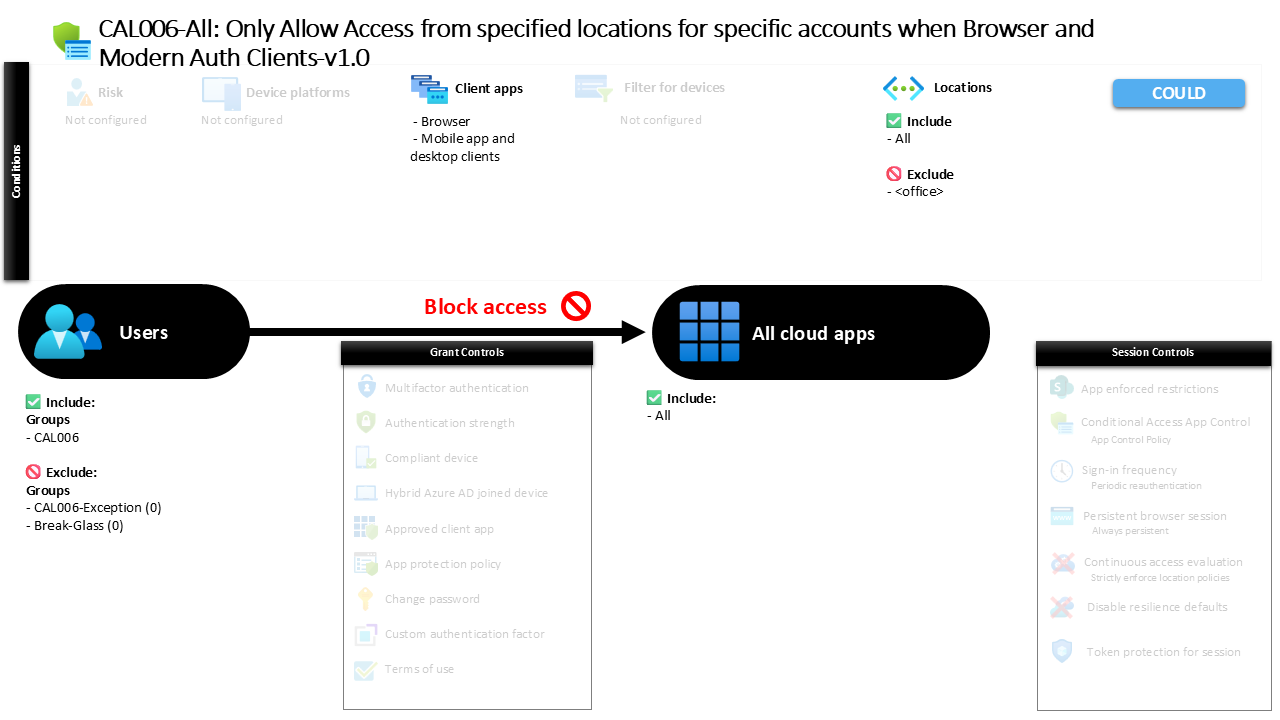
Conditional Access Location Restriction Policy CAL006 All Only Allow Access from specified locations for specific accounts when Browser and Modern Auth Clients
Introduction
Conditional Access location restriction is often introduced after organizations discover that identity alone is not enough to protect cloud resources. Even with strong authentication in place, attackers frequently attempt sign-ins from unfamiliar regions, anonymized networks, or infrastructure outside the organization’s trusted boundaries. Security teams therefore begin asking a simple question during architecture reviews: should certain sensitive accounts be able to sign in from anywhere in the world?
This Conditional Access location restriction addresses that concern directly. Instead of evaluating every possible device state or authentication method, the policy focuses on geography and network trust. When specific accounts attempt to access Microsoft cloud services, the sign-in location becomes the deciding factor. Access from trusted locations proceeds normally, while attempts from other locations are immediately blocked.
The result is a clean and predictable control. It narrows the attack surface by ensuring that sensitive accounts can only authenticate from approved networks, which is a foundational Zero Trust principle when protecting high-value identities.
