server, or other device type.
By centering the condition around client application type, the policy directly addresses the underlying security issue.
How Access Is Decided
During every authentication attempt, Microsoft Entra ID performs a sequence of evaluations to determine whether Conditional Access policies apply. This process begins by identifying the user, the application being accessed, and the characteristics of the authentication request.
For this policy, Conditional Access checks whether the sign-in request originates from a legacy client type. If the request matches that condition and the user falls within the policy scope, the policy proceeds to evaluate its access control configuration.
The configured control in this case blocks access. As a result, the authentication request is denied before the user can establish a session with the target application.
This decision happens automatically during the sign-in process. From the user’s perspective, the login attempt fails because the authentication method itself is not permitted.
This type of evaluation illustrates how Conditional Access acts as a real-time policy engine. It evaluates context and applies security decisions immediately during authentication.
What the User Experience Looks Like During Sign-In
When a user attempts to authenticate using a legacy client application, the experience is straightforward. The sign-in request is submitted to Microsoft Entra ID, but Conditional Access identifies the authentication method as belonging to the legacy client category.
Because the policy blocks that type of request, the authentication attempt does not succeed. The user cannot complete the sign-in process using that protocol.
In practical terms, users typically encounter this behavior when older applications or outdated email clients attempt to connect using legacy authentication methods. These clients were built before modern authentication standards became widely adopted.
Once the policy blocks the attempt, users must switch to applications that support modern authentication flows. Modern clients interact with Microsoft Entra ID in ways that allow Conditional Access to enforce stronger security requirements.
The experience reinforces an important security message. Access to applications must occur through modern authentication mechanisms that support identity protection.
Why This Policy Matters for Security and the Business
Legacy authentication remains one of the most common entry points for identity-based attacks. Because these protocols often bypass advanced identity protections, attackers actively search for environments where legacy authentication is still allowed.
Blocking legacy authentication closes that gap. It prevents attackers from using automated credential attacks through older protocols that cannot enforce modern security controls.
From a business perspective, this policy reduces the likelihood of unauthorized access to corporate applications. It also simplifies the identity security model by ensuring that all successful sign-ins use modern authentication.
Another important benefit is operational clarity. Security teams do not need to track which applications might still rely on legacy authentication. The policy establishes a consistent rule that applies across the environment.
This alignment between security enforcement and operational simplicity makes the policy both effective and sustainable.
Is This a Foundational or Must-Have Policy?
A Conditional Access legacy authentication block policy is widely considered a foundational identity protection control. It addresses a well-known security weakness that attackers routinely exploit in environments where legacy protocols remain enabled.
Because modern authentication standards are now widely supported across applications and services, organizations typically treat legacy authentication blocking as a baseline security requirement.
This policy establishes that baseline by enforcing a clear rule. Legacy authentication attempts are not permitted as a valid sign-in method.
In a broader Conditional Access architecture, this policy usually sits alongside other foundational controls that govern authentication strength, device compliance, and session behavior.
Together, these policies create a layered identity security framework where outdated and insecure authentication mechanisms are systematically removed.
Important Design Choices and Things to Notice
One of the most important design choices in this policy is its universal application scope. Instead of limiting enforcement to specific services or user segments, the policy targets all applications and nearly all users.
This decision reflects a clear security philosophy. Legacy authentication is not treated as acceptable for any standard user scenario.
Another notable design element is the use of exclusion groups. Rather than weakening the policy by modifying its scope, exceptions are managed through dedicated identity groups. This allows organizations to maintain strong security while still supporting controlled operational flexibility.
The policy also focuses exclusively on the client authentication type rather than layering additional conditions. This keeps the enforcement logic simple and highly predictable.
Simplicity is often a strength in Conditional Access design. Policies that address a single risk clearly are easier to maintain, audit, and understand.
Conditional Access Design Principles Behind This Policy
Several key Conditional Access design principles are visible in this policy.
First, it demonstrates the principle of eliminating insecure authentication paths. Rather than attempting to secure legacy protocols, the design removes them as a valid option entirely.
Second, the policy uses centralized enforcement. By applying the rule across all applications, the organization ensures consistent identity protection regardless of where a sign-in occurs.
Third, the design separates enforcement from exception management. The policy itself remains strict, while exclusions are handled through controlled identity groups.
These principles help maintain long-term security integrity. Conditional Access works best when policies are clear, narrowly focused, and consistently enforced across the environment.
Final Thoughts
The Conditional Access legacy authentication block policy represents one of the most effective ways to reduce identity attack exposure. Legacy protocols simply do not support the protections required for modern cloud identity security.
By preventing these authentication methods entirely, the organization ensures that every successful sign-in uses modern authentication standards that support Conditional Access evaluation.
In practice, this type of policy forms a critical part of a mature Microsoft Entra ID security architecture. It removes outdated entry points and reinforces a security model where identity protection is evaluated during every authentication attempt.
For organizations building a strong Conditional Access framework, blocking legacy authentication is not just a recommended step. It is a foundational design decision that significantly strengthens the overall identity security posture.