This Policy in One Line
This Conditional Access location restriction blocks sign-ins for selected accounts when access attempts originate from locations outside an approved trusted network.
What This Conditional Access Policy Does
The design intention behind this Conditional Access location restriction is straightforward: allow normal access when sign-ins originate from a trusted location and prevent access from anywhere else. Instead of evaluating device compliance, authentication strength, or session behavior, the policy evaluates a single contextual signal during the sign-in process: the location from which the request originates.
When a user attempts to authenticate, Microsoft Entra ID evaluates the sign-in against the configured network locations. Because the policy includes all locations while excluding a specific trusted location, the logic effectively says that any connection originating outside that trusted boundary will trigger the control. Once that condition is met, the configured action is applied.
In this case the action is direct and decisive. The sign-in is blocked. No additional prompts, authentication challenges, or session restrictions are presented. Access simply does not proceed when the connection originates from an unapproved network location.
This design creates a clear perimeter for identity access, ensuring that location trust becomes a mandatory requirement for these accounts.
Who the Policy Applies To
The policy targets a defined group of accounts rather than the entire organization. This approach reflects a common Conditional Access design pattern where specific identities receive additional protection due to their elevated risk profile or operational sensitivity.
When users within the targeted group attempt to sign in, their authentication request is evaluated against the conditions defined in the policy. These users become subject to the location evaluation described earlier, meaning their access is dependent on whether the connection originates from a trusted network.
At the same time, the policy deliberately excludes certain groups from the evaluation. Organizations commonly use exclusion groups to support controlled exception management through approval workflows or time-based access scenarios. For example, administrators may temporarily place accounts in an exclusion group during troubleshooting, migration activities, or emergency operations.
This layered targeting approach allows security teams to apply strict location-based access control while maintaining operational flexibility when legitimate exceptions are required.
What Apps and Services the Policy Protects
The policy protects access across all cloud applications integrated with Microsoft Entra authentication. Instead of limiting the restriction to a single service, the configuration applies the location requirement broadly across the Microsoft identity ecosystem.
During sign-in evaluation, Microsoft Entra does not distinguish between different applications when applying this policy. Whether a user attempts to access collaboration services, administrative portals, or other cloud resources, the same location condition is evaluated.
This broad scope reflects a deliberate security design decision. By applying the restriction across all applications, the policy prevents attackers from bypassing location controls through alternative entry points. Every authentication request initiated by the targeted accounts is evaluated consistently.
From a security architecture perspective, this approach reinforces the principle that identity access boundaries should be enforced centrally at the authentication layer rather than individually within each application.
Platforms, Devices, and Client Apps in Scope
The Conditional Access location restriction specifically evaluates sign-ins performed through browsers and modern authentication clients. These client types represent the majority of modern cloud access scenarios, including web-based access and applications that use contemporary authentication protocols.
When a user signs in through a browser, the authentication request is processed through Microsoft Entra and evaluated against the configured location rules. Similarly, modern desktop and mobile applications that use modern authentication protocols are also subject to the same evaluation.
Because the policy focuses on these modern authentication pathways, it ensures that the most common cloud access methods are covered by the location control. This design ensures that both web sessions and application-based sign-ins must originate from the trusted location.
The result is consistent enforcement across typical access patterns, preventing attackers from bypassing location restrictions simply by switching client types.
How Access Is Decided
Access decisions within this Conditional Access location restriction are determined by a simple but powerful evaluation process. During every authentication attempt, Microsoft Entra inspects the source location of the sign-in request and compares it to the configured trusted location list.
If the sign-in originates from the trusted network location defined in the policy, the condition that triggers the restriction is not met. Authentication continues normally and the user gains access to the requested application.
If the sign-in originates from any other location, however, the policy condition is satisfied. Because the configured control is a block action, the authentication process stops immediately and the user is denied access.
This approach reflects one of the strongest enforcement methods available in Conditional Access. Instead of introducing additional authentication steps or session restrictions, the system simply prevents access when the contextual signal indicates risk.
From a design perspective, it transforms network location into a decisive access boundary.
What the User Experience Looks Like During Sign-In
From the user’s perspective, the experience of this Conditional Access location restriction is predictable and easy to understand. When users sign in from the approved network location, the authentication process appears completely normal. No additional prompts appear, and access proceeds as expected.
However, when the same user attempts to authenticate from a different location, the experience changes immediately. The sign-in request is evaluated by Conditional Access and the restriction is triggered because the connection does not originate from the trusted network.
Instead of continuing with authentication, the user receives a message indicating that access has been blocked due to organizational policy. The application session never begins, and no authentication challenge is offered to bypass the restriction.
This clear user experience reinforces the policy’s intention: access for these accounts is location-bound and cannot occur from outside the trusted network boundary.
Why This Policy Matters for Security and the Business
Location-based Conditional Access policies play an important role in protecting sensitive identities. Even in environments with strong authentication practices, attackers often attempt to authenticate from infrastructure that sits outside normal organizational network patterns.
By restricting where authentication can originate, the organization dramatically reduces the likelihood that compromised credentials can be used successfully. Even if an attacker obtains valid credentials, they would still need access to the trusted network location to proceed.
For security teams, this adds a powerful contextual barrier to identity compromise. For the business, it provides assurance that critical accounts cannot be accessed from unknown or uncontrolled networks.
In environments where certain identities are expected to operate only within known network boundaries, location restriction becomes one of the simplest and most effective protections available.
Is This a Foundational or Must-Have Policy?
This Conditional Access location restriction is typically considered a specialized protection rather than a universal baseline control. Many organizations apply it selectively to identities that require stronger protection due to their operational importance or elevated privileges.
For these accounts, restricting sign-in locations significantly reduces exposure to external credential abuse. The control is particularly valuable when accounts are expected to operate primarily from corporate networks or controlled environments.
While not every user account requires this level of restriction, the policy becomes a strong defensive layer for high-value identities. In a mature Conditional Access strategy, location restrictions often complement other protections such as strong authentication requirements and device-based access policies.
Together, these controls create multiple layers of verification before access is granted.
Important Design Choices and Things to Notice
One of the most notable design choices in this Conditional Access location restriction is the use of a trusted location exclusion model. Instead of explicitly allowing access only from specific locations, the configuration includes all locations while excluding the trusted network.
This structure effectively turns the policy into a protective barrier around the trusted location. Sign-ins from the trusted network are permitted, while any attempt from elsewhere automatically triggers the restriction.
Another important detail is the focus on modern authentication clients and browsers. Because most modern cloud access occurs through these mechanisms, targeting them ensures that the policy covers the majority of authentication pathways.
Finally, the use of group targeting and exclusion groups demonstrates a thoughtful operational design. It allows administrators to enforce strict location controls while still maintaining a controlled mechanism for exceptions when operational needs arise.
Conditional Access Design Principles Behind This Policy
Several key Conditional Access design principles are visible in this policy. The first is contextual access control. Instead of relying solely on identity verification, the policy evaluates the context of the authentication request, specifically its origin location.
The second principle is layered identity protection. By restricting where authentication can occur, the organization adds an additional barrier beyond credentials and authentication factors.
Another principle present in the design is centralized enforcement. Because the restriction is applied at the identity platform level, it protects all applications that rely on Microsoft Entra authentication without requiring individual application configuration.
Finally, the policy demonstrates the principle of targeted enforcement. Rather than applying strict restrictions across the entire organization, the control focuses on accounts where the risk and impact justify stronger protection.
These principles together illustrate how Conditional Access can be used to build practical and effective security architecture.
Final Thoughts
Conditional Access location restriction is one of the clearest examples of contextual identity security. By making network location a determining factor in authentication decisions, organizations can dramatically reduce the exposure of sensitive accounts to external threats.
This policy demonstrates how a simple configuration can enforce a strong access boundary. When sign-ins originate from the trusted network location, users work normally. When they originate from anywhere else, access stops immediately.
In a broader Conditional Access strategy, controls like this complement authentication and device policies to create layered protection for identity. The result is an access model where identity alone is no longer enough. Context matters, and location becomes part of the decision that determines whether access is granted.